The Gentlemen ransomware targets Windows, Linux, NAS, BSD, and ESXi with a new cross-platform playbook

A ransomware-as-a-service group known as The Gentlemen has expanded quickly since emerging around mid-2025, and researchers say it now offers lockers for Windows, Linux, NAS, and BSD systems, plus a separate C-based locker built for VMware ESXi. Check Point says the operation publicly claims more than 320 victims, with more than 240 of those claims appearing in the first months of 2026.
That mix makes the group more dangerous than a standard Windows-only ransomware crew. Affiliates can hit user systems, servers, storage devices, and virtualization infrastructure in the same campaign, increasing pressure on victims and reducing recovery options. Check Point says it observed the malware during an active incident response engagement and tied the intrusion to SystemBC, a proxy malware commonly used in hands-on ransomware operations.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The group also appears to run like a structured criminal service. Check Point says operators recruit affiliates on underground forums, provide access to private infrastructure, and publish victim names on a leak site when negotiations fail. The report also says the gang references an X account in its ransom note to publicly pressure victims.
What makes The Gentlemen stand out
The biggest difference is platform reach. Check Point says The Gentlemen’s main lockers are written in Go and support Windows, Linux, NAS, and BSD, while a separate locker written in C targets VMware ESXi. That gives affiliates a way to encrypt both endpoints and the virtual environment many companies rely on to run critical services.
The ESXi angle matters because hypervisors sit beneath many core workloads. If attackers can shut down virtual machines and encrypt the underlying data stores, recovery becomes slower and more disruptive. Check Point says the ESXi variant shuts down running virtual machines first, then begins encryption after releasing locks on the virtual disk files.
The operation also appears well-supported on the access side. Check Point says verified affiliates receive EDR-killing tools and private pivot infrastructure. In the case it investigated, the attackers deployed SystemBC, which CISA has previously described in ransomware intrusions as a proxy bot used to support follow-on attacker activity.
How the intrusion moved inside the network
Check Point says the earliest confirmed activity showed the attacker already on a domain controller with Domain Admin privileges. From there, the operators pushed Cobalt Strike payloads to remote systems through administrative shares using randomly named executables, then ran discovery commands such as systeminfo, whoami, and directory listings to map the environment.
That sequence matches established attacker tradecraft. MITRE ATT&CK documents SMB and Windows admin shares as a common way to move laterally, especially when adversaries already hold valid high-privilege credentials. MITRE also documents whoami as a standard discovery method used to identify user context and privileges.
Check Point says the ransomware can then spread through a built-in argument that accepts harvested domain credentials. It enumerates domain computers through Active Directory, checks which hosts are reachable, and delivers the locker through several parallel channels, including PsExec, WMI, remote scheduled tasks, remote services, and PowerShell-based execution. MITRE separately documents WMI and lateral tool transfer as established attacker techniques.
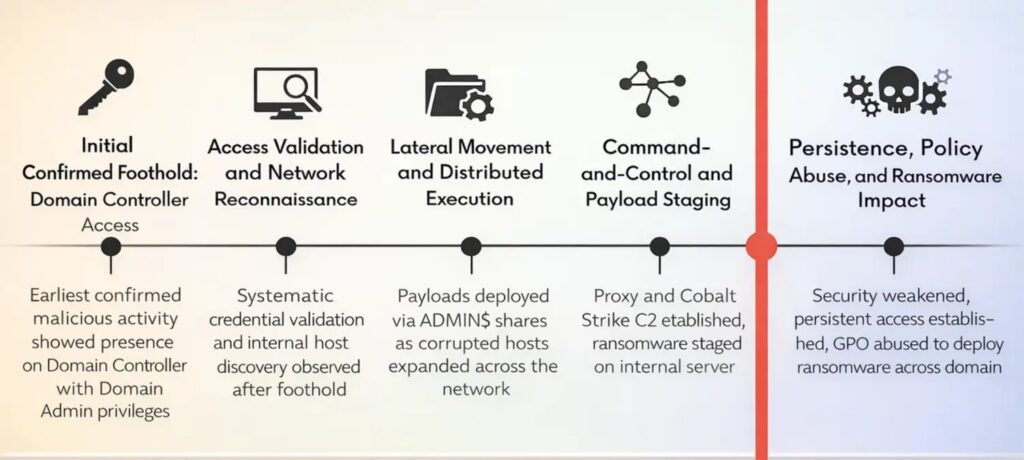
What happens before encryption
Before encryption starts, Check Point says the attackers disable Windows Defender, add broad exclusions for the full C: drive, shut down the firewall, re-enable SMB1, delete shadow copies, and wipe event logs. Those steps aim to reduce detection, weaken defenses, and make recovery harder.
The final deployment step is especially aggressive. Check Point says the operators abuse Group Policy Objects to push ransomware across every domain-joined machine at once. That lets the attack move from one privileged foothold to organization-wide encryption very quickly.
On ESXi, the malware also tries to blend in. Check Point says the locker copies itself to /bin/.vmware-authd, a path and name chosen to resemble a legitimate VMware daemon. MITRE classifies this kind of naming trick as masquerading, a defense-evasion tactic that helps malicious files look benign.
Why defenders should pay attention
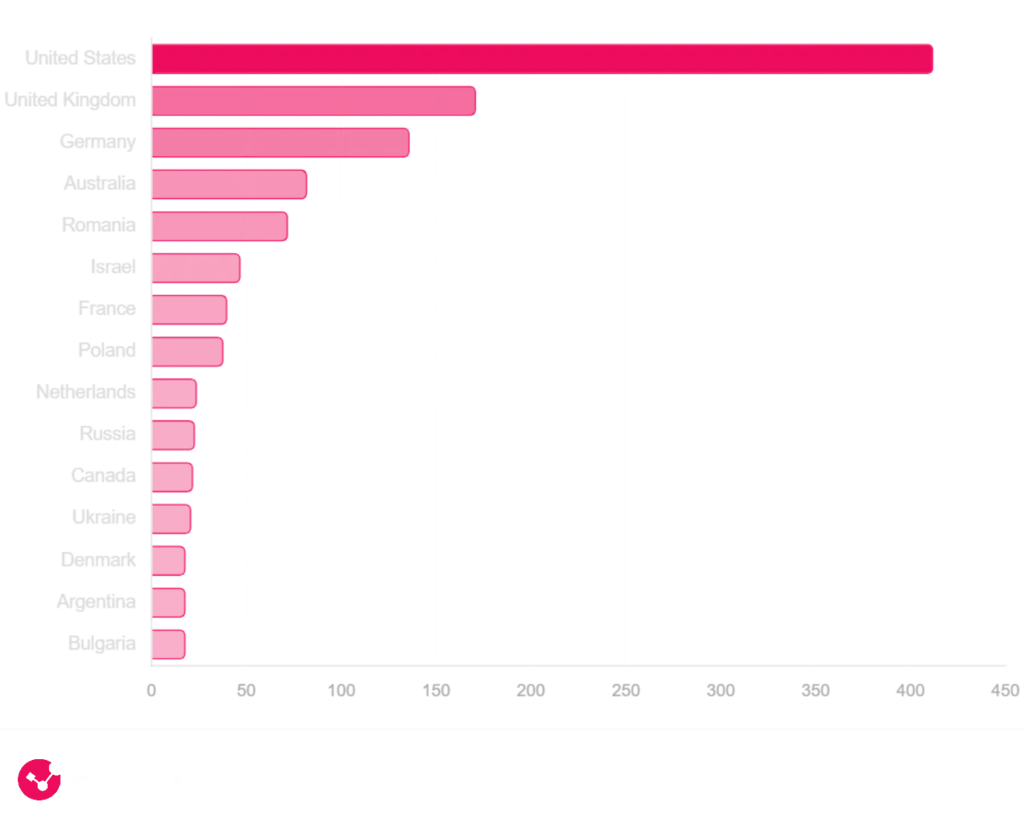
Check Point says telemetry from the related SystemBC command-and-control server showed more than 1,570 victims globally, with the United States accounting for the largest share, followed by the United Kingdom and Germany. The infection profile strongly suggested a focus on companies and organizations rather than opportunistic consumer targeting.
That scale matters because it suggests The Gentlemen is not a fringe operation testing one or two victims. It points to a broader affiliate model with enough access, tooling, and infrastructure to support repeated campaigns. The speed of the group’s public victim growth also suggests active recruitment and a working monetization model. This last point is an inference based on Check Point’s victim-count timeline and underground forum activity.
The use of SystemBC adds another warning sign. CISA’s updated Akira ransomware advisory says SystemBC serves as a proxy bot in ransomware operations, helping attackers maintain communications and move deeper into compromised environments. That does not tie The Gentlemen to Akira, but it does show that this malware remains a common and useful component in hands-on intrusions.
At a glance
| Element | What Check Point observed | Why it matters |
|---|---|---|
| Main ransomware family | The Gentlemen RaaS | Organized affiliate-driven operation |
| Supported platforms | Windows, Linux, NAS, BSD, ESXi | One campaign can hit many environments |
| Languages used | Go for most lockers, C for ESXi locker | Custom tooling for different targets |
| Access and staging | Domain controller access, Cobalt Strike, admin shares | Fast lateral spread from privileged foothold |
| Lateral movement | PsExec, WMI, scheduled tasks, services, PowerShell | Multiple delivery paths increase resilience |
| Recovery disruption | Defender disabled, firewall changed, shadow copies deleted | Slower recovery and weaker visibility |
| ESXi behavior | VMs shut down before encryption | Direct impact on virtual infrastructure |
Recommended actions
- Enforce MFA on administrative accounts and all remote access paths.
- Segment networks so a domain-level compromise cannot reach every server and hypervisor.
- Monitor for unusual use of admin shares, WMI, remote scheduled tasks, and service creation.
- Hunt for attempts to disable Defender, change firewall settings, re-enable SMB1, or delete shadow copies.
- Watch for suspicious binaries in user-writable paths and for files masquerading as VMware-related daemons on ESXi.
- Keep backups isolated or offline, because the ransomware actively targets recovery options and backup-related services.
FAQ
The Gentlemen is a ransomware-as-a-service operation that Check Point says emerged around mid-2025 and now supports attacks across Windows, Linux, NAS, BSD, and ESXi environments.
Because it targets VMware virtualization hosts directly. Encrypting ESXi systems can disrupt many virtual machines at once and make business recovery much harder.
Check Point says the operators used administrative shares, domain credentials, PsExec, WMI, scheduled tasks, services, and PowerShell-based methods. MITRE ATT&CK documents several of those as standard lateral-movement techniques.
SystemBC acts as a proxy malware component that can support attacker communications and follow-on operations. CISA has also noted its use in ransomware intrusions.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages