Critical Flowise flaw enables command execution through MCP adapters

Flowise users need to patch quickly. A newly disclosed vulnerability in Flowise lets an authenticated attacker execute arbitrary commands through MCP stdio adapters, and GitHub has assigned it CVE-2026-40933 with a critical 10.0 severity rating. The issue affects flowise and flowise-components through version 3.0.13, and the patched version is 3.1.0.
The bug sits in Flowise’s “Custom MCP” configuration. According to the GitHub advisory, an attacker can add an MCP stdio server with a crafted command and arguments, bypassing Flowise’s existing checks and reaching command execution on the host operating system. OX Security says it demonstrated this as a “hardening bypass” in Flowise during a broader investigation into MCP-related risks across the AI ecosystem.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This makes the Flowise issue more serious than a normal misconfiguration bug. In practice, it means a user with access to add or modify a Custom MCP entry can turn that feature into an execution path on the underlying server, which puts secrets, databases, API keys, and chat data at risk if the instance has broad access. That risk follows directly from the advisory’s command-execution description and OX’s broader research into MCP-connected services.
What the Flowise bug actually does
GitHub’s advisory says the flaw comes from unsafe serialization of stdio commands in the MCP adapter. The advisory includes an example where npx can be combined with -c and an arbitrary shell payload, which defeats the intended protections and leads to OS command execution.
The advisory also makes an important point about scope. This is not described as an unauthenticated internet-wide RCE in Flowise by itself. GitHub classifies it as an authenticated attack with low privileges, which means an attacker needs access to the Flowise environment and the ability to add an MCP configuration first.
That distinction matters because it changes the exposure model. A public Flowise instance with weak access controls, shared admin use, or overly broad internal permissions can still become a high-impact target, but the attack path is narrower than a no-login exploit.
Why MCP is part of the bigger story
OX Security says Flowise is one of several platforms affected by a wider class of MCP-related weaknesses tied to stdio command handling and trust boundaries. Its April 2026 advisory describes four exploit families and says the broader issue touches official MCP SDKs across Python, TypeScript, Java, and Rust. OX also says it reported the problem to Anthropic and recommended protocol-level changes, while Anthropic treated the behavior as expected.
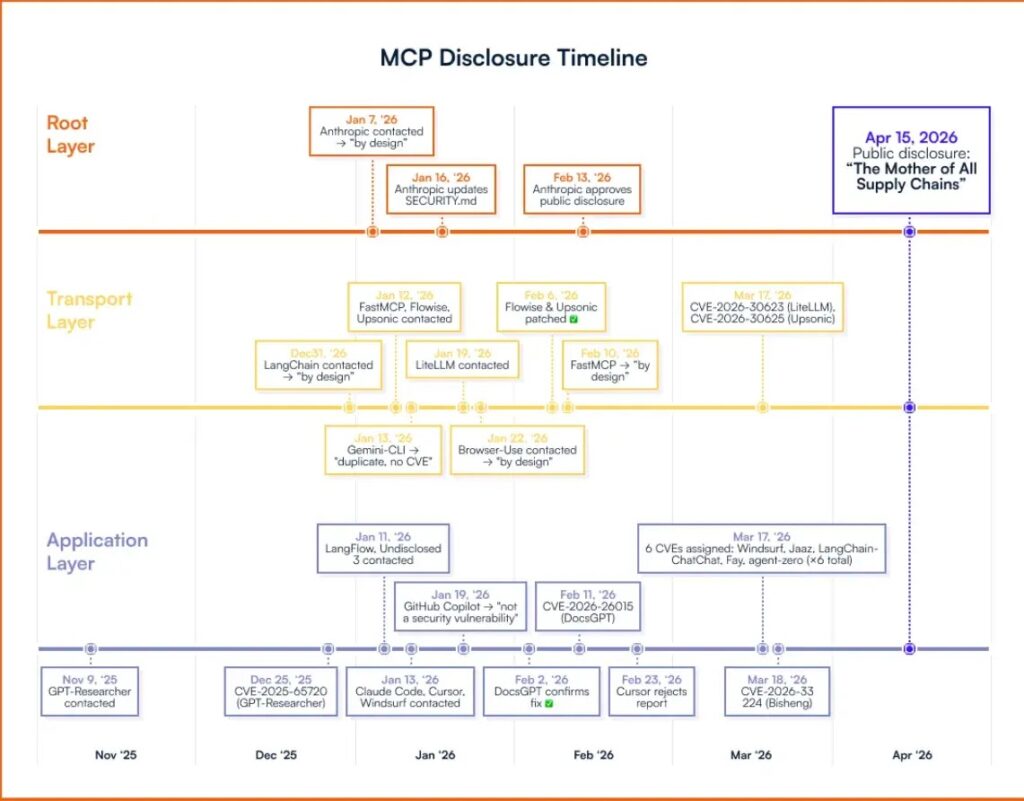
Anthropic’s own MCP materials show why this area stays sensitive. The official MCP specification says tools represent arbitrary code execution and must be treated with caution, and the security documentation stresses authorization, consent, and careful handling of untrusted servers and operations.
That does not prove every MCP implementation is equally vulnerable. It does show that MCP environments already operate in a high-trust, high-risk zone, where bad validation or unsafe command handling can turn a convenience feature into an execution path. That is an inference based on the Flowise advisory plus the MCP specification’s own security warnings.
Key facts at a glance
| Item | Verified detail |
|---|---|
| Vulnerability | CVE-2026-40933 |
| Affected product | flowise and flowise-components npm packages |
| Affected versions | <= 3.0.13 |
| Patched version | 3.1.0 |
| Severity | Critical, CVSS 10.0 |
| Attack type | Authenticated OS command execution via MCP stdio adapter configuration |
| Root cause described | Unsafe serialization and insufficient sanitization of stdio commands and arguments |
What defenders should do now
- Upgrade Flowise to version 3.1.0 or later immediately.
- Audit who can create or edit Custom MCP entries in Flowise. The advisory shows that this permission is central to exploitation.
- Treat all MCP stdio command and argument fields as untrusted input. OX specifically flags stdio configuration that includes user input as dangerous.
- Keep Flowise and similar AI orchestration platforms off the public internet unless you have strong access controls and strict segmentation. This matches OX’s mitigation guidance for MCP-connected services.
- Run MCP-enabled services with minimal OS privileges and inside sandboxed environments where possible.
Why this matters beyond Flowise
The Flowise bug is the most concrete and directly patchable part of this story. GitHub’s advisory gives defenders a clear CVE, a clear fix version, and a clear exploitation path.
The broader concern sits one layer higher. OX argues that the wider MCP ecosystem still has unresolved trust and execution problems, especially where services accept external MCP configuration, install third-party MCP servers, or let agents interact with tools that can invoke local processes.
That means patching Flowise is necessary, but it may not be enough for teams that rely heavily on MCP-based tooling. They also need tighter permission models, stricter server sourcing, and stronger isolation around anything that can spawn local commands or bridge into sensitive systems. This conclusion follows from the official Flowise advisory, OX’s disclosure, and the MCP spec’s own safety model.
FAQ
No. The GitHub advisory describes CVE-2026-40933 as an authenticated attack with low privileges, not a no-login remote exploit.
GitHub says versions up to and including 3.0.13 are affected. Version 3.1.0 contains the fix.
The issue sits in Flowise’s Custom MCP stdio adapter configuration, where unsafe command serialization lets attackers supply harmful commands and arguments.
I did not find a direct Anthropic advisory announcing a protocol-level fix for the broader OX findings during this check. OX says it recommended such changes and that Anthropic considered the behavior expected. The official MCP docs instead focus on consent, authorization, and treating tools as potentially dangerous.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages