ATHR turns callback phishing into a packaged AI vishing operation

A cybercrime platform called ATHR appears to package the full callback-phishing chain into one browser-based system, making it easier for attackers to run phone-led scams at scale. Abnormal Security says ATHR combines phishing email delivery, AI voice agents, credential harvesting pages, and a live operator dashboard inside a single platform built for Telephone-Oriented Attack Delivery, or TOAD.
That matters because TOAD attacks shift the dangerous part of the scam away from the email itself and onto a phone call. The email may contain nothing more than a phone number and a fake account alert, which helps it slip past traditional filters that look for malicious links or attachments.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
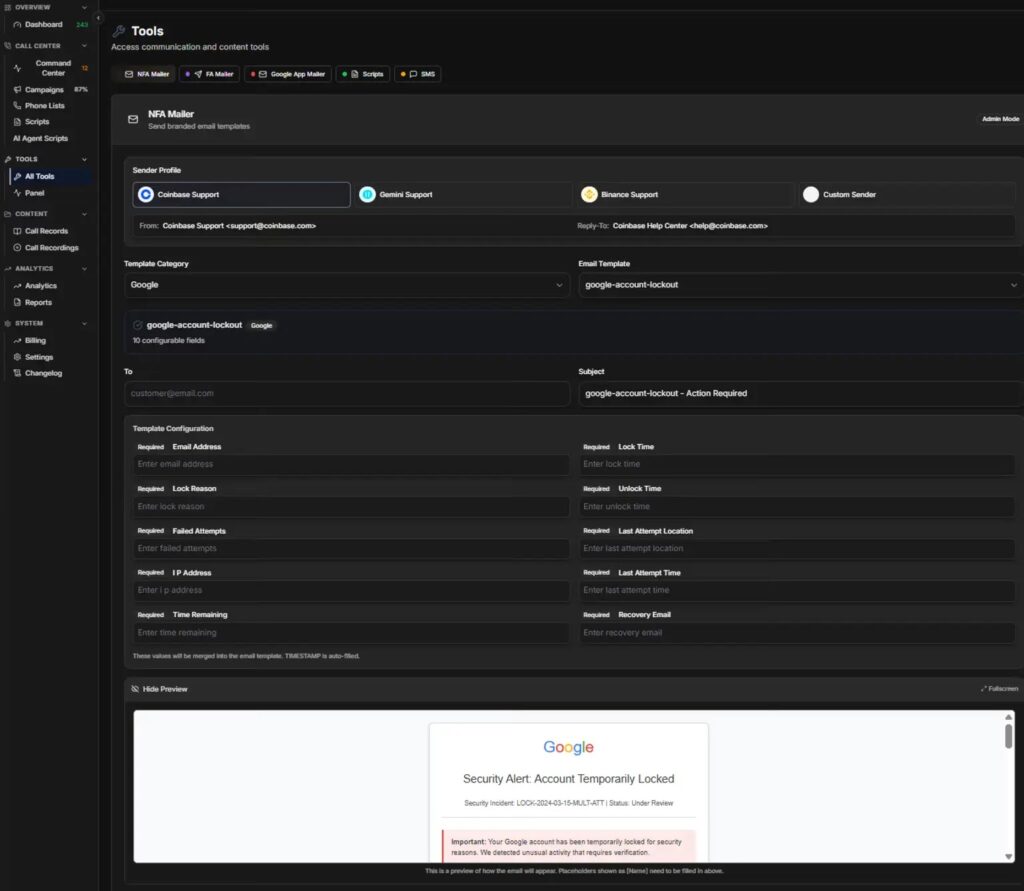
Abnormal says ATHR lowers the skill and coordination needed to run this kind of campaign by putting every stage in one interface. In the company’s April 16 research note, its analysts say the platform was advertised for $4,000 plus 10% of profits and supported phishing pages for brands including Google, Microsoft, Yahoo, AOL, Coinbase, Binance, Gemini, and Crypto.com.
How ATHR works
According to Abnormal, ATHR starts with a built-in mailer that sends account-alert style emails designed to look routine and urgent at the same time. The research says one prebuilt Google lure used a “Security Alert: Account Temporarily Locked” template with customizable fields such as timestamp, IP address, and location.
The victim then calls the number in the email instead of clicking a link. Abnormal says the call can route to either a human operator or an AI voice agent that follows a scripted flow, starting with callback verification, then a fake account-recovery process, and finally a request for a six-digit code or other credentials.
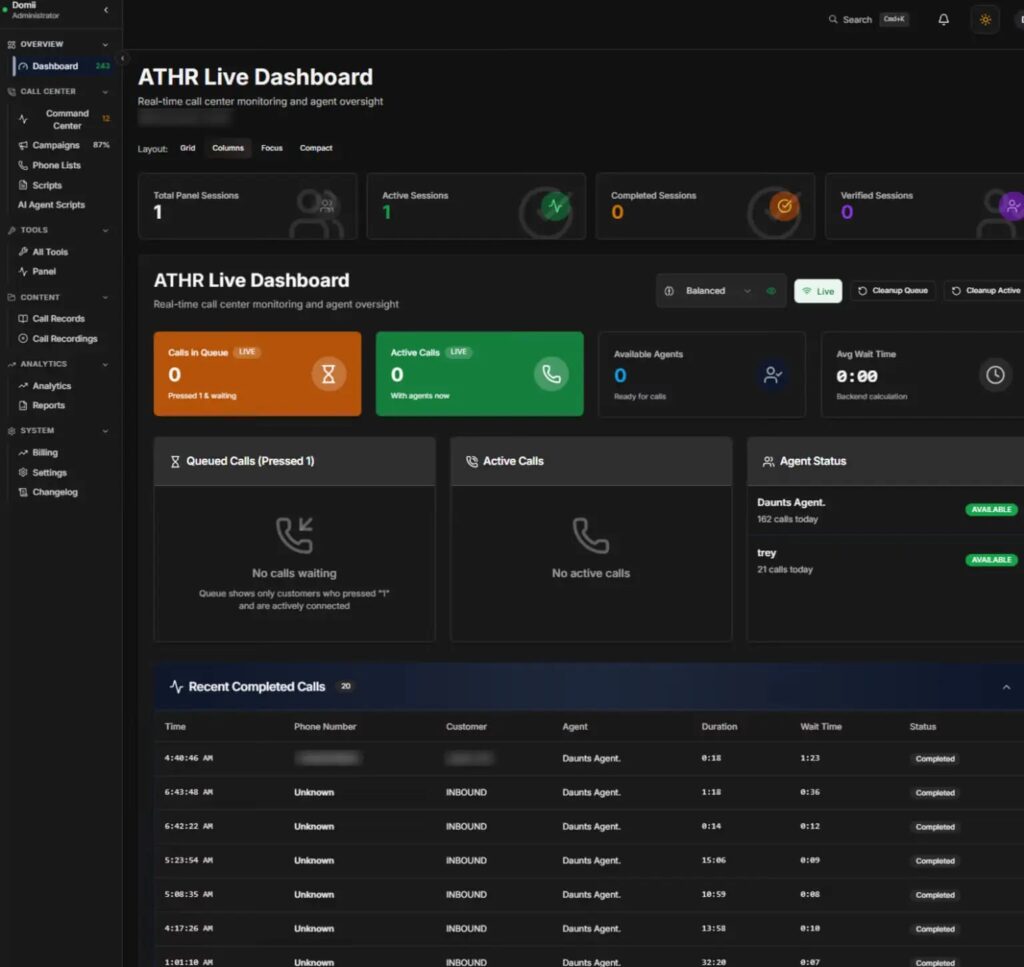
At the same time, the operator can steer the target to a fake login page and collect credentials in real time. Abnormal says the platform’s live dashboard displayed 243 total interactions, 12 active sessions, and 87% campaign utilization in one captured view, which suggests ongoing operational use rather than a proof of concept.
Why researchers see this as an escalation
The most notable change is automation. Abnormal says earlier TOAD operations often required separate tools for email delivery, phone handling, and credential capture, while ATHR folds those parts into one service that one operator can manage more easily.
The platform also appears to use an in-house text-to-speech system called ATHR TTS with a model labeled Sonic 3. Abnormal says the result sounds natural enough to mimic a real support call, which raises the odds that a nervous recipient will trust the voice on the line.
This fits a broader pattern in callback phishing. CISA’s phishing guidance says criminals increasingly use channels that avoid obvious malicious content in the initial message, while the FBI warns that spoofing can involve fake phone numbers and trusted brands to push victims into direct contact with scammers.
What makes TOAD hard to stop
A callback-phishing email can pass standard technical checks because the message may contain no attachment and no malicious URL. Your sample article noted that point, and Abnormal makes the same case directly by saying ATHR lures can pass SPF, DKIM, and DMARC while still pushing victims into a phone-based social-engineering trap.
That means email authentication alone does not settle the question of trust. CISA tells users to verify suspicious requests through official channels instead of using contact details supplied in the message, which lines up closely with the core defense against ATHR-style lures.
The danger rises further when the attacker controls both the call and the fake login page. Abnormal says ATHR gives operators a single workspace where they can watch calls unfold, answer objections, and capture usernames, passwords, and one-time codes while the victim still thinks they are dealing with a legitimate support process.
Key details
| Item | Details |
|---|---|
| Platform name | ATHR |
| Attack style | Telephone-Oriented Attack Delivery, or TOAD |
| Main components | Built-in mailer, AI voice agent, credential panels, operator dashboard |
| Reported price | $4,000 plus 10% of profits |
| Brands named by researchers | Google, Microsoft, Yahoo, AOL, Coinbase, Binance, Gemini, Crypto.com |
| Core evasion tactic | Email contains a phone number instead of a malicious link or file |
| Main risk | Real-time credential theft over a phone-led workflow |
Sources: Abnormal Security research and follow-on reporting.
What organizations should do
- Train users not to call numbers listed in unexpected security-alert emails. Tell them to open the company’s official website or app and find support details there instead.
- Flag clusters of inbound emails that share the same callback number across many recipients. Abnormal says repeated phone-number reuse can expose a campaign even when message content varies.
- Treat successful SPF, DKIM, and DMARC checks as only one signal, not final proof that an alert is safe. Abnormal says ATHR lures can pass those checks.
- Use behavioral detection that looks for unusual sender-recipient patterns and abnormal message intent, especially messages that push urgent phone contact. Abnormal argues that behavior-based analysis is better suited to this attack style than simple content scanning.
- Tell employees never to share passwords, MFA codes, or recovery codes over the phone. Several public TOAD advisories make the same point because the phone call is where the attacker tries to close the scam.
FAQ
Abnormal describes ATHR as a cybercrime platform built to automate TOAD attacks by combining phishing emails, AI vishing, credential capture, and operator controls in one interface.
TOAD stands for Telephone-Oriented Attack Delivery. It is a phishing method where the email pushes the victim to call a phone number, and the real social engineering happens during that call.
Because they may not include a malicious link or file. The email looks simple, while the credential theft happens later over the phone and on attacker-controlled pages.
Do not call the number in the message. Find the company’s official contact details independently and verify the alert there.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages