Transparent Tribe’s AI malware push shows how “vibeware” can overwhelm defenders

Transparent Tribe, also tracked as APT36, appears to have moved from relying mainly on familiar off-the-shelf malware to a faster, AI-assisted model that Bitdefender calls “vibeware.” In plain terms, the group seems to be using AI coding tools to generate many malware variants quickly, even if some of them are sloppy or incomplete. The danger is not polished code. The danger is scale.
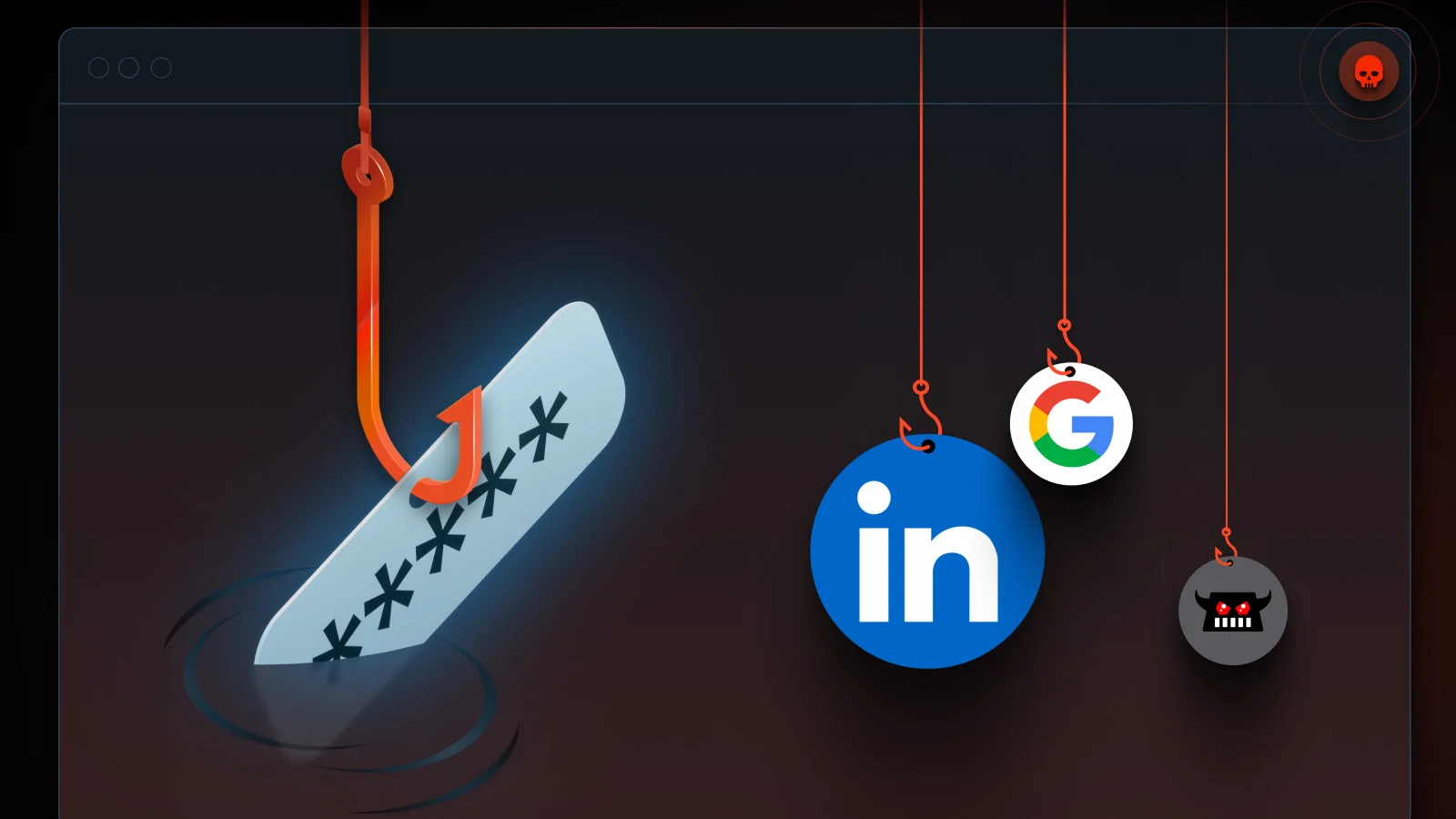
Bitdefender says this campaign primarily targets Indian government bodies, embassies, and military-linked entities, with secondary targeting tied to Afghanistan’s government and private businesses. The report also says investigators recovered evidence that the attackers used LinkedIn to profile potential victims, including staff connected to a military-related government agency.
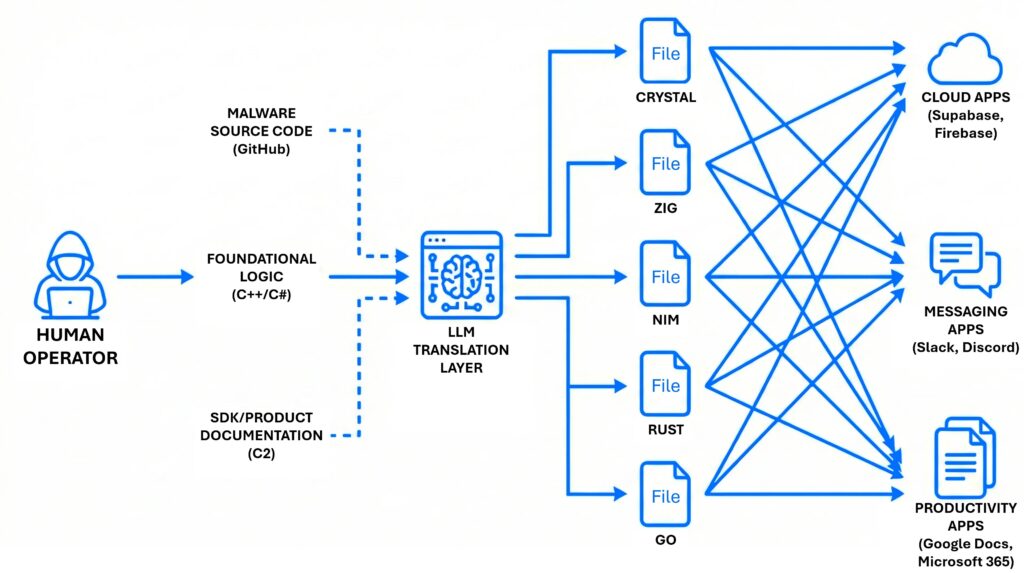
What makes this shift notable is the production model. Bitdefender describes a near-daily flow of fresh samples written across Nim, Zig, Crystal, Rust, Go, .NET, and C#, often paired with trusted cloud platforms such as Slack, Discord, Google Sheets, Supabase, Firebase, and Google Drive for command-and-control or data theft. That mix helps the malware blend into normal traffic and also pushes some security tools outside their usual comfort zone.
The broader AI angle also fits what Google Threat Intelligence Group has been tracking. In its February 2026 report, Google said it has not yet observed APT actors gaining breakthrough AI capabilities that fundamentally change the threat landscape, but it has seen threat actors use AI to speed up reconnaissance, phishing, malware development, and tool integration. That makes the APT36 case important because it looks less like a revolution and more like the industrialization of mediocre malware.
Why this campaign matters
This campaign suggests that AI-generated malware no longer needs to be elegant to be dangerous. If attackers can create many cheap variants, they only need one or two to slip through. Bitdefender calls this a form of Distributed Denial of Detection, where the goal is to overload defenders with volume, language diversity, and multiple fallback paths.
The report says some victims were hit with multiple implants at once, each using a different language or communication channel. If defenders block one path, another may stay alive. Bitdefender also says the hacking itself still appears to involve a human operator after the malware lands, so AI helps with volume and coding, while people still handle the intrusion work.
What Bitdefender found
| Area | What the report says |
|---|---|
| Threat actor | APT36 / Transparent Tribe |
| Main targets | Indian government, embassies, defense-linked entities |
| Secondary targets | Afghanistan government, private businesses |
| Delivery | Emails with ZIP or ISO archives containing .LNK files |
| Social engineering | Resume-themed PDF with a fake “Download Document” button |
| Languages used | Nim, Zig, Crystal, Rust, Go, .NET, C# |
| Trusted services abused | Slack, Discord, Google Sheets, Supabase, Firebase, Google Drive |
These findings come from Bitdefender’s March 5 report and related company materials summarizing the campaign. Bitdefender says it found metadata pointing to AI-integrated development tools and malware strings containing Unicode emojis, which it views as strong signs of AI assistance in the malware development pipeline.
How the attack chain works
Bitdefender says initial access likely starts with malicious email attachments. These messages may carry ZIP or ISO archives that hide Windows shortcut files, which can help the attackers bypass simple attachment filters.
One lure described in the report uses a PDF resume image with a large download button. When the victim clicks it, they get redirected to an attacker-controlled site that delivers the real archive. After that, the shortcut runs PowerShell in memory, downloads the main backdoor, and opens the door to a manual follow-up intrusion.
How “vibeware” hides in normal business traffic
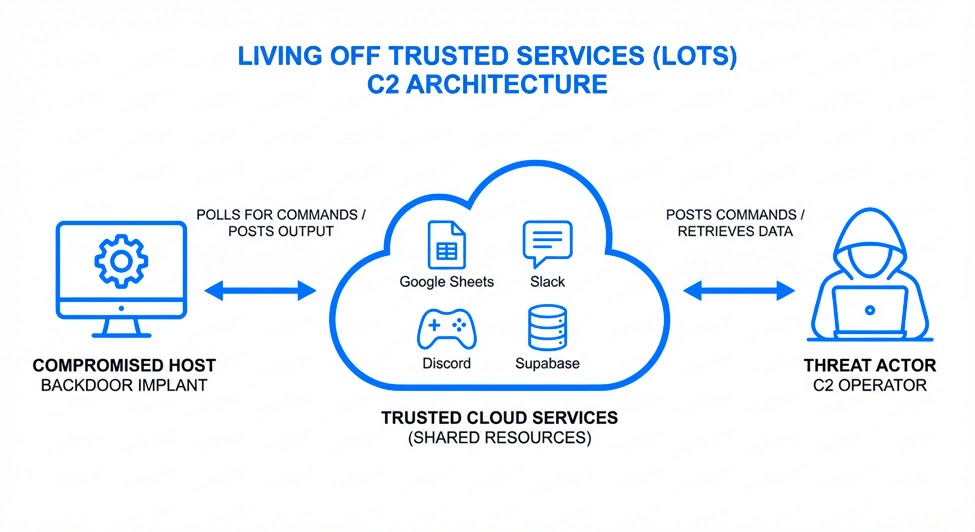
A big part of the campaign’s staying power comes from its abuse of services many organizations already trust. Bitdefender says the malware uses cloud platforms as control channels and as places to store stolen data or instructions. That makes detection harder because the traffic can look like ordinary enterprise activity.
Examples from the report include:
- Discord for command dispatch and output collection
- Slack for shell-style remote control
- Google Sheets as a live command hub
- Firebase and Supabase for data storage and coordination
- Google Drive for file uploads and exfiltration
Bitdefender says this “Living Off Trusted Services” approach works especially well with AI coding tools because these platforms have rich public documentation and SDKs. That gives coding assistants plenty of material to generate working integration code with little effort.
Why defenders should pay attention now
This campaign is a warning that defenders cannot rely only on file signatures or language-specific assumptions. Bitdefender says exotic languages can reset the detection baseline, while cloud APIs let malware traffic hide inside familiar domains and HTTPS sessions.
That means security teams should shift attention toward behavior. Unusual PowerShell, scheduled task creation, fileless execution, suspicious outbound connections from unsigned binaries, and unexpected use of trusted cloud services from unmanaged processes should all raise flags. Bitdefender says endpoint detection and response remains one of the strongest ways to catch this style of activity.
Defensive checklist
- Audit outbound connections to trusted cloud services from unsigned or unknown binaries.
- Hunt for suspicious scheduled tasks that mimic Microsoft or browser update jobs.
- Review PowerShell logs for in-memory execution chains and download cradles.
- Expand detections beyond common malware languages such as C++ and C#.
- Treat linked PDF lures, ZIP files, ISO files, and
.LNKattachments as high-risk in spear-phishing workflows.
FAQ
Bitdefender uses the term to describe AI-assisted malware produced in high volume, often across many languages, with the goal of overwhelming defenders rather than delivering one highly sophisticated implant.
Bitdefender says it links the activity with medium confidence to APT36, also known as Transparent Tribe, a Pakistan-aligned threat actor.
The report says the main targets are Indian government entities, embassies, and defense-linked organizations, with some secondary targeting of Afghanistan government entities and private businesses.
Not necessarily. The evidence points more to faster output and wider variation than to flawless engineering. Google and Bitdefender both describe the current trend as AI improving attacker productivity, not yet delivering a complete leap in capability.
Because attackers can use them as command channels or storage layers, and many organizations already trust those services. That makes malicious traffic harder to separate from normal business traffic.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages