TA446 uses leaked DarkSword iOS kit in phishing campaign against high-value targets
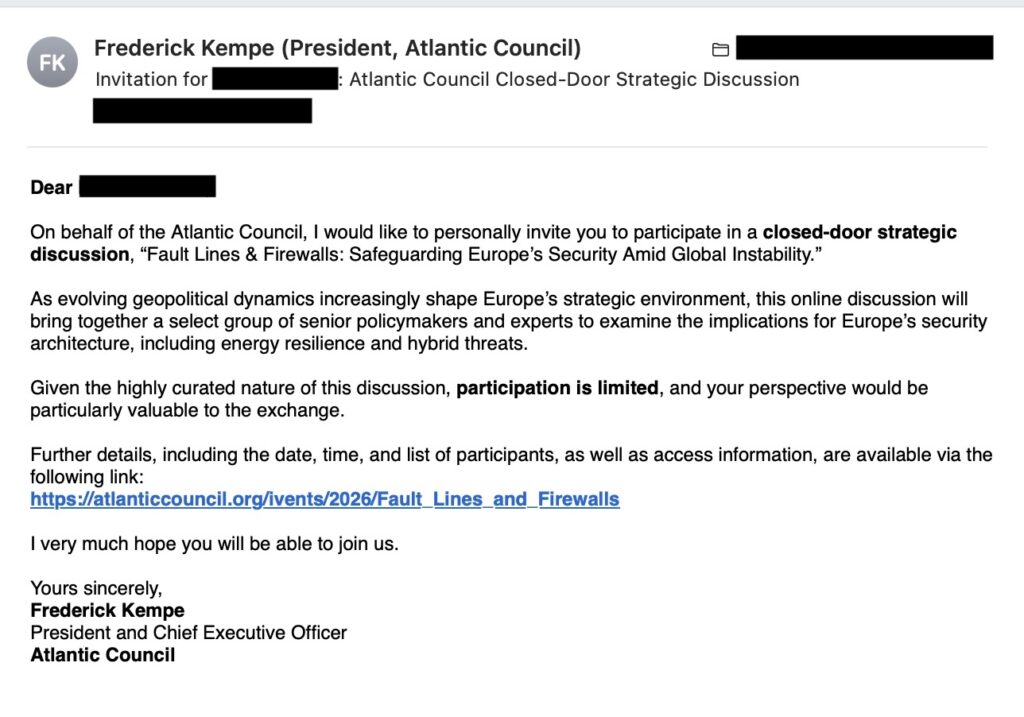
Russia-linked threat group TA446 has started using the leaked DarkSword iOS exploit kit in a targeted spear-phishing campaign, marking a major shift for an actor long known for credential theft rather than direct iPhone exploitation. Security researchers say the campaign used spoofed Atlantic Council emails sent on March 26, 2026, and aimed to deliver GHOSTBLADE malware to iOS devices.
TA446 is widely tracked as Callisto, COLDRIVER, and Star Blizzard, and public reporting has long linked it to Russian state interests. In this latest wave, Proofpoint said the actor used fake “discussion invitation” emails, while server-side filtering appeared to send only iPhone users toward the real exploit path. Automated analysis instead received a benign decoy PDF, which suggests the operators tried hard to avoid exposure in sandboxes and security tools.
The campaign matters because DarkSword only leaked publicly a few days earlier, after samples appeared on GitHub and triggered warnings across the mobile security industry. That rapid adoption shows how quickly advanced iPhone exploit tooling can move from a specialized capability into real-world operations.
A new step up for TA446
Researchers say TA446 had not previously shown a clear pattern of targeting Apple devices or iCloud accounts. Proofpoint’s public statement said the group’s use of DarkSword gave it a new way to go after iOS users directly, instead of relying only on standard phishing and credential theft.
One known recipient was Leonid Volkov, a prominent Russian opposition figure and political director of the Anti-Corruption Foundation, which underlines the campaign’s political and intelligence value. Proofpoint also said the broader targeting in this wave reached government, think tank, higher education, financial, and legal organizations, making it wider than TA446’s usual narrow focus.
Proofpoint also said TA446 email volume had risen sharply over the prior two weeks. Some of those messages reportedly delivered the MAYBEROBOT backdoor through password-protected ZIP files, while the March 26 activity used links instead of attachments to steer victims toward the DarkSword chain.
Campaign snapshot
| Item | Verified detail |
|---|---|
| Threat actor | TA446, also known as Callisto, COLDRIVER, and Star Blizzard |
| Campaign date observed | March 26, 2026 |
| Main lure | Fake Atlantic Council “discussion invitation” emails |
| Target device type | iPhones and other iOS devices |
| Exploit kit used | DarkSword |
| Malware mentioned | GHOSTBLADE, with other recent TA446 activity using MAYBEROBOT |
| Likely delivery control | Server-side filtering that served a decoy PDF to non-target analysis environments |
Why DarkSword changes the threat picture
DarkSword already raised alarms when Lookout disclosed it on March 18 as a sophisticated full iOS exploit chain and infostealer. Lookout described it as evidence that advanced mobile exploitation is no longer limited to rare espionage use and can increasingly support broader financially motivated or mixed-purpose attacks.
Reuters reported that DarkSword had already been used against iPhone users running iOS 18.4 to 18.6.2 who visited compromised Ukrainian websites. Later reporting showed that leaked GitHub samples made the kit easier for additional actors to adopt, especially against devices that had not moved to newer Apple software.
That context makes TA446’s move especially important. A group already skilled at high-trust phishing no longer needs to stop at stolen passwords if it can chain email lures into mobile exploitation. This appears to be one of the clearest early examples of a known state-linked phishing actor repurposing the leaked DarkSword kit in a live campaign.
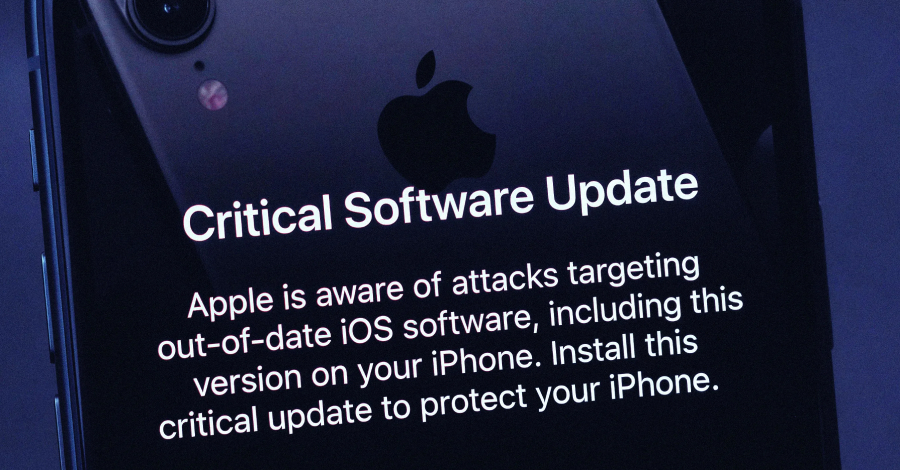
Apple’s response adds urgency
Apple has already patched many web-based attack paths tied to older iPhone software over time, and TechCrunch reported last week that Apple issued emergency updates on March 11, 2026, for devices that cannot run the latest major iOS branch. The same reporting said Apple had also begun warning users with older software to update because leaked exploit kits like DarkSword and Coruna increased the risk of broad abuse.
Apple’s official security documentation supports the broader point that customers should keep devices on current security releases, though Apple does not typically disclose exploit details before fixes are available. Apple’s deployment guidance also stresses that frequent updates are designed to keep devices protected.
For defenders, the lesson is simple. Mobile devices now sit inside the same threat path as email, identity, and web exploitation. Any organization that still treats iPhones as low-risk endpoints needs to revisit that assumption.
What security teams should do
- Patch iPhones and iPads to the latest supported Apple releases.
- Treat political, policy, and research-focused invitation emails as higher risk, especially when they include links instead of normal documents.
- Expand phishing monitoring to mobile endpoints, not just laptops and desktops. This is an inference based on the attack chain described by Proofpoint and Lookout.
- Review any traffic or threat intelligence tied to known TA446 infrastructure, including the second-stage domain linkage noted by Proofpoint.
- Consider stronger mobile protections for high-risk users such as journalists, dissidents, policy staff, researchers, and legal teams. This recommendation follows from the targeting pattern researchers described.
FAQ
TA446 is a Russia-linked threat actor also known as Callisto, COLDRIVER, and Star Blizzard. Researchers have long tracked it for targeted phishing and intelligence collection.
DarkSword is a sophisticated iOS exploit kit and infostealer disclosed by Lookout in March 2026. It later leaked publicly on GitHub, which increased concerns that more actors would use it.
Proofpoint said attackers sent fake Atlantic Council discussion invitations. If the victim matched the right conditions, the infrastructure appears to have served the DarkSword chain instead of a harmless decoy PDF.
Proofpoint said the targeting included government, think tank, higher education, financial, and legal entities. One known recipient was Leonid Volkov.
The reporting I found says there was no evidence that sandbox escapes were delivered in the observed infrastructure.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages