Top Node.js maintainers are under attack in a coordinated social engineering campaign

Open source developers behind some of the most widely used Node.js packages are facing a coordinated social engineering campaign that security researchers say closely mirrors the operation behind the recent Axios npm compromise. The campaign appears to focus on trusted maintainers who hold publishing access to packages used across developer tools, apps, and build pipelines worldwide.
Several well-known maintainers have now confirmed they were targeted. Socket says the list includes Feross Aboukhadijeh, Wes Todd, Matteo Collina, Scott Motte, Ulises Gascón, Pelle Wessman, and Jean Burellier, among others. These developers maintain or help maintain packages and projects such as WebTorrent, Lodash, Fastify, dotenv, Express, and Node.js core components.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The main goal appears simple. Attackers want control of a maintainer’s machine or session data so they can reach npm publishing credentials and push malicious package updates into the software supply chain. That pattern already surfaced in the Axios incident, where malicious versions 1.14.1 and 0.30.4 delivered a cross-platform remote access trojan.
How the scam works
This campaign does not rely on a rushed phishing email. Researchers say the attackers build trust over days or even weeks through LinkedIn messages, Slack invitations, and carefully staged business conversations that look ordinary at first glance.
In several reported cases, the victim was invited into a realistic Slack workspace and then pushed toward a video meeting. The meeting link often arrived just minutes before the call, and the page looked like Microsoft Teams or another real platform. Once the victim joined, the site displayed a fake problem and urged them to install software or run a terminal command.
If the target followed those steps, the attackers could deploy malware directly on the developer’s device. Security reporting on the Axios compromise says the malware could steal browser cookies, cloud credentials, keychain data, npm tokens, and other secrets, which makes normal two-factor authentication far less useful after infection.
Why this matters far beyond npm
This is not just a threat to a few maintainers. A single compromised publisher account can push malicious code into packages that millions of developers and companies install automatically through builds, updates, and dependency resolution. That is why the Axios attack drew such a strong response across the security industry.
Google Threat Intelligence Group attributed the Axios compromise to UNC1069, a North Korea linked threat actor, while Microsoft attributed related infrastructure and the compromise to Sapphire Sleet, another North Korean actor designation used by Microsoft. Both companies described the attack as part of a broader supply chain threat with downstream risk for enterprises.
Researchers also say this looks like a pivot from targeting crypto and finance victims one by one to targeting open source gatekeepers who can give attackers access at scale. That shift makes the campaign more dangerous because it turns trusted package maintainers into high-value supply chain entry points.
Confirmed names and what they maintain
| Maintainer | Reported by | Notable projects or roles |
|---|---|---|
| Feross Aboukhadijeh | Socket | WebTorrent, StandardJS, buffer, other widely used npm packages |
| John-David Dalton | Socket | Lodash creator |
| Wes Todd | Socket | Node Package Maintenance Working Group, Express TC |
| Matteo Collina | Socket | Fastify, Pino, Undici, Node.js TSC chair, Platformatic CTO |
| Scott Motte | Socket | dotenv creator |
| Ulises Gascón | Socket | Node.js collaborator, Express TC, Node.js Security WG contributor |
| Pelle Wessman | Socket | mocha, neostandard, npm-run-all2, type-fest maintainer |
| Jean Burellier | Socket | Node.js core collaborator, Express contributor |
What maintainers and teams should do now
Developers with npm publishing access should treat unexpected outreach like a live security issue, especially when a new contact pushes for a call, sends a last-minute meeting link, or asks for a software install. These attacks work because they look patient, polished, and normal.
Teams should also assume that device compromise breaks many familiar protections. Wes Todd warned that OIDC based publishing improves hygiene but does not stop a fully compromised machine, and Microsoft advised affected Axios users to rotate secrets immediately and pin safe versions
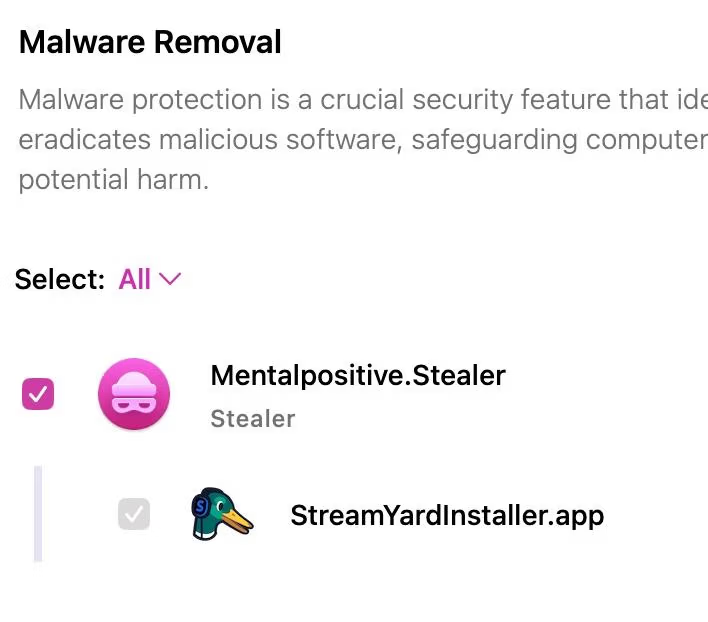
Security vendors and researchers now urge organizations to audit dependency trees, review build logs for malicious versions, search for suspicious outbound traffic, and pause risky auto-updates during active incidents. Those steps matter because the malicious Axios packages executed during install, not during normal app runtime.
Immediate red flags for maintainers
- A recruiter, marketer, or founder contacts you out of the blue and quickly moves the conversation to Slack.
- The meeting link arrives only minutes before the call.
- The page looks like Teams, Zoom, or StreamYard but asks you to install software to fix audio or video.
- You get asked to run a terminal command during a call.
- The outreach feels professional and slow-moving rather than urgent or sloppy.
FAQ
Google Threat Intelligence Group attributed the Axios supply chain attack to UNC1069. Microsoft linked the Axios compromise infrastructure to Sapphire Sleet. Public reporting ties the maintainer targeting campaign to the same broader operation, but different security vendors may use different actor names.
No. Socket says multiple other maintainers reported similar approaches after the Axios incident, including people tied to Fastify, dotenv, Lodash, Express, Node.js, and other major projects.
Because the malware steals active session data and credentials from the victim’s device after compromise. Once the attacker controls the machine or its authenticated sessions, 2FA may no longer block package publishing or account abuse.
Microsoft and Google both advise organizations to isolate affected hosts, rotate secrets, pin safe Axios versions, inspect dependency trees for plain-crypto-js, and review CI or developer systems for signs of compromise.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages