PXA Stealer attacks on financial firms are rising. Here is how the campaign works

Financial firms face a fresh infostealer problem. Researchers say threat actors have increased their use of PXA Stealer in recent months, with phishing emails and ZIP downloads playing a central role in attacks aimed at banks and other financial organizations. CyberProof says it observed a notable rise in activity during the first quarter of 2026, after disruption hit several other major infostealer operations in 2025.
The short answer is yes, this campaign matters. PXA Stealer can steal browser credentials, saved passwords, session data, and cryptocurrency wallet information, then send stolen data to attacker-controlled Telegram infrastructure. Earlier security research also tied PXA Stealer to broad, international targeting and described it as a Python-based infostealer with strong evasion features.
In the campaign CyberProof analyzed, victims received phishing emails that pushed them toward malicious URLs and ZIP archives. The lures varied widely, including resumes, software installers, tax documents, and legal paperwork, which makes simple keyword-based email filtering less effective.
Why this campaign stands out
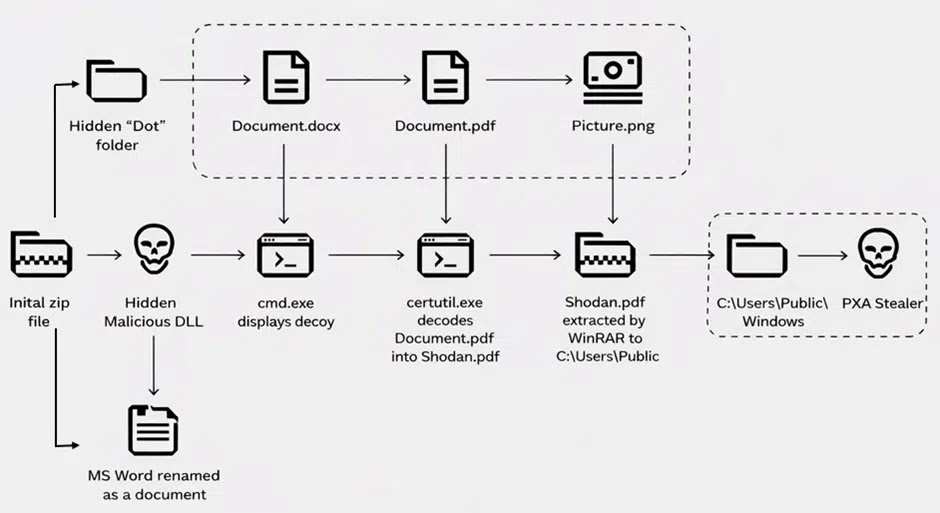
This activity stands out because it blends familiar phishing tactics with a layered infection chain. CyberProof’s write-up says one investigated sample used a ZIP archive that delivered a disguised executable, then unpacked additional components including a Python interpreter, scripts, and hidden files stored in a folder named “Dots.”
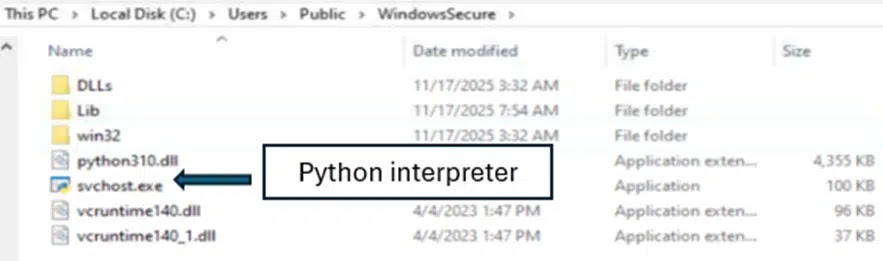
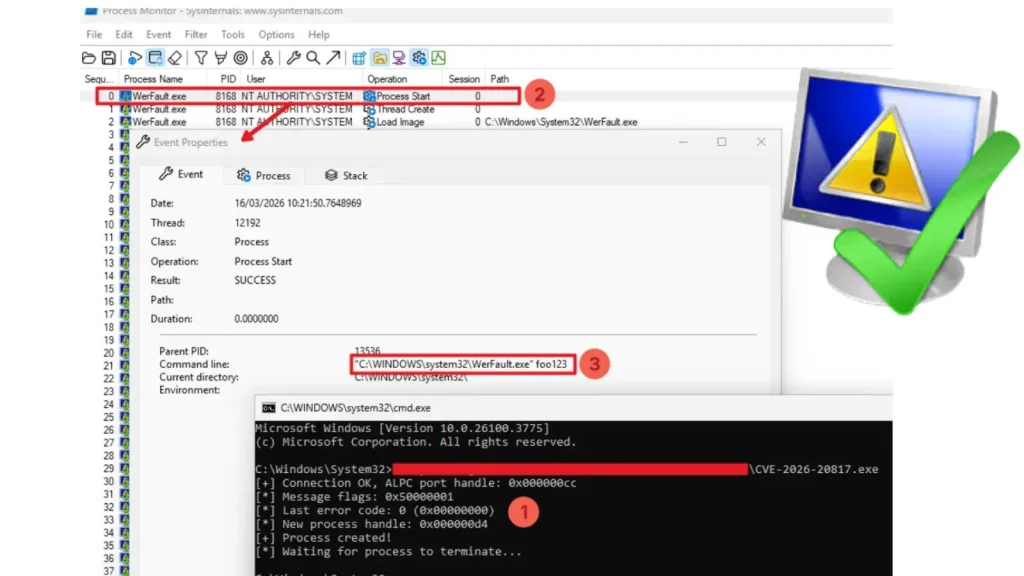
The attackers also abused legitimate Windows utilities and renamed files to look harmless or trustworthy. According to CyberProof, the chain involved certutil for decoding content, a renamed WinRAR binary, and a Python interpreter dropped under the name svchost.exe, all of which can help the malware blend into normal system activity.
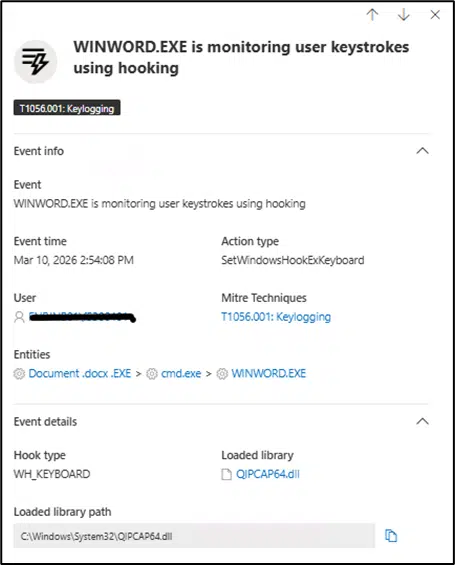
That combination matters for defenders because it reduces noise. Security teams may miss the attack if they only look for obviously malicious filenames or a single malware family signature. SentinelOne’s earlier research on PXA Stealer also described its Telegram-centered ecosystem and data theft capabilities, which supports the broader picture of a mature and adaptable infostealer operation.
How the infection chain unfolds
CyberProof says the attack can begin with a phishing email that leads the target to download a ZIP archive from an attacker-controlled domain. Inside that archive sits a file made to resemble a normal document, but it actually launches the malware chain once the victim opens it.
From there, the malware extracts tools and scripts, creates hidden storage locations, and unpacks further payloads. One analyzed case used an encrypted archive disguised as a PDF, then unpacked it with a hard-coded password before dropping files into a public Windows path.
The final objective is theft and exfiltration. CyberProof says the malware hooks into browsers to capture credentials and wallet data during active sessions, then sends that information out through Telegram channels. That matches earlier reporting from SentinelOne and Cisco Talos that described PXA Stealer as a flexible credential and information theft platform.
Key facts at a glance
| Item | Verified detail |
|---|---|
| Malware family | PXA Stealer, a Python-based infostealer |
| Main target in this campaign | Global financial institutions, according to CyberProof |
| Initial access | Phishing emails leading to malicious URLs and ZIP downloads |
| Common lures | Resumes, installers, tax files, legal documents |
| Data targeted | Browser credentials, passwords, wallet data, session-linked information |
| Exfiltration path | Telegram infrastructure/channels used by attackers |
| Evasion methods | Legitimate Windows tools, renamed binaries, hidden folders, obfuscated scripts |
What financial firms should do now
- Tighten email controls around ZIP, RAR, and executable downloads delivered through links.
- Flag document-like filenames that end in executable extensions, especially inside compressed archives.
- Audit outbound connections to Telegram and review whether any business need justifies that traffic from sensitive endpoints.
- Monitor for suspicious use of
certutil, renamed archiving tools, and unexpectedsvchost.exeinstances running from non-standard paths. This point is an inference based on the infection chain CyberProof documented. - Keep threat hunting queries and endpoint detections current for PXA Stealer behaviors, not only file hashes.
FAQ
PXA Stealer is a Python-based information-stealing malware family. Researchers have linked it to credential theft, browser data theft, and Telegram-based exfiltration.
They hold credentials, payment data, internal access tokens, and high-value account information. CyberProof says the campaign it analyzed deliberately targeted financial institutions during Q1 2026.
Not necessarily. In the campaign CyberProof described, phishing emails often contained malicious URLs that led users to download ZIP archives, rather than attaching the payload directly.
Researchers say Telegram helps operators manage stolen data and communications in a way that can blend into allowed network traffic or evade shallow inspection.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages