US and European authorities disrupt SocksEscort proxy network tied to AVRecon Linux malware
US and European authorities have disrupted SocksEscort, a long-running criminal proxy service that routed malicious traffic through hacked routers and other edge devices. The takedown targeted infrastructure used to sell access to infected residential and small-business devices, while officials said all infected devices used in the service have now been disconnected.
The operation was backed by the US Department of Justice, Europol, and private-sector partners including Lumen’s Black Lotus Labs. Europol said authorities seized 34 domains and 23 servers across seven countries during the action day, while US authorities also froze $3.5 million in cryptocurrency.
Investigators say SocksEscort worked by abusing compromised routers and IoT devices, then selling that access as a proxy service to criminals who wanted “clean” residential IP addresses. The DOJ said the service had offered access to about 369,000 IP addresses since the summer of 2020, and that the SocksEscort application still listed roughly 8,000 infected routers in February 2026, including 2,500 in the United States.
Lumen’s Black Lotus Labs tied the network to AVRecon, a Linux malware strain first detailed in 2023. The researchers said SocksEscort had maintained an average of about 20,000 infected devices each week for the last few years, and that they observed 280,000 distinct victim IP addresses since early 2025.
What authorities say happened
| Item | Confirmed detail |
|---|---|
| Service disrupted | SocksEscort proxy network |
| Malware behind it | AVRecon |
| Domains seized | 34 |
| Servers seized | 23 |
| Countries involved in server action | 7 |
| Crypto frozen | $3.5 million |
| IPs offered since 2020 | About 369,000 |
| Infected routers listed in Feb. 2026 | About 8,000 |
| US routers in Feb. 2026 | About 2,500 |
The DOJ says SocksEscort enabled multiple fraud schemes that caused major losses. Those included the theft of $1 million in cryptocurrency from a New York victim, $700,000 in losses tied to fraud against a Pennsylvania manufacturing business, and about $100,000 in damages in a fraud case involving MILITARY STAR card holders.
Europol described the network as a malicious proxy service built on infected routers and IoT devices across 163 countries. The agency said the service gave customers access to more than 35,000 proxies and was used in cybercrime including fraud, ransomware, DDoS attacks, and the distribution of child sexual abuse material.
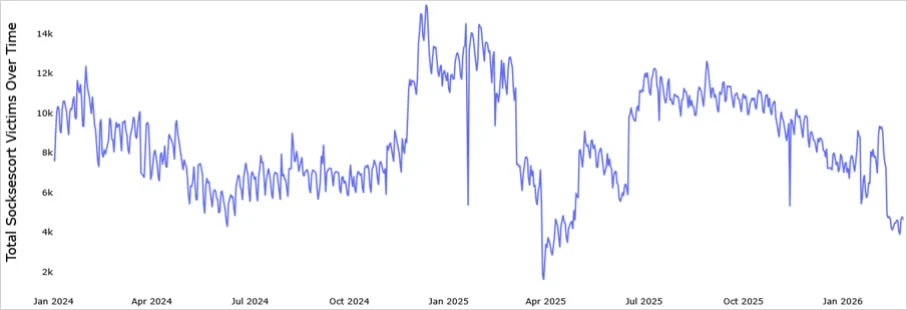
Source: Black Lotus Labs
How the botnet worked
According to an FBI and CISA joint advisory, SocksEscort operators exploited known vulnerabilities in routers and IoT devices, then installed AVRecon malware to maintain remote access and fold those devices into a botnet. That let the operators monetize the hacked hardware by reselling proxy access to criminals who wanted to hide their real IP addresses.
Black Lotus Labs says AVRecon appears to have been used only to grow SocksEscort, not to feed other botnets or services. The researchers also said the operators kept their command-and-control infrastructure unusually quiet, which helped the service persist after earlier disruption attempts.
That long lifespan is one reason this case matters. SocksEscort was not a short-lived malware campaign. Officials and researchers describe it as a service that ran for years, constantly replenished with compromised edge devices that looked like ordinary home or small-business internet connections.
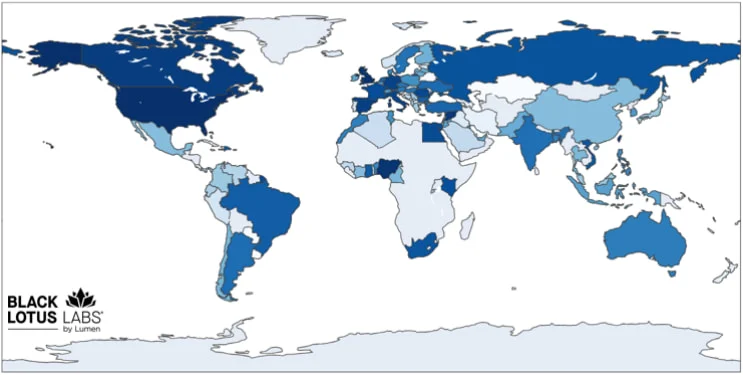
Source: Black Lotus Labs
Why this takedown matters
- It hit both the criminal storefront and the underlying infrastructure
- It cut off access to thousands of infected routers
- It targeted a proxy service that helped criminals blend into legitimate residential traffic
- It shows how vulnerable older routers and IoT gear remain
The case also highlights a broader security problem. Attackers continue to target Linux-based routers and edge devices because many stay online for years without updates, run default settings, or reach end of life without being replaced. That makes them ideal building blocks for proxy botnets and fraud infrastructure. This is an inference supported by the government advisory’s mitigation guidance and the scale of infections described by DOJ and Europol.
How to reduce the risk of router compromise
- Replace routers and edge devices that have reached end of life
- Install the latest available firmware updates
- Change default administrator passwords
- Disable remote administration if you do not need it
- Watch for official guidance from your vendor or ISP
These are the steps recommended in the joint US advisory tied to the operation.
FAQ
SocksEscort was a criminal proxy service that sold access to compromised routers and IoT devices so customers could route traffic through residential or small-business IP addresses.
Researchers and law enforcement tied the network to AVRecon, a Linux malware family used to compromise routers and maintain remote access.
The DOJ said SocksEscort had offered access to about 369,000 IP addresses since 2020. Europol said the compromised-device footprint spanned 163 countries.
Europol said investigators took down and seized 34 domains and 23 servers in seven countries, while US authorities froze $3.5 million in cryptocurrency.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages