MuddyWater-style campaign scanned 12,000 systems before hitting Middle East critical sectors

A new cyber campaign with tactics that resemble MuddyWater scanned more than 12,000 internet-facing systems before moving into targeted attacks against critical organizations in the Middle East. Reporting tied to Oasis Security says the operation hit aviation, energy, and government targets, and at least one Egyptian aviation organization suffered confirmed data theft.
The campaign appears to have started in early February 2025 and followed a clear sequence. The attackers first mapped exposed systems, then carried out Outlook Web Access brute-force activity, and later staged and exfiltrated sensitive files from selected victims.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What makes this case stand out is the scale of the prep work. This was not a quick smash-and-grab operation. The attacker reportedly combined mass scanning, recent CVE exploitation, credential attacks, and a modular command-and-control setup that researchers say overlaps with patterns long associated with MuddyWater activity.
How the operation worked
Researchers say the group weaponized at least five recently disclosed flaws during the early access phase. Public reporting on the campaign lists Laravel Livewire flaw CVE-2025-54068, SmarterMail flaw CVE-2025-52691, n8n RCE CVE-2025-68613, an RMM session issue tracked as CVE-2025-9316, and Langflow RCE CVE-2025-34291.
Two of those bugs have clear official records that show why they matter. NVD says CVE-2025-54068 can let unauthenticated attackers reach remote command execution in certain Livewire v3 scenarios, while NVD says CVE-2025-52691 can let unauthenticated attackers upload arbitrary files to SmarterMail servers and potentially achieve remote code execution.
After scanning and exploitation attempts, the attackers shifted to credential operations. The campaign allegedly used custom OWA brute-force tooling and Patator against organizations in Egypt, Israel, and the United Arab Emirates, with one Egyptian firefighting enterprise and at least one UAE target reportedly affected during the credential-harvesting stage.
| Stage | What researchers say happened | Why it matters |
|---|---|---|
| Reconnaissance | More than 12,000 exposed systems scanned | Shows broad target discovery before intrusion |
| Initial access | Exploitation of multiple recent CVEs | Gives attackers several entry paths |
| Credential attacks | OWA brute-force and username enumeration | Helps move from internet exposure to real accounts |
| Post-compromise | File staging and exfiltration | Indicates espionage or intelligence collection |
| C2 operations | Python and Go controllers over TCP, UDP, and HTTP | Suggests a flexible and resilient toolset |
What was stolen and who was targeted
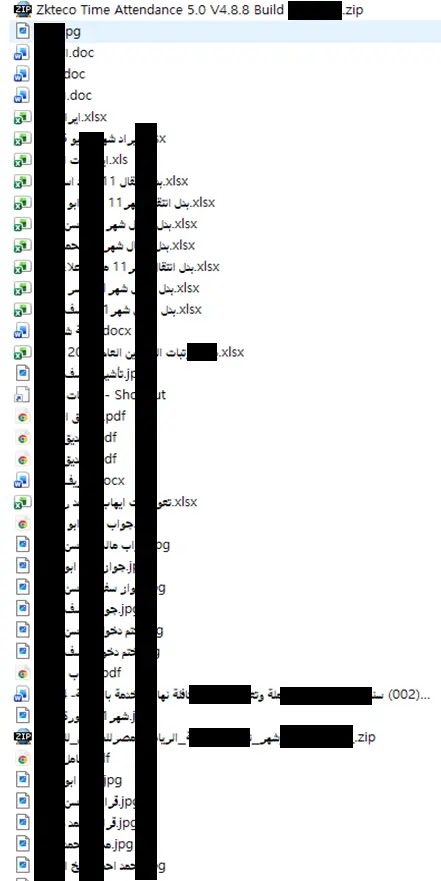
The strongest reported impact involves an aviation organization in Egypt. Researchers say attackers staged roughly 200 files in directories they controlled before data left the environment, including passport and visa records, payroll data, salary information, credit card data, and internal corporate documents.
The campaign focused heavily on Middle East critical sectors, but the targeting did not stop there. Reporting also points to activity involving organizations in Portugal and India, which suggests the infrastructure served a wider collection mission even if the highest-priority victims sat in the Middle East.
Researchers also traced attacker infrastructure to a server in the Netherlands and found server-side files that pointed to a larger coordinated operation. That infrastructure reportedly contained command-and-control components, scripts, and evidence of structured scanning activity rather than isolated attacks.
Why researchers are linking it to MuddyWater
The attribution here stays careful. Public summaries describe the activity as bearing strong operational similarities to MuddyWater, not as a final public attribution backed by a government indictment. Still, the overlap is serious enough that defenders should pay attention.
MITRE describes MuddyWater as a cyber-espionage group assessed to be part of Iran’s Ministry of Intelligence and Security, with a long record of targeting government and private organizations across the Middle East, Asia, Africa, Europe, and North America. CISA has also publicly warned that MuddyWater actors conduct cyber espionage against government and commercial networks.
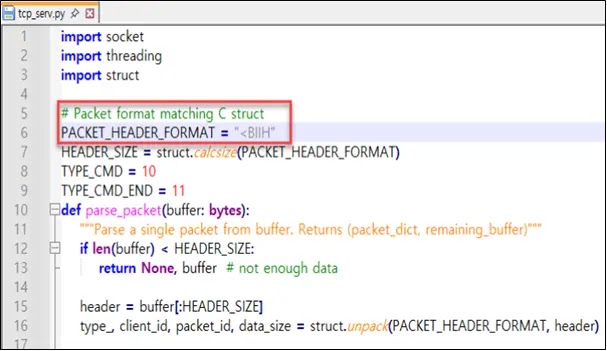
The technical overlap matters too. Reporting on this campaign says the attackers used a custom packet structure, Python-based TCP and UDP controllers, and Go-based binaries handling AES-CTR-encrypted exchanges over HTTP-style endpoints such as /signup and /feed. Those patterns reportedly line up with the ArenaC2 framework associated with earlier MuddyWater tradecraft.
Reported technical indicators highlighted in public coverage
- TCP controller listening on port 5009
- Python controllers named
tcp_serv.pyandudp_3.0.py - Go-based binaries including
serverandclient.exe - HTTP-like endpoints such as
/command,/result,/signup, and/feed - Cookie-based client identifiers and AES-CTR encrypted exchanges
What defenders should do now
Organizations that expose OWA, web apps, email systems, RMM tools, or workflow platforms should treat this campaign as a warning that speed matters. Attackers appear to have chained together internet scanning, public bug exploitation, and credential abuse in one workflow, which means defenders need visibility across all three stages rather than focusing on malware alone.
The first step is patching. NVD and national advisories already document the seriousness of flaws like CVE-2025-54068 and CVE-2025-52691, and CISA’s Known Exploited Vulnerabilities catalog also lists Livewire CVE-2025-54068, which raises the urgency even further.
Teams should also review OWA logs for brute-force attempts, watch for suspicious outbound traffic on port 5009, inspect unusual encrypted connections to unfamiliar endpoints, and check for large staging directories that may signal collection ahead of exfiltration. Those steps line up with the attack path researchers described in the campaign summaries.
Immediate checks for defenders
- Patch exposed internet-facing apps and mail systems
- Audit OWA sign-in logs for password spraying or brute-force patterns
- Hunt for outbound traffic on TCP port 5009
- Review web server and proxy logs for unusual
/signup,/feed,/command, or/resulttraffic - Search for newly created staging folders holding bulk sensitive files
- Reset exposed credentials and enforce MFA where possible
FAQ
Researchers say a MuddyWater-like actor scanned over 12,000 internet-exposed systems, exploited recent vulnerabilities, brute-forced OWA accounts, and stole data from selected targets in the Middle East.
Public reporting describes the campaign as having strong similarities to MuddyWater. The available coverage does not present a final official public attribution from a government agency for this specific operation.
The reported targets include aviation, energy, and government organizations, with confirmed exfiltration from at least one Egyptian aviation entity.
Researchers said the staged files included passport and visa records, payroll and salary data, credit card information, and internal corporate documents.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages