The Gentlemen Ransomware Gang Expands Attacks With SystemBC Botnet

The Gentlemen ransomware operation is expanding its attack toolkit with SystemBC, a proxy malware often used to hide malicious traffic and support post-compromise activity inside corporate networks. Check Point Research says a command-and-control server linked to a Gentlemen affiliate exposed telemetry from more than 1,570 infected systems, most of them likely tied to companies and organizations.
The finding suggests The Gentlemen is moving beyond a smaller ransomware operation and building a more mature criminal ecosystem. The group already claims more than 320 victims since emerging in mid-2025, with 240 of those attacks recorded in 2026 alone.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Security teams should treat this as a warning about speed and scale. Check Point says the group favors exposed internet-facing infrastructure such as VPNs, firewalls, and remote access gateways, then moves quickly once affiliates gain a foothold.
What Check Point found
During an incident response investigation, Check Point researchers found that a Gentlemen affiliate tried to deploy SystemBC on a compromised host. SystemBC can create SOCKS5 tunnels inside victim environments, which helps attackers route traffic, hide command-and-control activity, and deliver additional payloads.
The same investigation gave researchers visibility into a SystemBC command-and-control server. That server showed more than 1,570 infected systems worldwide, with the United States, the United Kingdom, and Germany among the most affected countries.
Check Point says it cannot yet prove whether SystemBC has become part of The Gentlemen’s core ransomware ecosystem or whether one affiliate used it in a separate intrusion. Still, its use alongside Cobalt Strike shows how affiliates can combine known tools into a fast and effective attack chain.
Key details at a glance
| Item | Details |
|---|---|
| Threat group | The Gentlemen ransomware-as-a-service |
| First observed | Around mid-2025 |
| Claimed victims | More than 320 |
| 2026 activity | Around 240 claimed attacks |
| Newly observed tool | SystemBC proxy malware |
| Botnet size seen by researchers | More than 1,570 infected systems |
| Main victim profile | Corporate and organizational environments |
| Common entry points | VPNs, firewalls, remote access gateways |
| Affected platforms | Windows, Linux, NAS, BSD, and ESXi |
Why SystemBC matters
SystemBC gives attackers a covert tunnel into compromised networks. That matters because ransomware attacks no longer rely only on dropping an encryptor. Modern affiliates often need remote access, credential theft, lateral movement, data theft, and payload staging before encryption starts.
In the incident analyzed by Check Point, the attacker already had Domain Admin-level access when the earliest confirmed activity began. From there, the affiliate validated credentials, moved across systems, deployed Cobalt Strike payloads through RPC, and staged ransomware from internal infrastructure.
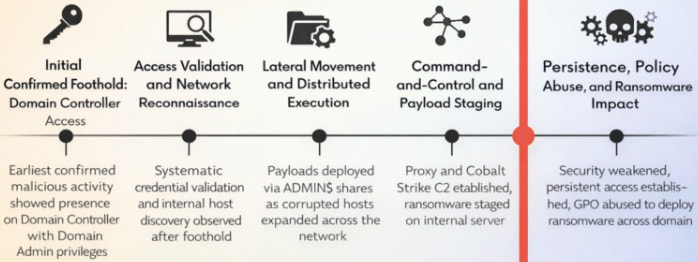
Source: Check Point
The attacker also used built-in Windows mechanisms, including Group Policy, to trigger near-simultaneous ransomware execution across domain-joined machines. This shows why domain controller compromise remains one of the most dangerous stages in a ransomware intrusion.
How the attack chain worked
The attack chain seen by Check Point followed a familiar but dangerous pattern:
- The attacker operated from a Domain Controller with Domain Admin privileges.
- Credentials were tested across the environment.
- Reconnaissance commands checked users, systems, and directories.
- Cobalt Strike payloads were pushed to remote machines.
- SystemBC was staged to support proxy-based command-and-control.
- The ransomware payload was hosted internally.
- Group Policy helped launch encryption across domain-connected systems.
Check Point says the ransomware uses a hybrid encryption design based on X25519 and XChaCha20. Smaller files under 1 MB are fully encrypted, while larger files are partially encrypted in chunks to speed up the attack.
Before encryption, the malware targets databases, backup tools, virtualization processes, Shadow Copies, and logs. The ESXi version can also shut down virtual machines so their disks can be encrypted.
Why The Gentlemen is growing fast
The Gentlemen runs as a ransomware-as-a-service operation, meaning the core developers provide infrastructure and tools while affiliates carry out attacks. Check Point says the group offers affiliates a 90% share of ransom payments, compared with the more common 80% split used by many rival operations.
That model can attract experienced attackers who already know how to break into corporate networks. A better payout gives them a reason to switch programs or test a newer brand.
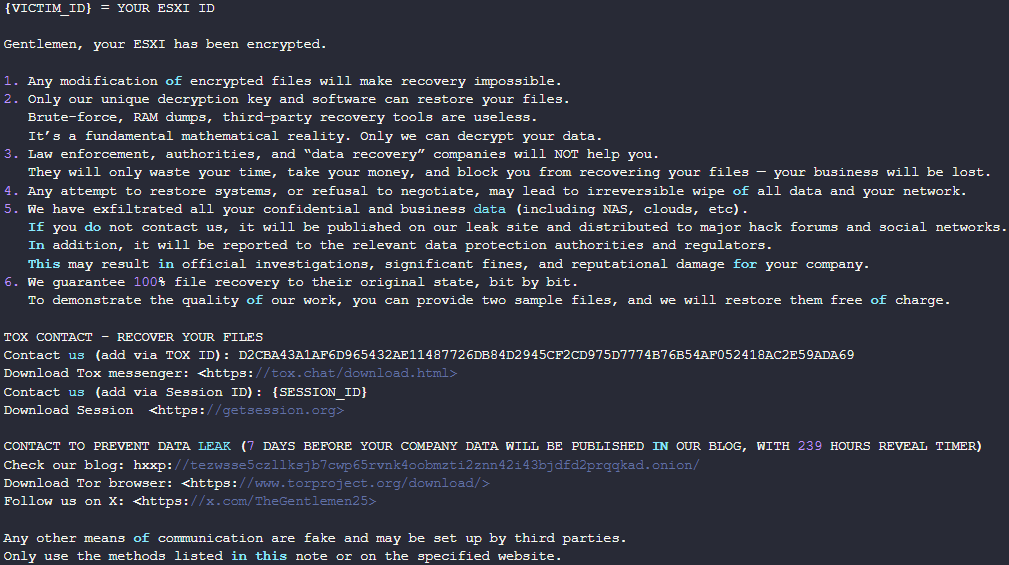
Source: Check Point
The group also provides a broad locker set. Check Point says The Gentlemen offers Go-based lockers for Windows, Linux, NAS, and BSD systems, plus a C-based locker for ESXi hypervisors.
Who is being targeted
Check Point describes The Gentlemen’s attacks as largely opportunistic. The group looks for exposed and vulnerable internet-facing systems instead of focusing only on one industry or country.
Manufacturing and technology companies appear most frequently among victims, while healthcare has become a growing third target. That is notable because some ransomware groups avoid hospitals and critical care providers to reduce pressure from law enforcement.
The geography also points to a broad campaign. Check Point says the United States has the highest number of victims, followed by the United Kingdom and Germany, with other affected regions also visible in the SystemBC telemetry.
What defenders should prioritize
Organizations should focus first on exposed systems that attackers can reach from the internet. VPN appliances, firewall portals, and remote access gateways need fast patching, strict access rules, and continuous monitoring.
Security teams should also assume that credential theft will follow soon after initial access. Strong multi-factor authentication, privileged access controls, and alerts for abnormal domain admin activity can slow attackers before they reach the ransomware stage.
Backups need extra attention. The Gentlemen’s tooling tries to disrupt backup and recovery paths, so companies should test isolated backups before an incident, not during one.
Key actions include:
- Patch VPNs, firewalls, and remote access gateways quickly.
- Restrict administrative access to domain controllers.
- Monitor for Cobalt Strike, SystemBC, Mimikatz, and unusual RPC activity.
- Segment networks to reduce domain-wide blast radius.
- Test offline or immutable backups.
- Review Group Policy changes and suspicious scheduled tasks.
- Hunt for unexplained outbound traffic to unknown command-and-control servers.
FAQ
The Gentlemen is a ransomware-as-a-service operation that appeared around mid-2025. It provides ransomware tools to affiliates who carry out attacks and share ransom payments with the operators.
SystemBC is proxy malware that creates encrypted tunnels inside infected environments. Attackers use it to hide traffic, move through networks, and deliver additional malware.
Check Point Research observed more than 1,570 victims connected to the relevant SystemBC command-and-control server.
Check Point says it has not confirmed that SystemBC is part of The Gentlemen’s core ecosystem. Researchers observed a Gentlemen affiliate using it during an incident response case.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages