Gh0st RAT and CloverPlus adware arrive together in new dual-payload malware campaign

A newly documented malware campaign is delivering two very different threats in one infection chain: Gh0st RAT for long-term remote control and CloverPlus adware for quick monetization. Splunk Threat Research Team says the pairing gives attackers both persistent access to the compromised system and a fast way to profit from it through unwanted browser changes and ad activity.
The campaign stands out because it reflects a broader shift in malware operations. Instead of dropping a single tool and moving on, the loader hides two encrypted payloads in its resource section and deploys them in sequence, allowing one infection to serve both espionage-style access and nuisance-driven revenue generation.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Splunk says the first payload is CloverPlus adware, detected as AdWare.Win32.CloverPlus, while the second is a Gh0st RAT client module that gets decrypted and launched later in the chain. That makes this less of a simple adware case and more of a bundled intrusion that can disrupt users immediately while also leaving a backdoor behind.
How the loader works
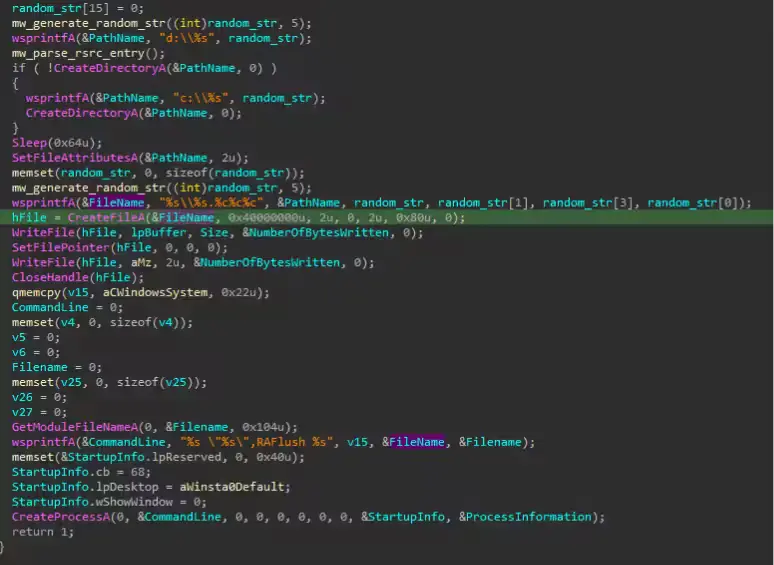
According to Splunk, the loader uses obfuscation to conceal both encrypted payloads inside its resource section. After it handles the CloverPlus adware component, it checks whether it is running from the %temp% folder and, if not, drops a copy of itself there before moving to the next stage.
The next step focuses on Gh0st RAT. Splunk says the malware decrypts a DLL stored as a resource, creates a random file name and extension, places it inside a randomly named folder at the root of the C:\ drive, and then runs it through rundll32.exe. That execution choice helps the malware blend into normal Windows activity by using a legitimate system binary.
This is one reason defenders should pay close attention to parent-child process relationships and odd DLL execution paths. A trusted Windows process starting code from unusual locations can signal a loader trying to stay quiet while it stages a more serious payload. This last point is an inference based on Splunk’s execution flow and common defensive practice.
Why Gh0st RAT still matters
Gh0st RAT is not a new malware family, but it remains useful to attackers because its source code is public and many variants still offer broad remote access features. MITRE ATT&CK classifies gh0st RAT as malware that has been used by multiple groups, which helps explain why it continues to resurface in new campaigns and bundled delivery chains.
In this case, Splunk’s analysis shows the RAT doing much more than sitting quietly on the host. The researchers describe behavior tied to privilege adjustment, system and network discovery, DNS manipulation, persistence through registry Run keys, and service-based execution paths that can give the malware a stronger foothold after reboot.
That combination makes the adware piece look almost secondary. CloverPlus may generate fast money and visible browser disruption, but Gh0st RAT is what turns the infection into a longer-term security problem with the potential for continued surveillance, system tampering, and follow-on abuse. This conclusion is an inference drawn from Splunk’s malware behavior analysis and MITRE’s description of gh0st RAT.
What the malware does after launch
Splunk says this Gh0st RAT variant adjusts token privileges, gathers host details such as MAC address and drive serial information, and uses those values to help identify victims inside the attacker’s infrastructure. The report also describes behavior that interferes with DNS resolution and can block access to some security-related domains.
The malware also uses persistence methods that defenders should recognize quickly. Splunk says it writes to the Windows Run registry key and abuses the Windows Remote Access service path to load a malicious DLL with elevated privileges, helping it survive reboots and operate with more power on the system.
Taken together, the campaign shows how attackers are getting more efficient. A single obfuscated loader now gives them ad fraud, user disruption, and a durable remote foothold, all from one initial delivery path.
At a glance
| Item | Verified detail |
|---|---|
| Research source | Splunk Threat Research Team |
| First payload | CloverPlus adware |
| Second payload | Gh0st RAT client module |
| Hiding method | Encrypted payloads in the resource section |
| Execution method for RAT | Decrypted DLL launched via rundll32.exe |
| Persistence noted | Run key changes and Windows service abuse |
| Key risk | Immediate monetization plus long-term system access |
What defenders should watch for
Security teams should monitor for rundll32.exe launching DLLs from random folders, especially from unusual locations under C:\ or after activity tied to %temp%. Splunk’s analysis shows that this execution pattern is central to how the Gh0st RAT payload gets started.
Registry changes also matter here. Splunk says the malware uses Run keys and RemoteAccess-related service paths for persistence, so defenders should flag unexpected writes in those areas and investigate any service-related DLL references that do not match known-good software.
Teams should also look closely at DNS anomalies, blocked access to security domains, and suspicious browser changes that seem like adware at first glance. In this campaign, the visible nuisance may be the easiest clue that a more serious RAT payload is already active underneath. This is an inference based on the dual-payload design Splunk described.
Key takeaways
- Splunk says one loader is now delivering both CloverPlus adware and Gh0st RAT in the same campaign.
- The loader hides both payloads in its resource section and later runs the RAT through rundll32.exe.
- The campaign combines quick monetization with a persistent backdoor on the same machine.
- Defenders should focus on odd DLL execution, persistence changes, and DNS-related anomalies.
FAQ
It delivers two different threats at once. Splunk says the loader drops CloverPlus adware for immediate monetization and Gh0st RAT for long-term remote access.
Yes. MITRE says gh0st RAT has public source code and has been used by multiple groups, which helps keep it relevant in new campaigns and variants.
Splunk says the loader decrypts the Gh0st RAT DLL, writes it to a randomly named location, and launches it with rundll32.exe.
Because the adware may be the most visible sign of infection, while the RAT quietly gives attackers deeper control and persistence on the same machine. This is an inference based on Splunk’s analysis of both payloads.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages