Triad Nexus rebuilds after FUNNULL sanctions with rotating domains and scam portals

Triad Nexus, a cybercrime network linked to the FUNNULL ecosystem, has rebuilt part of its fraud infrastructure after U.S. sanctions and now uses more than 175 rotating CNAME domains to keep scam portals online. Silent Push said the group shifted to new delivery methods after the crackdown and now hides traffic behind layered DNS chains, front companies, and cloud-hosted infrastructure.
The new setup matters because it makes fake investment platforms, brand clones, and gambling-related portals harder to trace and block. Silent Push said the operation now leans on what it calls infrastructure laundering, where malicious services route activity through legitimate cloud providers to make the traffic look more trustworthy.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This is not a brand-new actor. Silent Push and other reporting say Triad Nexus has operated for years as part of a broader scam ecosystem tied to fraud, laundering, and illegal gambling, but the infrastructure changed significantly after sanctions hit FUNNULL Technology Inc. and its administrator in May 2025.
What changed after the sanctions
The U.S. Treasury’s Office of Foreign Assets Control sanctioned Funnull Technology Inc. on May 29, 2025, saying the company provided infrastructure for hundreds of thousands of scam-linked websites tied to virtual currency investment fraud. Treasury said those schemes caused more than $200 million in reported U.S. victim losses.
Silent Push says Triad Nexus adapted by reducing direct dependence on FUNNULL and moving toward rotating CNAME pools, enterprise cloud infrastructure, and branded front companies. SecurityWeek’s coverage of the Silent Push report says the network launders infrastructure through major providers including Amazon Web Services, Cloudflare, Google, and Microsoft.
The group also appears to have changed its geographic exposure. Silent Push says many of the scam portals now block U.S. visitors with a “The region has been denied” message, while expanding localized operations in Spanish, Vietnamese, and Indonesian markets. That suggests the network wants to keep operating while staying farther away from the most direct U.S. enforcement pressure.
| Shift | Before sanctions | After sanctions |
|---|---|---|
| Core infrastructure | Heavy reliance on FUNNULL-linked delivery | More distributed cloud and DNS-based concealment |
| Domain strategy | More stable infrastructure patterns | 175+ rotating CNAME domains |
| Geographic exposure | Wider direct exposure, including U.S.-linked impact | U.S. access blocks and stronger non-U.S. targeting |
| Trust layer | Scam infrastructure tied more directly to known bad ecosystems | Front companies and cloud-hosted masking |
How the CNAME system helps the scam network hide
A CNAME record points one domain name to another, and Silent Push says Triad Nexus chains several of them together before the traffic reaches the final destination. The firm says many security tools only inspect one step in the chain, which can leave the real endpoint hidden behind multiple layers of redirection.
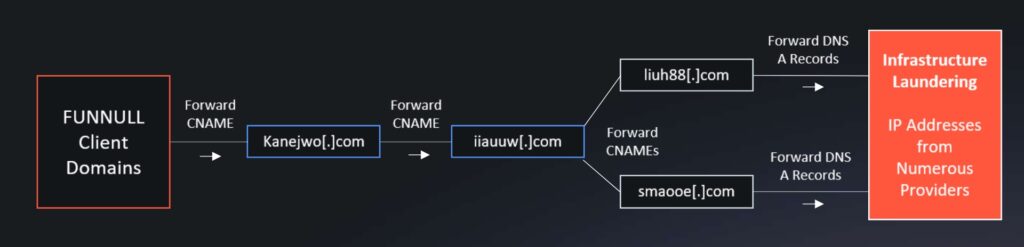
According to the Silent Push report, some Triad Nexus chains run three or four layers deep before landing on an IP address hosted on a reputable enterprise platform. That design can frustrate automated blocking because defenders may see a harmless-looking intermediate domain rather than the final scam server.
Silent Push also says the actor abandoned stable CNAME patterns in favor of a large rotating pool of randomly generated domains. That gives the network a way to reshuffle infrastructure quickly when investigators or service providers begin to identify one cluster.
Reported scam themes tied to the network
- Fake crypto investment platforms and pig-butchering portals
- Money laundering and illegal gambling infrastructure
- Brand impersonation pages copying luxury and financial companies
- “Clean” front companies used to make the operation look legitimate
The money and the global reach
The sample article says Triad Nexus has been linked to more than $1 billion in victim losses with an average loss of $47,000. I could not confirm those exact figures in the primary Treasury release or the SecurityWeek summary of Silent Push. The confirmed number I found from Treasury is more than $200 million in reported U.S. losses tied to FUNNULL-facilitated scam activity.
That does not make the operation small. Treasury said Americans lose billions of dollars every year to cyber scams, and it described FUNNULL as infrastructure for hundreds of thousands of scam websites. Silent Push and follow-on coverage say Triad Nexus continues to support large-scale fraud through infrastructure concealment and localized scam branding.
One example from the Silent Push reporting involves cdnbl.com, described as a fake CDN provider that claimed a long client history despite being much newer. Silent Push presents that as part of a wider pattern where the network builds polished business fronts to gain trust while hiding malicious delivery underneath.
What defenders should watch now
Security teams should stop treating a single DNS lookup as enough when they investigate scam infrastructure. Silent Push’s findings suggest defenders need full CNAME chain analysis, not just surface-level domain checks, because the visible hostname may only be one relay in a deeper redirection system.
Brand monitoring also matters here. The operation reportedly clones luxury brands, financial services, and payment platforms, which means newly registered lookalike domains and polished landing pages may signal fraud even before the final infrastructure is fully mapped.
The broader lesson is that sanctions disrupted the old setup but did not end the criminal business. Instead, the network appears to have become more adaptive, more distributed, and harder to trace, which is often what happens when enforcement hits a mature cybercrime service provider without fully dismantling its surrounding ecosystem. That last point is an inference based on the post-sanctions shift described by Silent Push, Treasury, and follow-on reporting.
Practical response steps
- Follow full DNS and CNAME chains instead of checking only the first hop.
- Monitor for new lookalike domains tied to finance, luxury brands, and crypto services.
- Review cloud-hosted scam infrastructure, even when it appears on reputable platforms.
- Treat geofencing and region-denied messages as possible signs of selective scam delivery.
- Track front-company branding that claims long operating histories without matching domain age or business records.
FAQ
Triad Nexus is a cybercrime network that Silent Push links to scam delivery, laundering activity, and illegal gambling infrastructure. It has also been associated with pig-butchering style fraud operations.
The connection comes from shared or related infrastructure patterns. Treasury sanctioned Funnull Technology Inc. in May 2025 for supporting scam-linked websites, and Silent Push says Triad Nexus rebuilt after that crackdown while distancing itself from direct reliance on FUNNULL.
They let attackers hide the final destination of scam traffic behind multiple layers of DNS redirection. That makes automated detection and takedowns slower and less reliable.
No. Public reporting suggests sanctions forced operational changes, but the network adapted with new infrastructure, front companies, and new regional targeting.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages