Iranian MOIS linked three hacker brands to one coordinated cyber campaign, researchers say

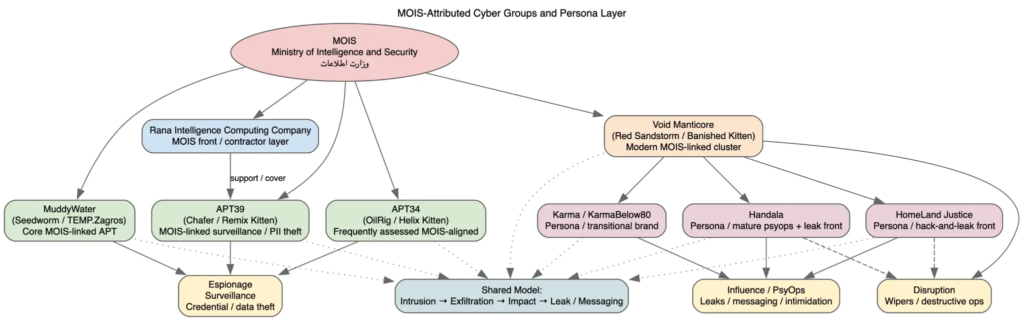
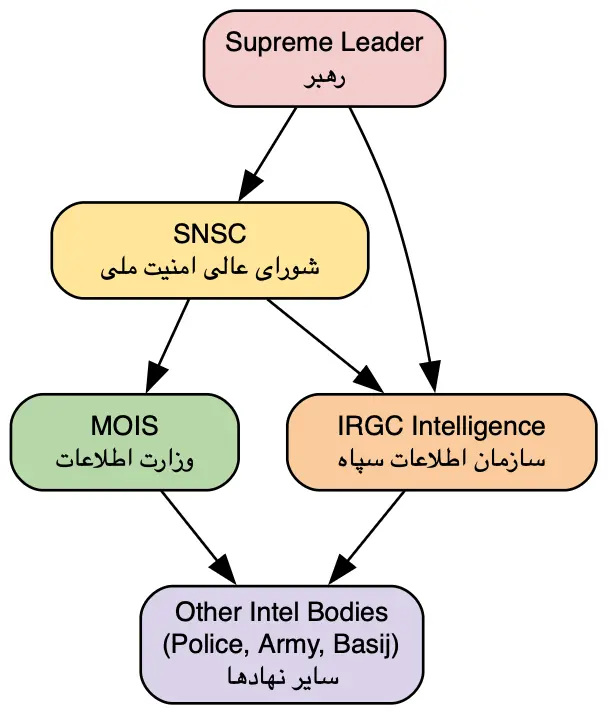
Iran’s Ministry of Intelligence and Security appears to have run Homeland Justice, Karma/KarmaBelow80, and Handala as parts of one coordinated cyber campaign, not as separate hacktivist groups. New threat intelligence from DomainTools says the three brands share infrastructure, tradecraft, timing, and messaging goals, which points to centralized direction rather than independent actors.
That finding matters because these operations did more than steal data or disrupt systems. Researchers say the actors mixed intrusion, leaks, public claims, pressure campaigns, and narrative shaping into one model built to damage targets technically and politically at the same time.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
U.S. authorities have now acted against part of that ecosystem. On March 19, 2026, the Justice Department announced the seizure of four domains it says MOIS used to claim hacks, post stolen data, and threaten dissidents, journalists, and Israeli-linked individuals: Justicehomeland[.]org, Handala-Hack[.]to, Karmabelow80[.]org, and Handala-Redwanted[.]to.
How the campaign evolved
DomainTools says the campaign first became visible under the Homeland Justice label during the 2022 attacks on Albania. The company argues that this phase established the model the group still uses now: gain access, exfiltrate data, disrupt or destroy systems, then move fast to public messaging and information operations.
That Albania link lines up with earlier U.S. government findings. CISA said in 2022 that Iranian state cyber actors identifying as Homeland Justice launched a destructive cyberattack against the Albanian government. DomainTools now places that activity inside a broader MOIS-linked ecosystem that later reappeared under Karma and Handala branding.
Researchers say the branding changed, but the operational logic did not. They point to shared infrastructure patterns, repeated use of Telegram-linked amplification, consistent naming behavior, and overlapping tactics as signs that one operator or one tightly managed apparatus kept switching masks to fit different targets and narratives.
Why Handala matters now
The Handala phase appears to push hardest on influence operations. DomainTools says Handala expanded the model beyond network intrusion into surveillance, harassment, curated leaks, and public intimidation, especially against Israeli-linked targets and critics of the Iranian regime.
The Justice Department described the same pattern in sharper legal terms. It said the seized domains supported psychological operations and transnational repression, and that Handala-linked infrastructure published personally identifiable information, issued threats, and claimed responsibility for a March 2026 destructive malware attack against a U.S.-based multinational medical technologies firm.
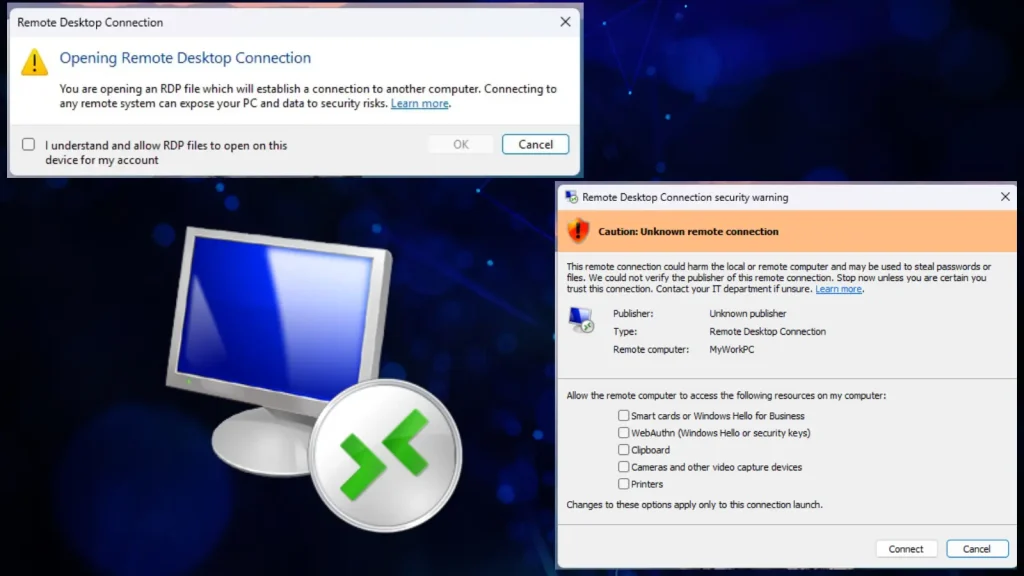
That combination gives this campaign its weight. Even when the intrusion path relies on ordinary weaknesses such as poor credential hygiene, exposed services, phishing, or weak access controls, the operators can still create outsized impact by turning every breach into a media event and a pressure campaign.
The three personas at a glance
| Persona | Main role researchers describe | Notable activity |
|---|---|---|
| Homeland Justice | Destructive and disruptive operations with public claims | 2022 Albania attacks and document leaks |
| Karma / KarmaBelow80 | Rebranded phase aimed at Israeli targets | Shifted focus in late 2023 while keeping similar tradecraft |
| Handala | Influence, leaks, intimidation, and public harassment | 2024 to 2026 operations, including activity tied to seized domains |
What defenders should watch for
Organizations should not treat these names as separate threat groups by default. The newer research suggests defenders should track the ecosystem behind the labels, not just the label itself.
Security teams should pay close attention to internet-facing services, privileged account activity, exposed identities, and any infrastructure that can feed a leak-and-amplify campaign. CISA’s earlier Albania advisory and DomainTools’ newer assessment both point to a mix of intrusion activity and public messaging, which means incident response teams need a comms plan as much as a containment plan.
The U.S. government also continues to push for reporting and attribution support. Rewards for Justice says it offers up to $10 million for information on people who, under a foreign government’s direction or control, engage in malicious cyber activity against U.S. critical infrastructure.
Practical takeaways
- Monitor leak sites, Telegram channels, and cloned public personas alongside normal IOC feeds.
- Audit privileged accounts and remote access paths aggressively.
- Assume a stolen-data incident may turn into a public pressure campaign within hours.
- Build legal, executive, and communications workflows into cyber response plans.
FAQ
Current DomainTools research says no. It assesses them as interchangeable personas inside one MOIS-linked cyber influence ecosystem.
Yes. The Justice Department said on March 19, 2026 that it seized four domains tied to the operation.
They showed the model early. The actors paired destructive cyber activity with leaks and public messaging, which turned a network intrusion into a broader political and psychological operation.
Harden exposed services, review identity controls, watch for leak-site mentions, and prepare for coordinated technical and reputational fallout, not just malware cleanup.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages