Attackers abuse AppDomain hijacking to turn signed Intel utility into stealth malware loader

A newly documented intrusion campaign shows how attackers can turn a legitimate signed Intel utility into a stealth malware launcher without modifying the original binary. CYFIRMA says the operation, which it calls PhantomCLR, abuses the .NET AppDomainManager mechanism so malicious code runs before the trusted Intel program begins its normal logic.
The technique matters because it shifts the trust problem away from the executable itself. In this case, the attackers place a weaponized configuration file next to IAStorHelp.exe, a real Intel-signed utility, and use normal .NET runtime behavior to load an attacker-controlled DLL during startup. CYFIRMA says the malicious chain needs no code tampering, no registry trick to launch, and no exploit against the Intel binary itself.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
CYFIRMA says the campaign has targeted organizations in the Middle East and in parts of the EMEA financial sector through spear-phishing emails carrying a ZIP archive. The archive reportedly contains the signed Intel binary, the poisoned config file, a malicious .NET DLL, an encrypted payload blob, a disguised shortcut, and a decoy PDF used to distract the victim.
How the attack starts
According to CYFIRMA, the victim receives a phishing email with a ZIP archive that looks business-related. Inside is a shortcut disguised as a PDF, which launches the Intel binary while opening a decoy document so the activity appears normal.
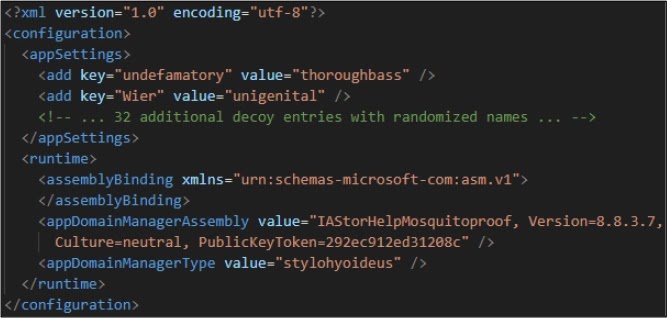
The important detail comes next. CYFIRMA says the .NET runtime automatically checks for a matching .config file in the same folder as the executable. The attackers exploit that expected behavior with IAStorHelp.exe.config, which instructs the runtime to load IAStorHelpMosquitoproof.dll through the AppDomainManager mechanism before the host application’s main code executes.
That design makes the attack unusually quiet. Security tools may see a trusted Intel-signed process start, while the real malicious logic runs earlier inside the same CLR initialization flow. This is one reason AppDomain hijacking remains a serious detection challenge in .NET-heavy environments. That conclusion is an inference based on CYFIRMA’s execution analysis.
Why AppDomain hijacking is effective
CYFIRMA says the attackers rely on a malicious <runtime> block inside the config file to specify a rogue assembly and initialization class. Because the runtime honors those settings during application startup, the malicious DLL gains an early foothold without patching the legitimate binary or dropping extra launch scripts.
The report also says the signed host binary’s trust does not extend to verifying the safety of every assembly loaded through this path. In practice, that means a valid signed executable can become the delivery vehicle for unsigned malicious code if defenders focus only on the binary’s signature and not the runtime environment around it.
This gives attackers a useful blend of legitimacy and stealth. They borrow trust from a signed enterprise utility, then let the runtime itself do the work of bringing hostile code into memory. That is more subtle than simply replacing a binary and often harder to catch with basic allowlisting. This is an inference supported by CYFIRMA’s description of the trust chain.
What happens after execution
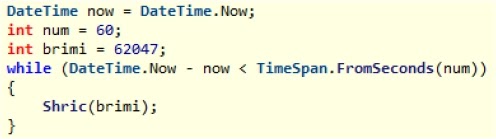
CYFIRMA says the malware uses a multi-stage framework designed to delay obvious malicious behavior and frustrate analysis. The report describes two timing gates, including a CPU-heavy prime calculation and a long iterative key-derivation loop, which together appear intended to burn sandbox time before the final payload becomes visible.
Once decrypted, the payload reportedly executes in memory and uses just-in-time trampoline logic rather than obvious standard allocation paths that many tools monitor closely. CYFIRMA also describes noisy DLL-loading behavior and later memory cleanup steps meant to make forensic reconstruction harder after the malicious stages finish.
On the network side, CYFIRMA says command-and-control traffic used Amazon CloudFront infrastructure and an associated AWS load balancer backend, helping the malicious traffic blend in with normal cloud activity. That does not make the traffic benign, but it does make simple reputation-based blocking less effective on its own.
What researchers are and are not saying
CYFIRMA compares the framework’s post-exploitation maturity to commercial offensive tools such as Cobalt Strike and Brute Ratel C4. At the same time, the firm says it has not directly attributed the campaign to a known threat actor. That distinction matters because the tooling quality suggests a capable operator, but the public evidence stops short of naming a specific group.
So the safest conclusion is narrower. This looks like a disciplined, well-resourced operation that knows how to abuse trusted execution paths, but public reporting does not yet support a firm actor attribution.
At a glance
| Item | Verified detail |
|---|---|
| Research source | CYFIRMA |
| Campaign name | Operation PhantomCLR |
| Signed binary abused | IAStorHelp.exe |
| Main technique | AppDomainManager hijacking via malicious .config |
| Initial access | Spear-phishing ZIP with disguised .pdf.lnk |
| Malicious DLL named in report | IAStorHelpMosquitoproof.dll |
| Network layer noted | CloudFront plus AWS ELB infrastructure |
| Attribution status | No direct public attribution to a known actor |
What defenders should watch for
Teams should look for trusted .NET executables running from user-writable locations with unexpected sidecar .config files. In this campaign, the poisoned config file is the real trigger, not a visibly tampered host binary.
Security teams should also hunt for suspicious .pdf.lnk files, Intel-signed utilities launched from unusual directories, and non-browser processes making outbound HTTPS connections to CloudFront or related cloud infrastructure. Those signals do not prove compromise by themselves, but CYFIRMA’s report shows they fit the observed chain.
For detection engineering, this campaign is a reminder that signed binary trust alone is not enough. Defenders need visibility into .NET configuration behavior, unusual CLR initialization paths, and side-loaded runtime components that appear next to otherwise legitimate software. This is an inference based on the attack design CYFIRMA documented.
Key takeaways
- CYFIRMA says attackers abused AppDomainManager hijacking to force early execution of malicious code through a poisoned config file.
- The attack used a legitimate Intel-signed utility, IAStorHelp.exe, as the trusted host process.
- The phishing archive reportedly contained the signed binary, config file, malicious DLL, encrypted payload, disguised shortcut, and decoy PDF.
- Public reporting describes a mature framework, but there is no direct attribution to a known threat actor yet.
FAQ
It is abuse of .NET runtime configuration so attacker-controlled code loads during application startup, before the legitimate program’s normal logic runs. CYFIRMA says this campaign used the AppDomainManager mechanism for that purpose.
CYFIRMA says no. The attack used a legitimate signed Intel binary and placed a malicious config file beside it to redirect runtime behavior.
Because the visible executable is trusted and signed, while the malicious behavior starts inside normal CLR initialization. That can reduce the chance of simple signature-based or allowlist-only controls catching it. This is an inference based on CYFIRMA’s reported execution flow.
No. CYFIRMA describes a sophisticated framework and compares its maturity to known offensive toolkits, but says there is no clear direct attribution to a known actor.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages