Malicious NuGet Packages Target ASP.NET Developers Stealing Credentials Through JIT Hooks

Four malicious NuGet packages attack ASP.NET developers deploying credential-stealing backdoors. NCryptYo, DOMOAuth2_, IRAOAuth2.0, SimpleWriter_ racked up 4,500+ downloads since August 2024. JIT compiler hijacking and localhost proxies evade detection completely.
Hamzazaheer published typosquatted packages mimicking legitimate cryptography, OAuth libraries. NCryptYo impersonates Windows CNG provider with identical DLL namespace. Static constructor fires on assembly load creating hidden proxy tunnel immediately.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Localhost port 7152 relays traffic to attacker infrastructure silently. DOMOAuth2_ and IRAOAuth2.0 extract ASP.NET Identity data including user IDs, roles, permissions. SimpleWriter_ drops persistent executables disguised as PDF tools.
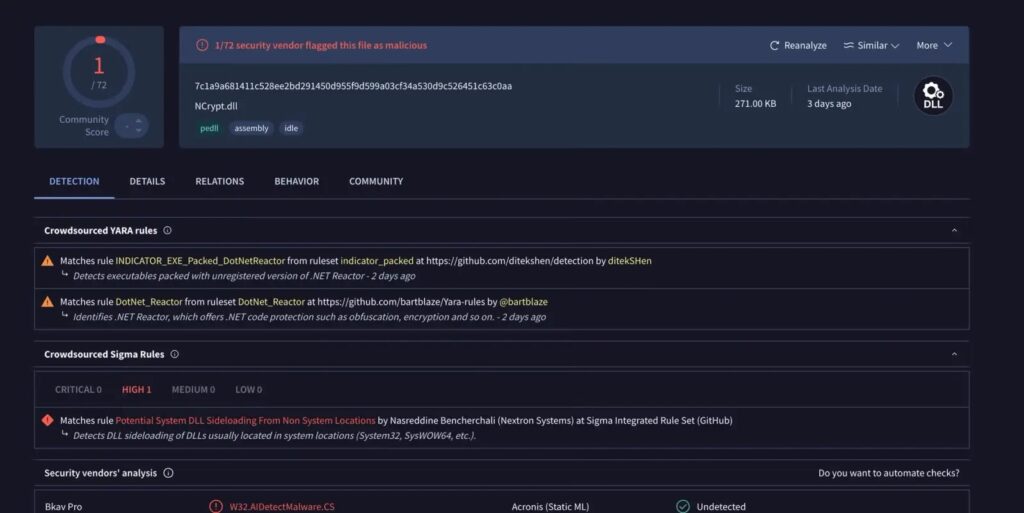
GZip-compressed Base64 authentication tokens identical across packages confirm single operator. VirusTotal shows 1/72 engines detect NCrypt.dll despite aggressive obfuscation. .NET Reactor protection includes 14-day expiry and anti-debugging.
JIT hooking intercepts .NET method compilation decrypting payloads runtime-only. Static scanners see inert encrypted resources. 126KB primary payload builds external C2 tunnel post-compromise.
Production web apps inherit backdoors from compromised developer workstations. CI/CD pipelines propagate malware silently to customer deployments. Supply chain compromise extends beyond initial targets.
Package Details Table
| Package | Disguise | Downloads | Primary Function |
|---|---|---|---|
| NCryptYo | Crypto library | Unknown | JIT hook + proxy |
| DOMOAuth2_ | OAuth2 client | Unknown | Identity theft |
| IRAOAuth2.0 | OAuth2 client | Unknown | Identity theft |
| SimpleWriter_ | PDF writer | Unknown | File dropper |
Attack Infrastructure
- Proxy Port: localhost:7152 external relay
- Obfuscation: .NET Reactor + encrypted resources
- Detection Evasion: JIT compiler hijacking
- Token Encoding: GZip + custom Base64
- Persistence: Production app deployment
CI/CD scanning must flag static constructors and localhost listeners. Obfuscation markers require automated rejection policies.
Mitigation Actions
- Verify package authors and download history
- Block localhost:7152 outbound connections
- Scan for JIT hooking in dependencies
- Audit ASP.NET Identity data access
- Deploy obfuscation detection in pipelines
- Remove hamzazaheer published packages
Developer workstations represent highest risk vectors. Compromised builds propagate through entire deployment chains. Enterprise .NET environments require immediate package audits.
FAQ
NCryptYo, DOMOAuth2_, IRAOAuth2.0, SimpleWriter_.
JIT compiler hijacking decrypts runtime-only.
Identical GZip Base64 auth tokens across packages.
ASP.NET Identity user IDs, roles, permissions.
Static constructor fires on assembly load.
Backdoors deploy to customer web applications.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages