Windows Remote Desktop can leave behind image fragments attackers may rebuild

Windows Remote Desktop can leave behind small image fragments from past RDP sessions on the local computer. SCYTHE Labs recently highlighted how attackers can extract those cached tiles and stitch parts of a remote session into readable images.
The issue comes from a normal Windows performance feature called persistent bitmap caching. Microsoft’s protocol documentation says persistent bitmap caches store bitmap images sent to the client and can remain available after the RDP connection closes.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The key point is not that Remote Desktop has a new critical vulnerability. The risk comes from local session artifacts that many users and IT teams may not know exist. If an attacker gains access to a user profile, those files can reveal what appeared on screen during earlier RDP sessions.
What the RDP Bitmap Cache stores
The RDP Bitmap Cache stores small image tiles from Remote Desktop sessions. On Windows, these cache files commonly sit in the user profile under %LOCALAPPDATA%\Microsoft\Terminal Server Client\Cache.
These files are not clean screenshots. They look more like scattered pieces from a shredded image. However, forensic tools can extract the tiles and help rebuild useful visual fragments.
That creates a real privacy and security problem. Even a partial image may expose an internal dashboard, customer record, email inbox, file path, admin console, ticketing system, or a visible credential field.
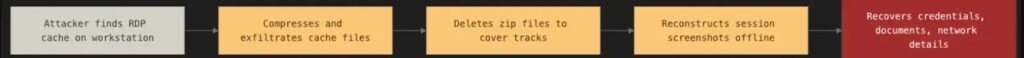
How attackers can turn fragments into screenshots
SCYTHE explains that an attacker with access to the user profile can collect the RDP cache folder, compress it, and move it off the machine. The process does not necessarily require administrator privileges because the cache sits inside a standard user directory.
After extraction, open-source tools can process the files. ANSSI’s bmc-tools parses RDP bitmap cache files into many small image tiles, while RdpCacheStitcher helps arrange those tiles into meaningful images.
RdpCacheStitcher’s project page describes it as a tool that supports forensic analysts in reconstructing useful images from RDP cache bitmaps. That same capability can also help attackers if they already have access to the cache files.
| Step | What happens |
|---|---|
| 1 | A user connects to another system through Remote Desktop |
| 2 | Windows caches visual bitmap tiles to improve performance |
| 3 | The files remain in the local user profile |
| 4 | An attacker copies or compresses the cache directory |
| 5 | Tools extract the cache into small image fragments |
| 6 | The fragments can be arranged into partial screenshots |
Why this matters for companies using RDP
RDP already appears often in post-compromise activity because attackers use it for remote control, lateral movement, and hands-on-keyboard access. SCYTHE notes that threat groups such as BianLian, Medusa, and Scattered Spider have used RDP in real intrusions.
For attackers, the bitmap cache can become a quiet reconnaissance source. It may show which tools a company uses, which systems an administrator accessed, and what sensitive information appeared on screen.
For incident responders, the same cache can provide useful evidence. DFIR research has shown that RDP bitmap artifacts can help analysts reconstruct parts of attacker activity and understand what happened during a remote session.
What is confirmed and what still needs context
What is confirmed is that persistent bitmap caches exist in the RDP protocol and can persist beyond a single RDP connection. Microsoft’s documentation describes persistent bitmap caches as stores for bitmap images sent to the client.
What is also confirmed is that public tools can parse and reconstruct RDP bitmap cache data. bmc-tools describes itself as an RDP Bitmap Cache parser, and RdpCacheStitcher supports reconstruction of useful images from extracted cache tiles.
The important context is that this does not give a remote attacker automatic access by itself. The attacker still needs access to the local machine, the user profile, or the cache files before they can extract and rebuild these fragments.
At a glance
| Item | What current reporting shows |
|---|---|
| Feature involved | RDP Bitmap Cache |
| Product area | Windows Remote Desktop client |
| Main purpose | Improve RDP performance by caching visual tiles |
| Common cache path | %LOCALAPPDATA%\Microsoft\Terminal Server Client\Cache |
| Required attacker access | Local access to the user profile or cache files |
| Admin rights needed | Not necessarily |
| Tools mentioned | bmc-tools, RdpCacheStitcher |
| Main risk | Sensitive session visuals may remain on disk |
| Defensive option | Disable persistent bitmap caching where appropriate |
Why an empty cache can also matter
SCYTHE also highlights a second investigation clue. If a workstation has a long history of RDP use but the bitmap cache suddenly appears empty, defenders should treat that as suspicious.
Attackers who understand RDP cache artifacts may delete or corrupt the folder before leaving. That does not prove compromise on its own, but it can support an investigation when combined with logs, PowerShell history, remote access records, and file activity.
This makes the cache useful in two ways. Existing fragments may reveal what appeared on screen, while missing fragments may suggest someone attempted cleanup.
What security teams can do now
- Check whether persistent bitmap caching needs to remain enabled for all users.
- Disable persistent bitmap caching for administrators and high-risk users where performance allows.
- Monitor access to
%LOCALAPPDATA%\Microsoft\Terminal Server Client\Cache. - Alert on PowerShell commands that compress or copy the RDP cache directory.
- Watch for outbound transfers of ZIP files from user profile or temporary folders.
- Add RDP cache review to incident response playbooks.
- Treat sudden cache deletion as a possible investigation lead.
- Use privileged access workstations for sensitive administration tasks.
- Train administrators not to leave passwords, tokens, or sensitive records visible during RDP sessions.
How to reduce the exposure
Users can reduce future exposure by disabling persistent bitmap caching in the Remote Desktop Connection client. Open mstsc.exe, select Show Options, go to the Experience tab, and clear Persistent bitmap caching.
Administrators can also manage this through Group Policy or endpoint configuration. SCYTHE recommends testing whether detection tools catch compression commands targeting the cache directory and adding the RDP cache directory to file integrity monitoring where possible.
Disabling the cache helps reduce future risk, but it does not automatically answer whether old files already contain sensitive data. Security teams should review existing cache artifacts during investigations involving RDP.
FAQ
The RDP Bitmap Cache is a Remote Desktop performance feature that stores small visual tiles from remote sessions on the local machine. It helps reduce repeated image transfers during RDP sessions.
No. This is not a new remote code execution flaw. It is a security exposure created by cached local artifacts that may remain after RDP sessions end.
Sometimes they can rebuild partial or meaningful images, but not always perfect full screenshots. Tools such as bmc-tools and RdpCacheStitcher can help extract and arrange the cached image tiles.
On many Windows systems, the files sit under %LOCALAPPDATA%\Microsoft\Terminal Server Client\Cache in the current user profile.
Companies should consider disabling it for administrators, help desk users, developers, and anyone who uses RDP to access sensitive systems. Teams should test the performance impact before applying the change broadly.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more


User forum
0 messages