Chinese state hackers hit South American telcos with new TernDoor, PeerTime, and BruteEntry malware

A China-linked hacking group has spent months targeting telecom providers in South America with a new cross-platform malware toolkit built for persistence, remote control, and expansion inside networks. Cisco Talos says the activity cluster, tracked as UAT-9244, has operated since 2024 and has compromised Windows systems, Linux hosts, and network-edge devices used by telecommunications providers.
Talos says it has high confidence that UAT-9244 is a China-nexus advanced persistent threat closely associated with FamousSparrow and also overlapping with Tropic Trooper based on tooling, victimology, and tradecraft. At the same time, Talos says it could not establish a solid connection to Salt Typhoon, even though the target profile looks similar.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The most important part of the report is the malware set itself. Talos says the group deployed three previously undocumented malware families: TernDoor, a Windows backdoor; PeerTime, a Linux backdoor that uses the BitTorrent protocol for command and control; and BruteEntry, a Go-based brute-force and scanning tool that helps build operational relay boxes, or ORBs, from compromised devices.
That combination makes this campaign more than a standard espionage intrusion. It gives the attackers a way to hold access across multiple operating systems, hide inside edge infrastructure, and turn infected systems into launch points for more scanning and password attacks. For telecom networks, that is a serious risk because the infrastructure sits at the center of traffic flow, customer data, and enterprise connectivity.
What Cisco Talos found
| Malware | Platform | Main role |
|---|---|---|
| TernDoor | Windows | Backdoor for persistence, remote shell, file operations, process execution |
| PeerTime | Linux / embedded systems | P2P backdoor using BitTorrent-based C2 |
| BruteEntry | Linux / edge systems | Brute-force scanner that turns devices into ORB nodes |
Talos says TernDoor arrives through DLL side-loading. The attackers use the legitimate executable wsprint.exe to load a malicious BugSplatRc64.dll, which then decrypts and injects the final payload into memory, specifically into msiexec.exe. Talos also says the malware includes an embedded Windows driver, WSPrint.sys, that can terminate, suspend, and resume processes.
On top of that, TernDoor can run remote shell commands, launch arbitrary processes, collect system information, read and write files, and uninstall itself. Talos says the malware persists through scheduled tasks and Windows Registry changes, and those same mechanisms help hide the scheduled task from view.
PeerTime takes the campaign into Linux and telecom edge environments. Talos says it observed PeerTime variants for ARM, AARCH64, PowerPC, and MIPS, which strongly suggests the malware was built for routers, appliances, and other embedded gear common in telecom infrastructure. Talos also found a C or C++ version and a Rust-based version, along with Simplified Chinese debug strings in one instrumentor binary.

The backdoor uses the BitTorrent protocol for command and control, which makes it stand out from more conventional malware. Talos says PeerTime can decrypt and load payloads in memory, rename its process to look legitimate, download payloads from peers, and use BusyBox to write files to the host. That gives the attackers a flexible, peer-to-peer way to operate across mixed Linux and appliance environments.
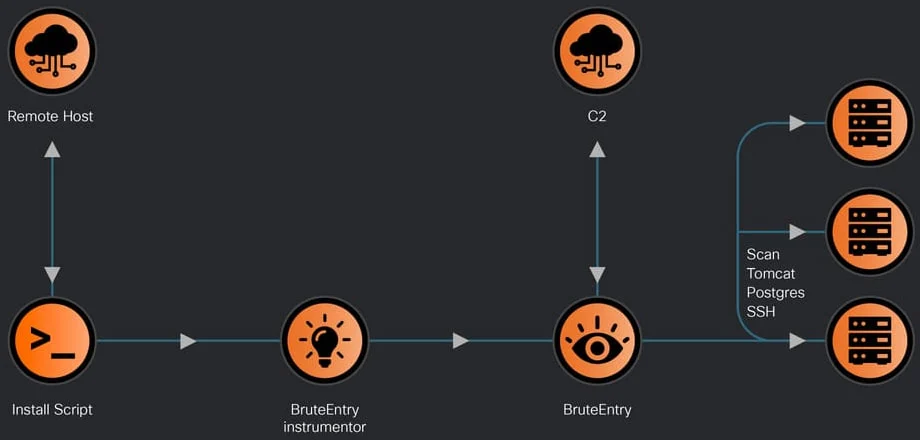
Then there is BruteEntry. Talos says this Go-based malware includes an instrumentor binary and a brute-forcing component that converts compromised systems into scanning nodes. Those nodes then probe new targets and brute-force services including SSH, Postgres, and Tomcat, while sending results and task notes back to the command-and-control infrastructure.
Why telecom networks keep showing up in China-linked campaigns
Telecom providers remain prime targets because they offer visibility, scale, and strategic access. CISA and partner agencies warned in late 2025 that Chinese state-sponsored actors were compromising networks worldwide to support global espionage, including telecommunications and other critical infrastructure.
That warning lines up closely with what Talos describes here. UAT-9244 focused on South American telecom providers, used malware that can live on Windows, Linux, and edge systems, and expanded access through scanning and brute force once it got in. The pattern matches long-term espionage tradecraft rather than quick smash-and-grab operations.
U.S. agencies have warned for years that PRC-linked actors frequently target network providers and telecommunications companies by exploiting exposed devices and weakly defended edge systems. A joint NSA, CISA, and FBI advisory in 2022 highlighted that exact pattern, and newer CISA guidance continues to stress the risk from internet-facing infrastructure and edge appliances.
What defenders should pay attention to
This campaign is notable for three reasons.
- It spans Windows, Linux, and edge devices instead of relying on a single environment.
- It uses new malware families rather than recycled public tooling.
- It turns infected systems into ORB infrastructure that can help widen the campaign.
Talos also published indicators of compromise for UAT-9244, which defenders can use to hunt for activity and block known artifacts. Cisco maintains a public IOC repository tied to its research posts, which gives blue teams a direct path to operationalize the findings.
For telecoms and other operators with a lot of unmanaged edge equipment, the biggest lesson is simple: do not treat network appliances as second-class assets. CISA recently warned that unsupported edge devices are especially vulnerable because they sit at the perimeter and often miss timely patching and modern monitoring coverage.
Key takeaways
- Cisco Talos says UAT-9244 has targeted South American telecom providers since 2024.
- Talos links the group with high confidence to China-nexus activity and says it closely overlaps with FamousSparrow and Tropic Trooper.
- The campaign uses three newly documented malware families: TernDoor, PeerTime, and BruteEntry.
- PeerTime’s BitTorrent-based command and control and BruteEntry’s ORB-building role make this toolkit unusual.
- Government agencies continue to warn that Chinese state-backed actors are pursuing long-term access inside telecom and critical infrastructure networks.
FAQ
Cisco Talos tracks UAT-9244 as a China-nexus advanced persistent threat actor and says it has high confidence the cluster closely overlaps with FamousSparrow and Tropic Trooper activity.
Talos says the campaign targeted telecommunications service providers in South America, including Windows, Linux, and network-edge environments.
TernDoor is a Windows backdoor that Talos says supports remote shell access, file actions, process execution, persistence, and self-uninstall behavior.
Talos says PeerTime is a Linux backdoor that uses the BitTorrent protocol for command and control and supports several architectures common in embedded and edge devices.
BruteEntry helps turn compromised devices into scanning and brute-force nodes, or ORBs, that can probe services such as SSH, Postgres, and Tomcat for new footholds.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages