Tycoon2FA operators resume cloud account phishing after infrastructure disruption

Tycoon2FA is already back in action after the March 4 takedown. CrowdStrike says the phishing-as-a-service platform resumed cloud account phishing within days of the Europol-led disruption, with activity quickly returning to levels seen before the operation.
That makes the takedown look more like a temporary setback than a lasting shutdown. Europol said authorities and private-sector partners seized 330 domains tied to the service, but CrowdStrike found that Tycoon2FA operators rebuilt fast and kept using largely unchanged tactics, techniques, and procedures.
Tycoon2FA remains one of the biggest phishing threats aimed at cloud accounts. Microsoft said that by mid-2025, the platform accounted for about 62% of all phishing attempts it blocked, including more than 30 million emails in a single month. Microsoft also linked the service to an estimated 96,000 phishing victims worldwide since 2023, including more than 55,000 Microsoft customers.
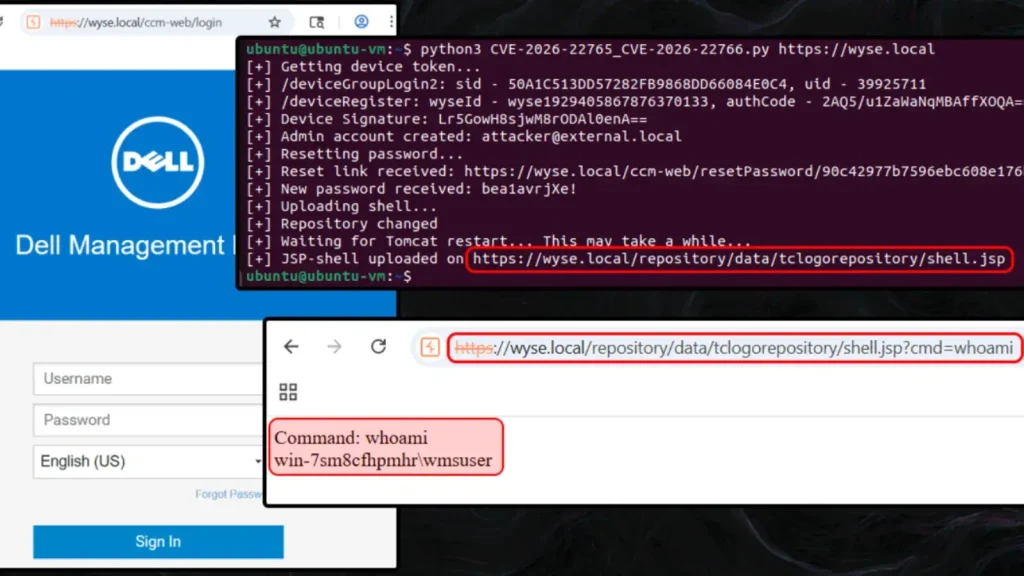
The platform works as an adversary-in-the-middle phishing kit. It sits between the victim and a legitimate login page, captures credentials and session cookies in real time, and lets attackers bypass multifactor authentication by reusing the stolen session. Microsoft says Tycoon2FA has impersonated services such as Microsoft 365, OneDrive, Outlook, SharePoint, and Gmail.
What happened after the takedown
CrowdStrike said daily Tycoon2FA activity dropped sharply right after the March 4 disruption, falling to about 25% of pre-disruption levels on March 4 and March 5. That dip did not last. The company says volumes rebounded within days and returned to levels consistent with early 2026 activity.
Researchers say the post-takedown campaigns looked familiar. The phishing flow still used decoy pages, fake CAPTCHA checks, credential capture, and automated logins into Microsoft Entra ID accounts once credentials and tokens had been stolen. CrowdStrike added that the service continued to support business email compromise, email thread hijacking, cloud account takeover, and abuse of trusted platforms for phishing delivery.
How Tycoon2FA attacks work
| Stage | What happens | Why it matters |
|---|---|---|
| Phishing lure | Victims receive links through email, URL shorteners, presentation platforms, or compromised SharePoint environments | Trusted delivery paths can increase click rates |
| Decoy page | Victims land on fake CAPTCHA or fake sign-in pages | The fake flow helps screen targets and hide from researchers |
| Credential relay | Obfuscated code proxies the victim’s credentials to the real Microsoft 365 login page | The attacker captures credentials in real time |
| Session theft | MFA tokens and session cookies get intercepted | Attackers can bypass MFA and take over accounts |
| Account abuse | Threat actors log into Microsoft Entra ID and begin follow-on activity | This can lead to BEC, inbox manipulation, and further phishing |
What CrowdStrike observed
CrowdStrike said its Falcon Complete team responded to at least 30 suspected Tycoon2FA-enabled phishing incidents between March 4 and March 6, involving at least 12 decoy and credential-capture pages. The company also said automated logins often came from IPv6 addresses tied to M247 Europe SRL in Romania. Eight of the 11 IPv6 addresses observed in March were first seen on or after March 1, which suggests the operators quickly replaced parts of their infrastructure.
The company also said operators used generative AI to create convincing fake websites for visitors who failed geofencing checks. That appears designed to waste the time of researchers and automated analysis systems while keeping the real phishing flow hidden from unwanted traffic.
Why this threat still matters
The quick rebound shows the limits of infrastructure-only disruption. When authorities seize domains but do not fully remove the people, hosting, and support systems behind a phishing service, operators can often rebuild with new domains and IP space and continue serving customers. CrowdStrike’s findings suggest that is exactly what happened here.
For Microsoft 365 and Google cloud users, the risk remains serious. Microsoft says Tycoon2FA can keep working even after a password reset if active sessions and stolen tokens are not revoked. That makes fast response essential after a suspected phishing compromise.
What organizations should do now
- Treat MFA as necessary but not sufficient. Tycoon2FA is built to get around it by stealing live sessions.
- Monitor Exchange and Microsoft 365 environments for suspicious inbox rules, hidden folders, and unusual Entra ID sign-ins. CrowdStrike says these are common early signs of compromise and BEC staging.
- Watch for logins from unusual IPv6 ranges, unexpected geographies, or new infrastructure tied to known phishing activity.
- Train users to distrust links delivered through URL shorteners, presentation sites, and compromised trusted contacts. CrowdStrike says all three appeared in recent campaigns.
- Revoke active sessions and tokens during incident response, not just passwords. Microsoft says stolen session cookies can keep attackers inside even after a password change.
Bottom line
Tycoon2FA never stayed down for long. The latest evidence shows that the March 4 disruption damaged part of the platform’s infrastructure, but not the service itself. Operators rebuilt quickly, kept their core attack flow intact, and resumed phishing aimed at cloud accounts with little visible slowdown beyond the first few days.
That means defenders should not read the takedown as the end of the threat. It was a real hit, but not a knockout. Organizations still need stronger phishing detection, session-aware incident response, tighter cloud monitoring, and better user training to reduce the risk from Tycoon2FA-style attacks.
FAQ
Tycoon2FA is a phishing-as-a-service platform that helps cybercriminals run adversary-in-the-middle phishing attacks and bypass MFA by stealing session cookies and credentials in real time.
Europol and partners disrupted part of the platform on March 4, 2026, and seized 330 domains. But CrowdStrike says the operators resumed activity within days and returned to near pre-disruption levels.
Because it captures the live authenticated session, not just the password. Microsoft says attackers can reuse stolen session cookies and remain inside unless defenders revoke active sessions and tokens.
Microsoft says Tycoon2FA has impersonated Microsoft 365, OneDrive, Outlook, SharePoint, and Gmail to steal credentials and authenticated sessions.
Start with suspicious Entra ID sign-ins, inbox rule creation, hidden folders in Exchange, phishing flows that use fake CAPTCHA pages, and redirects through URL shorteners or trusted platforms. CrowdStrike says these all appeared in the latest campaigns.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages