Caller-as-a-Service Turns Scam Calls Into a Structured Fraud Economy

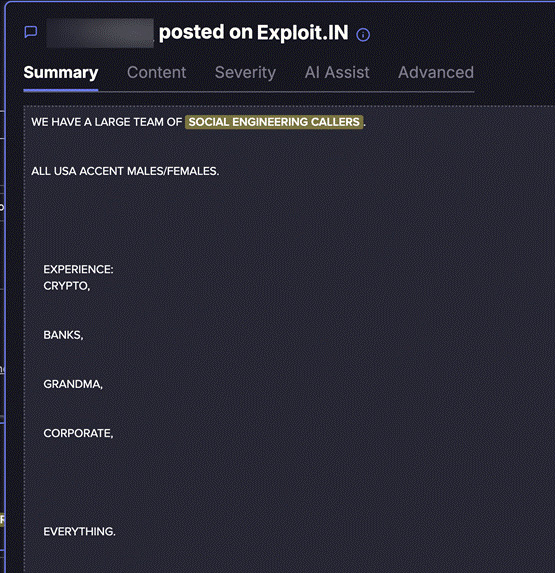
Caller-as-a-Service is becoming a more organized part of cybercrime, with fraud groups recruiting English-speaking callers, assigning roles, supervising live calls, and paying workers through fixed or performance-based models. The model turns phone scams into a service economy where callers do not need to build malware, buy infrastructure, or manage stolen data themselves.
The risk is that scam calls are no longer random one-off attempts. Flare’s research describes underground operations that look closer to structured sales teams, with job posts, screening requirements, live oversight, and compensation plans designed to improve conversion rates.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The wider fraud problem is already large. The FBI said people over 60 reported more than $3.4 billion in losses in 2023, while its 2024 Internet Crime Report said older victims reported nearly $5 billion in losses the following year. The FBI also lists phishing, spoofing, extortion, and personal data breaches among the top cybercrime complaint categories by volume.
What Caller-as-a-Service means
Caller-as-a-Service describes a fraud model where one group handles stolen data, tools, scripts, infrastructure, or monetization, while another person handles the live phone call. The caller’s job is to build trust, create pressure, and persuade the victim to share information, approve a transaction, install software, or move money.
Flare’s analysis says the market now includes separate roles across the scam chain. These include malware developers, phishing kit builders, infrastructure operators, data sellers, victim list traders, and callers who specialize in real-time social engineering.
This division of labor lowers the barrier to entry. A caller does not need advanced technical skills if another actor provides victim lists, leaked credentials, phone numbers, scripts, and follow-up monetization support.
Why the hiring process matters
The recruitment angle is the key point. Underground posts described by Flare resemble job ads, with requirements such as native English ability, fraud experience, operational security awareness, and sometimes live screen sharing during calls.
That live supervision detail matters because it suggests quality control. Operators can monitor the caller, correct mistakes, keep scripts consistent, and prevent the caller from stealing leads or payouts from the wider group.
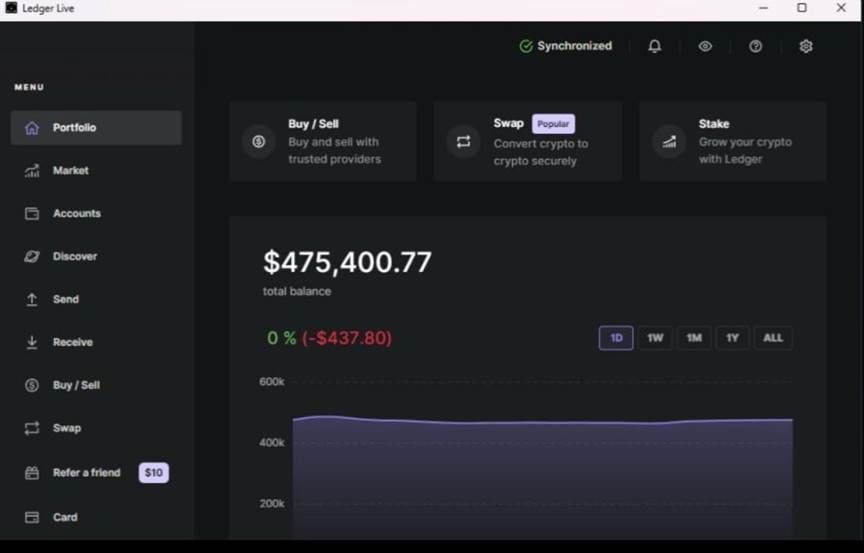
Some posts also use “proof-of-profit” tactics to recruit workers. Flare describes screenshots of large cryptocurrency balances being used to show that the operation can pay, whether the balances are real or staged.
At a glance
| Item | What current reporting shows |
|---|---|
| Model | Caller-as-a-Service |
| Main role | Fraud callers conduct live social engineering |
| Supporting roles | Data sellers, infrastructure operators, malware developers, phishing kit builders |
| Recruitment style | Underground job posts with requirements and screening |
| Common requirement | English fluency and prior fraud experience |
| Operational control | Some callers remain on screen share during live calls |
| Pay models | Fixed pay, commission, or hybrid compensation |
| Main victim risk | Financial theft, credential theft, account takeover |
| Main defender challenge | Calls can look personal because attackers use leaked data |
How scam callers get paid
Flare’s research says these operations use several compensation models. Some callers receive fixed payments, some receive a percentage of extracted funds, and some get a hybrid model that combines both.
One example in the research describes a fixed payment of $1,000 per successful call with an additional percentage. Another example describes a weekly payment model, showing that some operators treat callers more like recurring workers than one-time contractors.
The payment model also shows how fraud chains work. A caller may succeed at convincing a victim, but the money may still require extra steps, such as account takeover, bank transfer abuse, crypto movement, or resale of stolen access.
Why stolen data fuels the call economy
Caller-as-a-Service works better when criminals already know something about the victim. A caller with a name, phone number, email address, employer, bank reference, or exposed credential can sound more credible within seconds.
This is where data breaches and underground markets connect directly to phone fraud. Flare’s report says structured fraud operations rely on leaked credentials and victim lists sourced from underground markets.
The FBI defines vishing as voice-based phishing that happens over phone, voice email, or VoIP calls. That makes Caller-as-a-Service a professionalized version of a known attack pattern, with better targeting and more operational discipline.
Why defenders may care
Organizations often focus on email phishing, endpoint malware, or exposed credentials. Caller-as-a-Service shows why phone-based social engineering deserves equal attention.
A single well-prepared call can bypass technical controls if the caller persuades an employee to approve a login, share a one-time code, install a remote tool, or move funds. This risk increases when the caller already has leaked data from earlier breaches.
The FTC warns consumers not to share personal or financial information with unexpected callers and recommends reporting scam calls with details such as the caller ID number, call-back number, date, and time.
What organizations can do now
- Train employees on live-call scams, not just email phishing.
- Create a no-code-sharing rule for all phone calls.
- Require callback verification through known internal numbers.
- Monitor for unusual password resets, MFA resets, and payment changes.
- Watch dark web and Telegram sources for leaked employee or customer data.
- Add extra verification for finance, IT help desk, and executive assistant workflows.
- Review vendor support procedures so attackers cannot impersonate trusted partners.
What individuals can do now
- Hang up if a caller creates urgency or asks for sensitive details.
- Contact the company, bank, or agency through its official website or app.
- Never share passwords, one-time codes, recovery codes, or full card numbers.
- Do not install remote access tools after an unexpected call.
- Use multi-factor authentication on important accounts.
- Report scam calls to the FTC or FBI IC3 when money, credentials, or identity data are involved.
FAQ
Caller-as-a-Service is a fraud model where criminals recruit or pay callers to conduct live phone scams while other actors provide stolen data, scripts, infrastructure, or monetization support.
It is closely related. Vishing means voice-based phishing over phone, voicemail, or VoIP. Caller-as-a-Service describes a more organized business model behind some of those calls.
Flare’s research says some underground job posts request native English speakers, which suggests operators are targeting English-speaking regions and want callers who sound natural to victims.
Real-time screen sharing lets operators supervise calls, enforce scripts, improve performance, and reduce internal fraud. It also makes the operation look more like a managed call center.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages