Over 10,000 Zimbra Servers Remain Exposed to Ongoing XSS Attacks

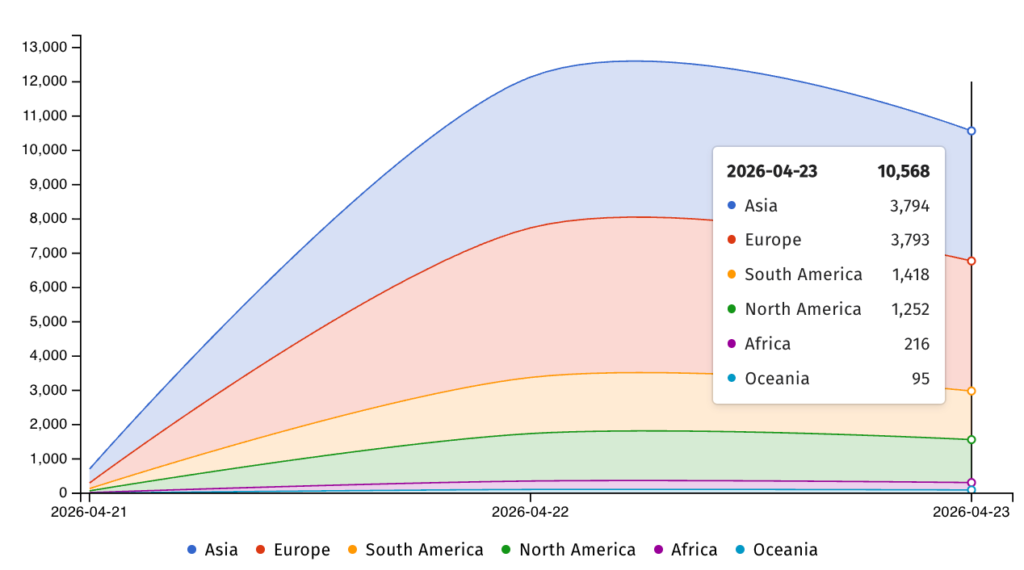
More than 10,000 internet-exposed Zimbra Collaboration Suite servers remain vulnerable to an actively exploited cross-site scripting flaw, according to Shadowserver. The vulnerability, tracked as CVE-2025-48700, affects Zimbra’s Classic UI and can let attackers run malicious JavaScript inside a user’s webmail session.
CISA added the flaw to its Known Exploited Vulnerabilities catalog on April 20, 2026, after confirming evidence of active exploitation. Federal Civilian Executive Branch agencies had until April 23 to secure affected Zimbra systems, which gave agencies only three days to act.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The main concern is that the attack can happen through a crafted email viewed in the Zimbra Classic UI. Zimbra’s advisory history describes the issue as a Classic UI XSS flaw tied to HTML content sanitization, including crafted structures and CSS @import injection vectors.
What CVE-2025-48700 does
CVE-2025-48700 affects Zimbra Collaboration Suite versions 8.8.15, 9.0, 10.0, and 10.1. NVD describes it as a cross-site scripting vulnerability that allows attackers to execute arbitrary JavaScript within the user’s session.
That can expose sensitive information because the malicious script runs in the context of the victim’s active Zimbra webmail session. Depending on session state and permissions, this can support email theft, session abuse, phishing from trusted accounts, or further targeting inside an organization.
The flaw stems from insufficient sanitization of HTML content. In practical terms, an attacker can craft email content that the Classic UI fails to clean properly before rendering it to the user.
At a glance
| Item | Details |
|---|---|
| Vulnerability | CVE-2025-48700 |
| Product | Zimbra Collaboration Suite |
| Affected versions | 8.8.15, 9.0, 10.0, 10.1 |
| Vulnerable component | Zimbra Classic UI |
| Vulnerability type | Cross-site scripting |
| Main trigger | Crafted HTML email viewed in Classic UI |
| User interaction | No link click or attachment needed in reported attack flow |
| Exploitation status | Actively exploited |
| CISA KEV date | April 20, 2026 |
| Federal deadline | April 23, 2026 |
| Exposed vulnerable servers | More than 10,000 |
| Main risk | Sensitive data exposure and session abuse |
Why the Zimbra flaw is urgent
Zimbra servers often sit at the center of an organization’s communications. A successful compromise can give attackers access to email, internal contacts, attachments, authentication messages, and sensitive business discussions.
This makes even an XSS flaw dangerous. Attackers do not always need server-level remote code execution to cause damage. If they can run script code inside a trusted mailbox session, they may steal session data, read messages, redirect users, or stage follow-on phishing.
Shadowserver said it is scanning and reporting Zimbra instances vulnerable to CVE-2025-48700 daily. BleepingComputer reported that more than 10,500 exposed servers remained unpatched, with the largest concentrations in Asia and Europe.
Why Classic UI is the key risk area
The vulnerability affects the Zimbra Classic UI, not every possible way of accessing Zimbra mail. The risky path involves malicious HTML content being rendered in a way that allows JavaScript execution inside the user’s browser session.
This matters because many organizations continue using Classic UI for compatibility, habit, or user preference. Attackers know this and can target webmail users with crafted messages designed for that interface.
Administrators should not assume a system is safe just because users do not download attachments or click links. The attack path described in current reporting centers on viewing a malicious email in the vulnerable interface.
Previous Zimbra attacks show the pattern
Zimbra flaws have repeatedly attracted state-backed and criminal attackers because email systems provide valuable intelligence and credentials. In recent years, Zimbra vulnerabilities have appeared in campaigns linked to Russian espionage groups and other advanced actors.
Seqrite Labs previously described Operation GhostMail, a phishing campaign tied to APT28 that exploited a different Zimbra XSS flaw, CVE-2025-66376, against Ukrainian government targets. That campaign used malicious email content without attachments, links, or macros, relying instead on JavaScript embedded in the HTML body.
BleepingComputer also notes that other Russian-linked groups, including Winter Vivern and APT29, have targeted vulnerable Zimbra servers in earlier campaigns. The repeated targeting shows why exposed and unpatched webmail systems remain high-value assets.
What administrators should do now
- Update Zimbra Collaboration Suite to a patched version immediately.
- Confirm whether users still access the Zimbra Classic UI.
- Review CISA KEV guidance for CVE-2025-48700.
- Check mail logs and web logs for suspicious crafted email activity.
- Search for unusual mailbox access, forwarding rules, or session activity.
- Review administrator accounts and delegated mailbox permissions.
- Monitor for suspicious outbound emails from trusted internal accounts.
- Apply extra scrutiny to government, telecom, education, defense, and critical infrastructure environments.
- Consider disabling Classic UI exposure if the organization can operate without it.
- Ask Shadowserver or national CERT channels about vulnerability reports tied to your IP ranges.
Why patching is not enough after exposure
Patching closes the vulnerable path, but it does not answer whether attackers already used the flaw. Organizations that had internet-exposed Zimbra servers before patching should review signs of compromise.
Security teams should check for unusual webmail sessions, mailbox searches, suspicious message forwarding, new filters, and unexpected login locations. They should also review whether attackers used compromised mailboxes to send phishing messages to internal or external contacts.
Email compromise can persist quietly. Even after the webmail flaw is fixed, stolen session data, copied messages, or attacker-created forwarding rules can continue to create risk.
What users should watch for
Users should treat unusual emails inside Zimbra with caution, especially messages that appear blank, oddly formatted, or unexpected. They should report suspicious emails instead of forwarding them widely.
They should also report sudden login prompts, unexpected mailbox changes, missing messages, or unusual sent items. These signs can indicate mailbox misuse or session theft.
Organizations should remind users that a message does not need an attachment to be dangerous. In this case, the risk comes from how vulnerable Zimbra Classic UI versions render malicious HTML email content.
FAQ
CVE-2025-48700 is a cross-site scripting vulnerability in Zimbra Collaboration Suite’s Classic UI. It can allow attackers to execute JavaScript inside a user’s webmail session.
The vulnerability affects Zimbra Collaboration Suite 8.8.15, 9.0, 10.0, and 10.1.
Yes. CISA added the flaw to its Known Exploited Vulnerabilities catalog after evidence of active exploitation.
Shadowserver is reporting vulnerable instances daily, and current reporting says more than 10,000 internet-exposed Zimbra servers remain unpatched.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages