Nexcorium botnet hits TBK DVRs through CVE-2024-3721, Fortinet says
Threat actors are actively exploiting CVE-2024-3721 in TBK DVR devices to deploy Nexcorium, a Mirai-based malware strain built for distributed denial-of-service attacks, according to new research from Fortinet FortiGuard Labs. The campaign targets TBK DVR-4104 and DVR-4216 devices and expands further by hitting end-of-life TP-Link routers through CVE-2017-17215.
The key risk is simple. A vulnerable internet-exposed DVR can turn into a botnet node through a single unauthenticated command-injection request. Fortinet says the malware then downloads the correct binary for the device architecture, establishes persistence, connects back to command-and-control infrastructure, and prepares the infected hardware for DDoS activity.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This makes the campaign more than another Mirai clone story. It shows how quickly threat actors still weaponize old, lightly managed IoT gear, especially devices that sit online for years with weak credentials, stale firmware, or no realistic patch path at all.
How the attack works
Fortinet says the campaign abuses the vulnerable /device.rsp?opt=sys&cmd=___S_O_S_T_R_E_A_MAX___ endpoint on affected TBK DVRs. The flaw allows OS command injection through crafted HTTP requests, giving attackers remote code execution without authentication. NVD also describes the issue as command injection affecting TBK DVR-4104 and DVR-4216.
After that first foothold, the malware retrieves a downloader script, checks the underlying Linux architecture, and fetches the right Nexcorium binary for the target. Fortinet says the malware supports multiple CPU architectures, which lets operators reuse the same campaign against a broad range of IoT hardware.
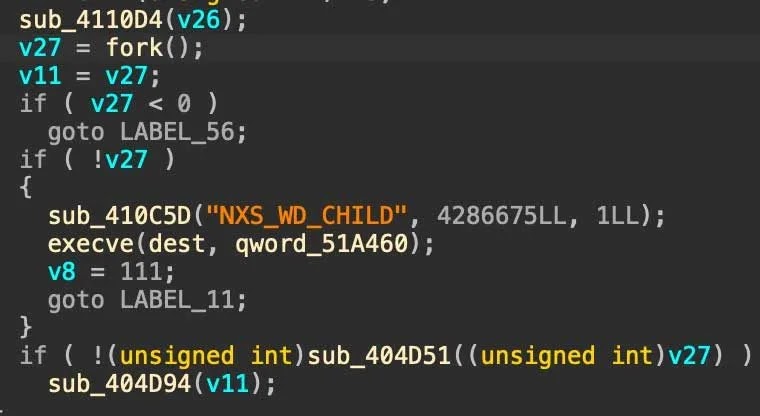
Persistence is built in. Fortinet says Nexcorium uses watchdog functionality to keep the main process alive, restores itself if its binary gets altered or removed, and opens a C2 channel that lets operators issue DDoS commands and push follow-on instructions.
Why Nexcorium matters
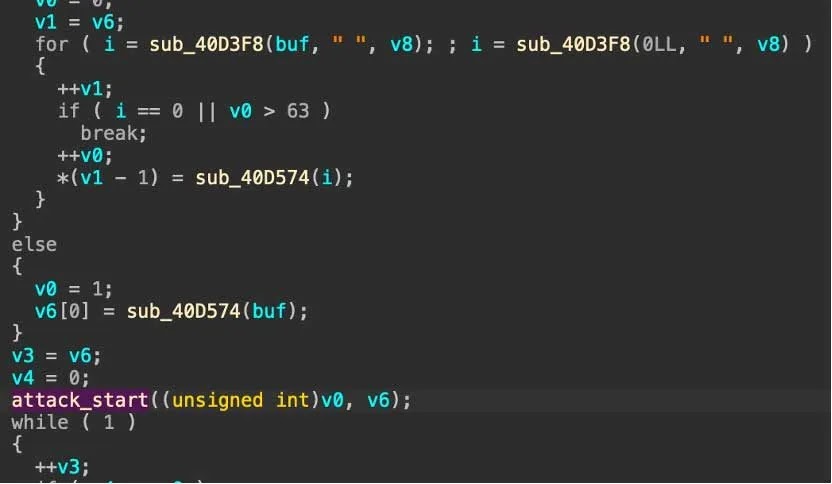
Nexcorium follows the Mirai playbook, but it adds enough operational polish to stay dangerous. Fortinet says it includes an XOR-encoded configuration table, a watchdog module, a DDoS component, and aggressive Telnet brute-force propagation using hardcoded default credentials.
The campaign also does not stop at TBK DVRs. Researchers say operators used CVE-2017-17215 against end-of-life TP-Link routers to widen the infected pool. That gives the botnet a larger, more geographically distributed base of compromised devices for future attacks.
That matters because DVRs and older routers often stay online for years in small businesses, shops, warehouses, and surveillance deployments. They often run with weak passwords, outdated firmware, and little monitoring, which makes them reliable targets for long-lived botnet growth. This point is an inference based on Fortinet’s device focus and the long-standing abuse pattern around Mirai-style IoT malware.
What defenders should watch
| Indicator | Why it matters |
|---|---|
| Exploitation attempts against the TBK DVR vulnerable endpoint | This is the reported initial access path for CVE-2024-3721. |
| Unexpected downloader scripts and architecture-specific ELF binaries | Fortinet says Nexcorium uses a downloader that selects the right payload for each device. |
| Watchdog-like processes that restart the main payload | The malware reportedly uses watchdog logic to survive interruption. |
| Telnet brute-force traffic using default credentials | Fortinet says Nexcorium tries to spread through hardcoded credential lists. |
| Signs of DDoS preparation and unusual outbound C2 activity | Compromised devices become part of a Mirai-style attack network. |
What organizations should do now
- Replace TBK DVR-4104 and DVR-4216 devices if they are still deployed. Fortinet says these models should be retired and it does not point to a vendor patch path for this campaign context.
- Retire TP-Link routers still exposed to CVE-2017-17215 if they are end-of-life and unpatchable.
- Remove direct internet exposure from DVR management interfaces wherever possible.
- Change factory-default credentials and use unique strong passwords on all IoT gear.
- Segment surveillance devices away from critical internal systems to reduce lateral risk.
FAQ
It is a command-injection vulnerability affecting TBK DVR-4104 and DVR-4216 devices. NVD says the flaw enables remote exploitation through crafted requests to a vulnerable endpoint.
Fortinet describes Nexcorium as a Mirai-based malware strain that infects IoT devices and prepares them for DDoS attacks, persistence, brute-force spread, and C2-controlled activity.
Fortinet says the campaign targets TBK DVR-4104 and DVR-4216 devices through CVE-2024-3721 and also expands to end-of-life TP-Link routers through CVE-2017-17215.
For the TBK DVR issue, NVD lists the vulnerability details, but I did not find a clear vendor patch bulletin during this check. Fortinet’s current guidance focuses on replacement, password hygiene, segmentation, and removing exposure.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages