Microsoft Teams Phishing Campaign Deploys New “Snow” Malware Suite

A newly tracked threat group called UNC6692 is using Microsoft Teams chats to trick employees into installing a custom malware suite named Snow. The campaign starts with email bombing, then moves into Teams, where the attacker pretends to be an IT helpdesk worker offering to fix the spam problem.
Google’s Mandiant researchers say the attack does not rely on a software vulnerability. It relies on trust. The victim accepts a Teams message from an external account, clicks a link for a fake “patch,” and downloads files that start the infection chain.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The Snow toolkit includes three main components: SnowBelt, SnowGlaze, and SnowBasin. Together, they give attackers persistence, command execution, tunneling, screenshot capture, file handling, and a path toward deeper network compromise.
How the Microsoft Teams attack starts
UNC6692 first floods the target’s inbox with a large volume of unwanted emails. This creates pressure and makes the victim more likely to accept help from someone claiming to be IT support.
The attacker then sends a Microsoft Teams message and tells the target to install a local patch that will stop the spam. Mandiant says the phishing page used in the campaign was presented as a “Mailbox Repair and Sync Utility.”
When the victim clicks the link, the page downloads a renamed AutoHotkey binary and an AutoHotkey script from an attacker-controlled AWS S3 bucket. The script then helps install SnowBelt, a malicious Chromium-based browser extension, inside a headless Microsoft Edge session.
What the Snow malware components do
SnowBelt works as the first major persistence and relay component. It runs as a malicious browser extension and helps the attacker retrieve additional files for the next stages of the compromise.
SnowGlaze acts as the tunneling tool. It creates a WebSocket tunnel between the infected system and attacker infrastructure, and it can support SOCKS proxy activity for routing traffic through the compromised host.
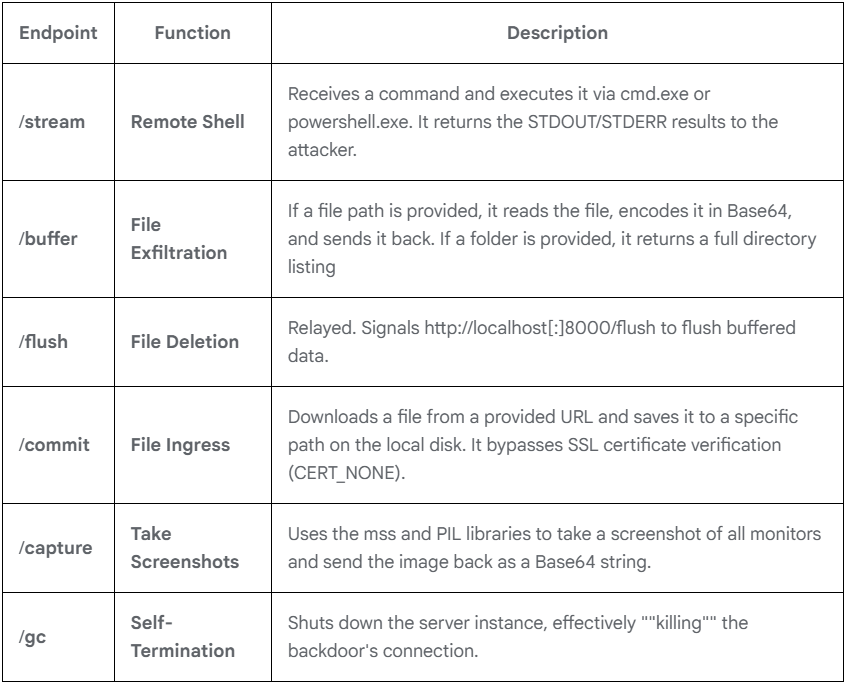
SnowBasin is the Python-based backdoor. It runs a local HTTP server and can execute CMD or PowerShell commands, capture screenshots, download files, manage files, exfiltrate data, and shut itself down when ordered by the attacker.
At a glance
| Item | What the current reporting shows |
|---|---|
| Threat group | UNC6692 |
| Main delivery channel | Microsoft Teams |
| First pressure tactic | Email bombing |
| Impersonation theme | IT helpdesk support |
| Fake lure | Patch to stop email spam |
| Initial payload | AutoHotkey binary and script |
| Malware suite | Snow |
| Main components | SnowBelt, SnowGlaze, SnowBasin |
| Browser abused | Microsoft Edge in headless mode |
| Main goals | Credential theft, lateral movement, data theft, domain compromise |
| Reported infrastructure abuse | AWS S3 for payload hosting and data handling |
The attack can lead to domain-level compromise
After the first system is compromised, UNC6692 moves beyond simple malware deployment. Mandiant says the attackers performed internal reconnaissance and scanned for services such as SMB and RDP to find more systems inside the network.
Source: Google
The attackers also dumped LSASS memory to extract credential material. They then used pass-the-hash techniques to authenticate to additional hosts and continue moving through the environment.
At a later stage, the threat actor reached domain controllers and used FTK Imager to extract the Active Directory database along with SYSTEM, SAM, and SECURITY registry hives. Those files can expose sensitive credential data across the domain if attackers successfully exfiltrate them.
Why Teams makes the lure more convincing
Microsoft Teams gives attackers a different kind of credibility. Many employees treat Teams messages as internal, urgent, and safer than email, especially when the message appears during a stressful inbox flooding event.
This matters because many organizations train users to be cautious with email links, but they may not apply the same caution to chat messages. A fake helpdesk conversation inside Teams can feel like normal workplace support.
The campaign also shows how attackers can blend familiar tools with custom malware. Email bombing creates the problem, Teams delivers the fake solution, and the Snow toolkit gives the attacker a foothold for deeper compromise.
What defenders should watch for
Security teams should focus on both user behavior and endpoint signals. The first warning may not come from malware detection. It may come from a user reporting a sudden flood of emails followed by an unexpected Teams support message.
Defenders should also review Microsoft Teams external access settings. Attackers can abuse cross-tenant communication when organizations allow external users to message employees without enough friction or review.
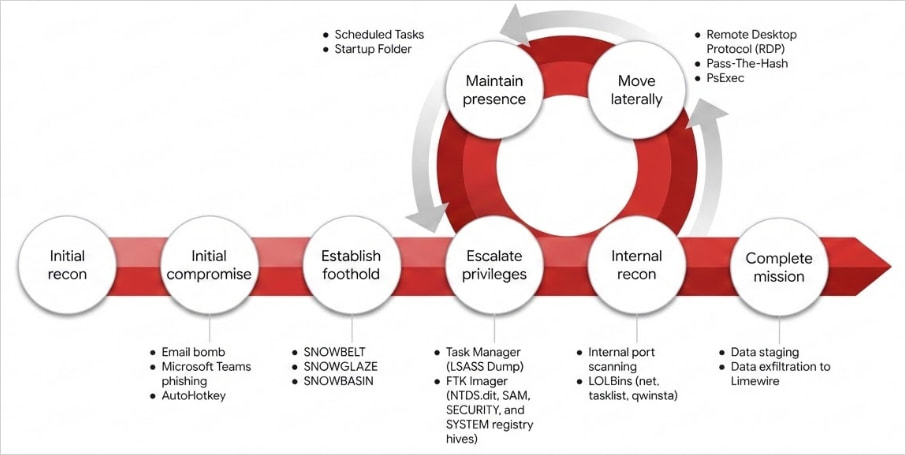
Source: Google
Endpoint teams should look for suspicious AutoHotkey execution, headless Microsoft Edge activity, unexpected browser extension loading, new scheduled tasks, and strange local HTTP server behavior tied to Python processes.
Practical steps for organizations
- Restrict external Microsoft Teams communication where possible.
- Require users to verify IT support requests through a known internal channel.
- Train employees to report email bombing and unexpected Teams helpdesk messages together.
- Alert on AutoHotkey execution from unusual download locations.
- Monitor Microsoft Edge launches using headless mode and extension-loading flags.
- Review scheduled tasks and startup folder shortcuts created after suspicious Teams activity.
- Watch for unexpected WebSocket tunnels and SOCKS proxy behavior.
- Detect LSASS dumping attempts and pass-the-hash activity.
- Monitor access to domain controllers after unusual endpoint activity.
- Use Mandiant’s published indicators and YARA rules to hunt for Snow components.
FAQ
UNC6692 is a threat group tracked by Google’s Mandiant researchers. It has been linked to a social engineering campaign that uses email bombing and Microsoft Teams impersonation to deploy the Snow malware suite.
Snow is a custom malware suite made up of several components, including SnowBelt, SnowGlaze, and SnowBasin. These tools support persistence, tunneling, command execution, file handling, data theft, and lateral movement.
The attacker floods the victim’s inbox, then contacts them through Microsoft Teams while pretending to be IT support. The victim receives a link to a fake patch, which downloads the files used to start the Snow infection chain.
The public reporting describes social engineering and abuse of legitimate collaboration features, not a Teams zero-day. The attacker convinces the victim to trust the chat and install the fake patch.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages