


Massive Brute Force Attack Targets VPN Devices with 2.8 Million IPs
Microsoft 365 to Shut Down Its Free VPN
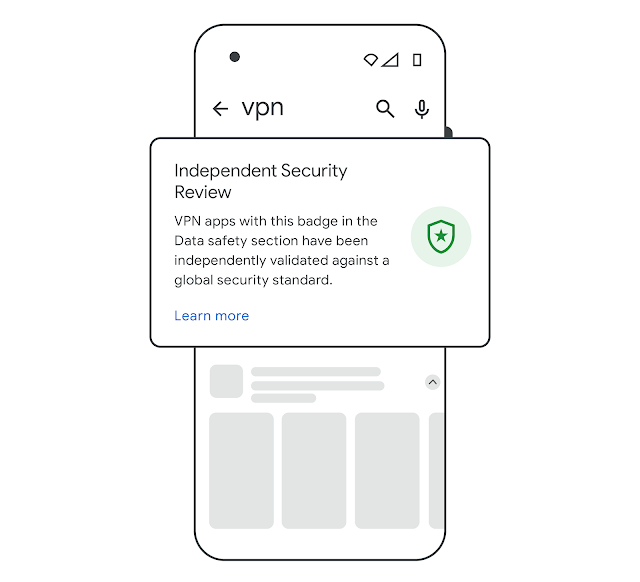
Google Play Introduces “Verified” Badge for VPN Apps

NTISB Warns Against Malicious Browser Extensions and VPNs
China-Linked Hackers Exploit Ivanti VPN Zero-Day
Google Detects Playfulghost Backdoor Malware in VPN Apps

Is Planet VPN Safe? Yes, It is! [But It’s Slow]

9 Best Datacenter Proxies [Tested & Ranked]
New memecoin tokens drop by 50% as UK watchdog bans platform

9 Best Web Scraping Tools [A Detailed Expert Review]

8 Best SOCKS5 Proxies [Tested, Reviewed, & Ranked]
Pakistan extends deadline for VPN registration, decides not to block VPNs for now
Australia Passes Law to Ban Social Media for Kids Under 16
