UK Warns Chinese Hackers Are Using Hijacked Routers and IoT Devices as Proxy Networks

The UK’s National Cyber Security Centre and international partners have warned that China-linked hackers are increasingly routing attacks through large covert networks of compromised routers, cameras, NAS devices, and other internet-connected equipment. The goal is simple: hide the real source of malicious activity and make intrusions harder to trace.
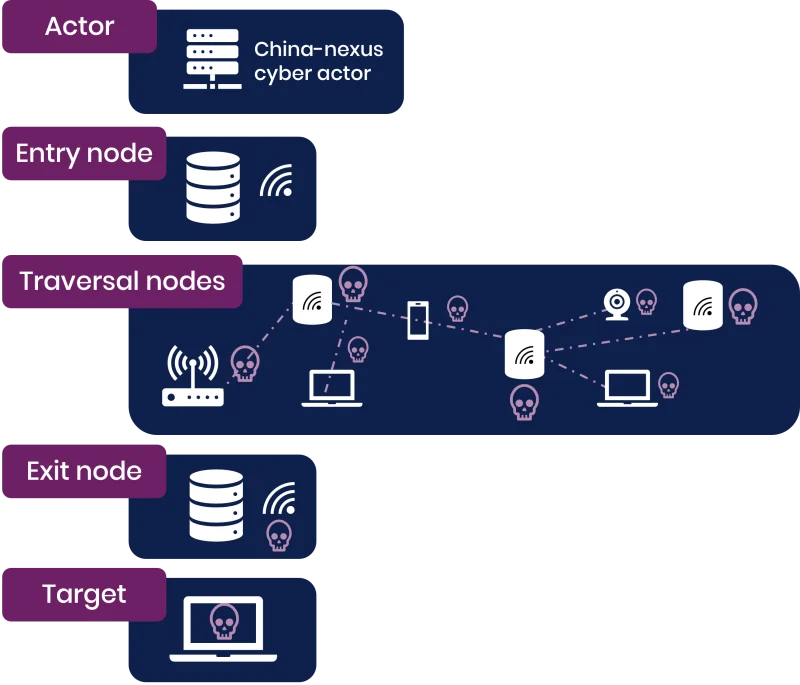
The advisory says China-nexus actors have shifted away from individually rented or purchased infrastructure and now rely on externally provisioned botnets made from hacked consumer and small business devices. These networks can route traffic through several compromised nodes before it reaches a target, making the activity look like it came from a nearby or ordinary internet connection.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The warning was backed by agencies from the UK, United States, Australia, Canada, Germany, Japan, the Netherlands, New Zealand, Spain, and Sweden. Reuters reported that 15 cybersecurity partners from eight countries joined the coordinated alert, with the NCSC leading the public warning.
Why the proxy networks matter
The NCSC says most China-nexus threat actors now use these covert networks. It also says multiple covert networks have been created, are constantly updated, and may be shared by more than one actor.
The devices inside these networks are mainly small office and home office routers, IoT devices, and smart devices. That can include routers, internet cameras, video recorders, and network-attached storage devices.
This gives attackers a cheap and resilient way to hide. Instead of connecting from an obvious foreign server, they can move through compromised devices that belong to homes, small businesses, or unmanaged branch offices.
How the attacks avoid detection
A covert network works like a layered relay system. The attacker enters the network through one compromised device, routes traffic through other devices, and exits close to the target network.
That makes traditional IP blocking weaker. A defender may see traffic from a local broadband provider or a normal residential IP address, not a known attacker server.
The joint advisory warns that static lists of bad IP addresses no longer work well against this model because the botnets keep changing. New compromised devices join, old devices disappear, and attackers can rotate infrastructure quickly.
At a glance
| Item | Details |
|---|---|
| Main warning | China-linked actors use covert proxy networks at scale |
| Lead agency | UK National Cyber Security Centre |
| Co-signing partners | Agencies from the U.S., Australia, Canada, Germany, Japan, the Netherlands, New Zealand, Spain, and Sweden |
| Main devices abused | SOHO routers, IoT devices, cameras, NVRs, NAS devices |
| Main purpose | Hide attack origin and evade detection |
| Common use | Espionage, pre-positioning, data theft, and operational cover |
| Known examples | Raptor Train and KV-Botnet |
| Groups linked in reporting | Flax Typhoon and Volt Typhoon |
| Main defender concern | Static IP blocking becomes less effective |
| Main user concern | Old or exposed devices can become part of state-linked infrastructure |
Raptor Train shows the scale of the problem
Raptor Train is one of the clearest examples. A 2024 joint advisory said the botnet consisted of more than 260,000 compromised devices as of June 2024, spread across North America, South America, Europe, Africa, Southeast Asia, and Australia.
The FBI linked the botnet to malicious activity by the China-linked Flax Typhoon group and the Chinese company Integrity Technology Group. The U.S. Justice Department said a court-authorized operation disrupted the botnet in September 2024.
The targets tied to Raptor Train activity included military, government, higher education, telecommunications, defense industrial base, and IT sectors, mainly in the United States and Taiwan, according to earlier reporting and government advisories.
KV-Botnet shows why takedowns do not end the threat
A separate network known as KV-Botnet was linked to Volt Typhoon, another Chinese state-backed group. The U.S. Justice Department said a court-authorized operation disrupted hundreds of U.S.-based SOHO routers that had been hijacked by PRC state-sponsored hackers.
The botnet mainly abused vulnerable routers that were out of date or no longer receiving patches. Those devices gave attackers a way to conceal traffic while targeting critical infrastructure.
Later reporting from Lumen’s Black Lotus Labs and BleepingComputer said Volt Typhoon activity began rebuilding after the FBI disruption, showing how these networks can return when vulnerable devices remain exposed.
Why this affects more than governments
The advisory focuses on China-linked cyber activity, but the device problem affects everyone. A home router, small office firewall, smart camera, or NAS box can become part of a covert network without the owner noticing.
The device owner may not be the final target. Attackers may use the compromised device only as a relay to reach a government agency, defense contractor, telecom provider, university, or critical infrastructure operator.
This creates a shared security problem. Weak edge devices help attackers hide from the real victims, while the owners of those devices may never see obvious signs of compromise.
What organizations should do now
- Map all edge devices, including routers, VPNs, firewalls, remote access systems, cameras, and NAS devices.
- Baseline normal traffic from edge devices and investigate unusual outbound connections.
- Use multifactor authentication for remote access and administrator accounts.
- Apply dynamic threat feeds that include covert network indicators, not only static IP blocklists.
- Use IP allowlists where business operations allow them.
- Apply zero-trust controls for remote access and sensitive systems.
- Use machine certificate verification where possible.
- Replace end-of-life devices that no longer receive security updates.
- Disable remote management interfaces that do not need internet exposure.
- Review logs for repeated failed logins, strange admin sessions, or unexpected configuration changes.
What home users and small businesses should do
- Replace routers and cameras that no longer receive firmware updates.
- Change default admin passwords on routers, cameras, NAS devices, and DVRs.
- Turn off remote administration unless you actively need it.
- Install firmware updates from the vendor’s official support page.
- Reboot devices after checking settings, but do not treat rebooting as a full fix.
- Remove unused port forwarding rules.
- Use a separate guest network for smart devices where possible.
- Check the router’s admin page for unknown DNS settings or unknown users.
Why IP blocking alone is no longer enough
Security teams often block known malicious IPs, but covert networks make that approach weaker. A malicious connection may come from a device that looked clean yesterday or from a residential IP range that changes often.
The NCSC advisory recommends stronger monitoring around edge devices and remote access connections. It also recommends combining threat feeds with baseline traffic analysis so defenders can spot behavior that does not match normal patterns.
For high-risk organizations, the focus should shift from “Is this IP on a blocklist?” to “Does this connection make sense for this user, device, location, certificate, and access pattern?”
FAQ
The UK NCSC and international partners warned that China-linked hackers are using large covert networks of compromised routers, IoT devices, and smart devices to hide cyber operations.
The advisory says these networks mainly use compromised SOHO routers, IoT devices, and smart devices. Reporting also mentions cameras, video recorders, and NAS equipment.
Proxy networks help attackers disguise their location, evade geographic blocking, rotate infrastructure, and make malicious traffic look like it came from ordinary internet users.
Raptor Train was a large botnet linked to Flax Typhoon and Integrity Technology Group. A 2024 advisory said it contained more than 260,000 compromised devices as of June 2024.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages