Tropic Trooper uses GitHub and VS Code tunnels in a new campaign targeting East Asia
A newly detailed cyberespionage campaign tied to Tropic Trooper shows the group shifting to newer tools and more covert infrastructure. Zscaler ThreatLabz says the attackers used a trojanized SumatraPDF executable, a custom AdaptixC2 beacon listener, GitHub as a command channel, and Visual Studio Code tunnels for follow-on remote access.
The campaign targeted Chinese-speaking individuals in Taiwan, along with victims in South Korea and Japan, according to Zscaler. Researchers say they first identified the malicious ZIP archive on March 12, 2026, and linked the operation to Tropic Trooper with high confidence.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What makes this operation stand out is not just the malware. It is the use of legitimate developer and collaboration infrastructure that many organizations already trust. GitHub Issues and VS Code tunnels both serve real business purposes, which gives attackers useful cover once they get inside a network.
How the attack starts
Zscaler says the infection begins with a ZIP archive containing a file disguised as a document about US-UK and US-Australia nuclear submarine cooperation. The executable is actually a trojanized SumatraPDF binary that displays a decoy PDF while quietly launching the next stage in the background.
That second stage deploys an AdaptixC2 beacon. Zscaler says the loader resembles the TOSHIS loader previously linked to Tropic Trooper, and the staging infrastructure also hosted additional tools associated with the group, including a Cobalt Strike beacon with the watermark “520” and an EntryShell backdoor.
The use of a decoy document matters because it lowers suspicion at the exact moment the malware installs. The victim sees believable content, while the compromise continues out of view. That observation follows directly from Zscaler’s description of the loader behavior.
How GitHub became the command channel
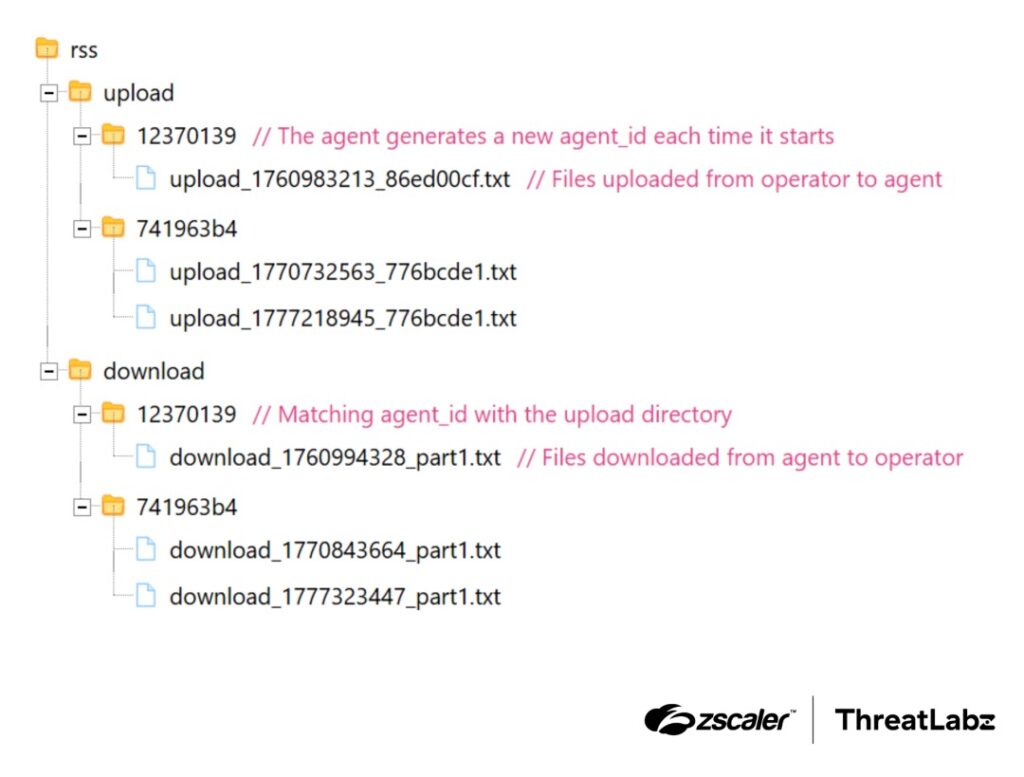
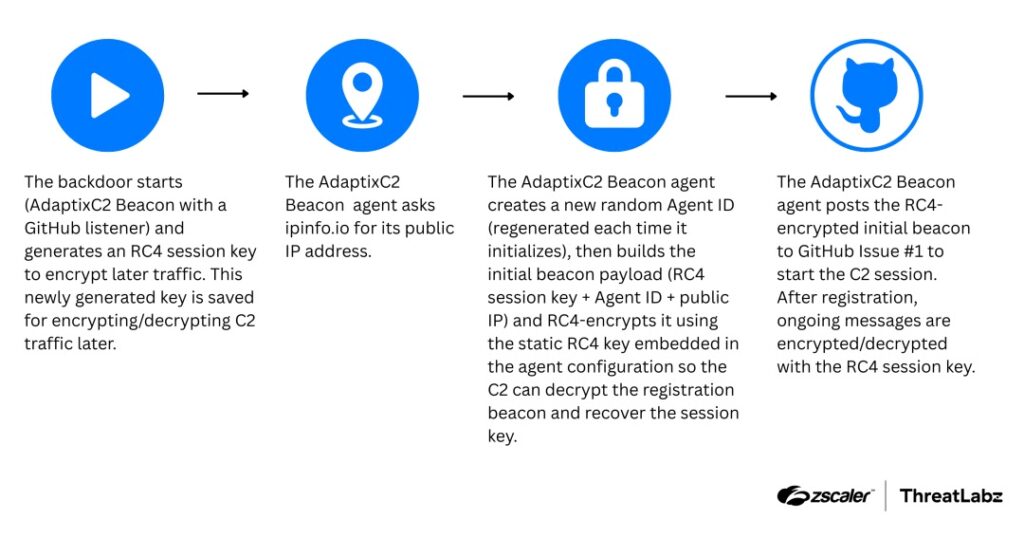
Zscaler says Tropic Trooper built a custom beacon listener on top of AdaptixC2 that uses a GitHub repository for command-and-control. Instead of contacting a classic malware server, the beacon reads tasks from GitHub Issues and uploads results back to the same repository.
GitHub’s own documentation confirms that its REST API supports issue operations, which makes this method plausible and easy to blend into normal API traffic. For defenders, that creates a harder problem because GitHub access is common in many enterprise environments, especially on developer systems.
Zscaler says the beacon first fetches its external IP from ipinfo.io, then sends an encrypted initial beacon to GitHub Issue number 1. It later checks open issues for tasks, processes commands based on issue-title patterns, and posts encrypted results back to the repository as file content. Researchers also say the uploaded data was deleted within about 10 seconds, making forensic recovery much harder.
Why VS Code tunnels matter here
Zscaler says the attackers used VS Code tunnels for interactive remote access after deciding a victim machine was worth deeper exploitation. Commands seen during the intrusion included scheduled task creation for persistence, plus reconnaissance with arp and net view, before the operators moved to VS Code tunnel usage.
]Microsoft’s VS Code documentation confirms that Remote Tunnels lets users securely access a machine from another device without configuring SSH. That is a legitimate admin and developer feature, but in an intrusion it can also give attackers a low-friction path to stable remote access over trusted infrastructure.
This is why the campaign deserves attention beyond the malware family itself. A defender may block a suspicious domain, but GitHub and VS Code services often stay allowed by design. That shifts detection away from simple network blocking and toward user, process, and behavior monitoring. This last point is an inference based on the documented use of GitHub APIs and VS Code tunnels.
What organizations should watch for
Security teams should look for GitHub API access from endpoints that do not normally perform developer tasks, especially if those systems also show suspicious process trees or recent execution of unexpected binaries. Zscaler specifically recommends monitoring unexpected GitHub API traffic from non-developer endpoints.
They should also audit the use of VS Code tunnels in corporate environments. Microsoft documents how remote tunnel access can be turned on through the VS Code account menu, command palette, or command-line tooling, which means defenders can build detections around those actions.
Zscaler also advises hunting for scheduled task names that mimic system services, trojanized binaries that pose as legitimate apps, and IP lookup traffic such as calls to ipinfo.io from systems that have no business making them.
Quick facts
| Item | Details |
|---|---|
| Threat actor | Tropic Trooper |
| Reported by | Zscaler ThreatLabz |
| Discovery date | March 12, 2026 |
| Main lure | Trojanized SumatraPDF disguised as a military-themed document |
| Initial payload | AdaptixC2 beacon |
| Command channel | GitHub repository and GitHub Issues |
| Follow-on access | VS Code tunnels |
| Main targets | Taiwan, South Korea, Japan |
Defensive steps
- Monitor GitHub API requests from non-developer endpoints, especially access patterns involving repositories and issues.
- Restrict or audit VS Code tunnel usage, including the
code tunnelworkflow and UI-based activation. - Use application allowlisting to stop trojanized binaries that impersonate trusted tools such as SumatraPDF.
- Hunt for suspicious scheduled tasks with names that resemble Microsoft or DNS services.
- Flag systems that suddenly query IP lookup services like ipinfo.io without a legitimate need.
- Tighten email and file gateway controls around ZIP archives that contain executables disguised as documents.
FAQ
Zscaler says the group moved to AdaptixC2 with a custom listener, used GitHub Issues as a C2 layer, and relied on VS Code tunnels for remote access after compromise.
Because GitHub API traffic can look normal inside many organizations. GitHub’s official documentation shows that issue operations are standard API functions, which gives attackers a trusted platform to hide in.
Yes. Microsoft documents Remote Tunnels as a normal way to access a remote machine without setting up SSH. In this case, researchers say attackers abused that legitimate feature after gaining a foothold.
Zscaler says the operation targeted Chinese-speaking individuals in Taiwan, plus victims in South Korea and Japan.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages