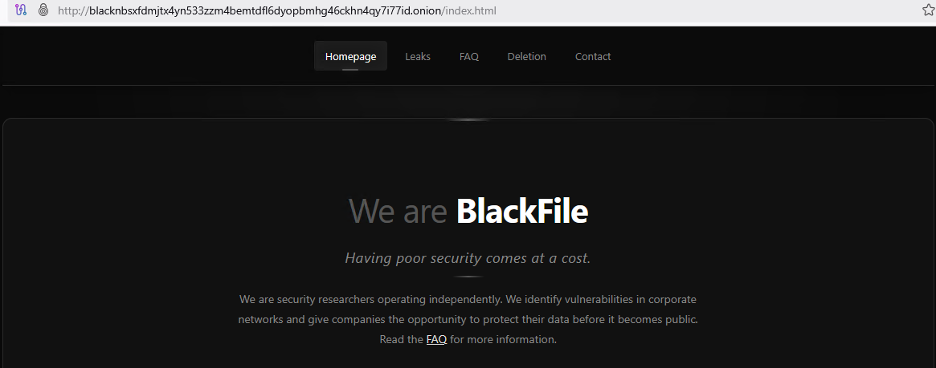
New BlackFile Extortion Group Uses Vishing Calls to Target Retail and Hospitality Firms

A new extortion group known as BlackFile is using phone calls, fake IT support messages, and stolen login codes to break into corporate systems. The group has been linked to a wave of data theft and extortion attacks affecting retail and hospitality organizations since February 2026.
BlackFile is also tracked as CL-CRI-1116, UNC6671, and Cordial Spider. Researchers say the group focuses on social engineering instead of custom malware, which makes the attacks harder to detect with traditional endpoint tools.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign shows how extortion groups are moving beyond email phishing. Instead of sending a malicious attachment, the attackers call employees, pretend to work for the company’s IT helpdesk, and direct them to fake login pages that collect credentials and one-time passcodes.
BlackFile relies on trust, not malware
The BlackFile intrusion chain starts with vishing, or voice phishing. Attackers use spoofed VoIP numbers or fake caller ID names to make the call look like it came from a trusted internal source.
Once the employee follows the instructions, the fake login page captures the username, password, and MFA code. The attackers then use that short window to access the victim’s single sign-on environment.
After logging in, BlackFile operators can register their own devices with the company’s multifactor authentication system. That gives them a more durable way back into the environment without needing to trick the same employee again.
What the attackers do after getting access
BlackFile operators look for higher-value accounts after the first compromise. Researchers say the group scrapes internal employee directories and moves toward executive-level access when possible.
The group then targets cloud data stored in platforms such as Salesforce and SharePoint. Instead of deploying obvious malware, the attackers abuse standard API functions and normal download features to move data out of the company.
The stolen files may include employee phone lists, confidential business reports, and documents containing sensitive terms such as “confidential” or “SSN.” The use of normal cloud functions helps the activity blend into legitimate SSO-authenticated sessions.
At a glance
| Item | What the current reporting shows |
|---|---|
| Group name | BlackFile |
| Other names | CL-CRI-1116, UNC6671, Cordial Spider |
| Main tactic | Vishing, or voice phishing |
| First reported activity window | January to February 2026 |
| Main targets | Retail and hospitality, with activity across multiple industries |
| Primary goal | Data theft and extortion |
| Common entry point | Fake IT helpdesk calls |
| Cloud platforms targeted | Salesforce and SharePoint |
| Notable behavior | Device registration to bypass MFA prompts |
| Reported ransom range | Seven-figure demands |
The extortion pressure goes beyond leaked files
After stealing data, BlackFile uses a leak site to pressure victims. The group may contact companies through compromised employee email accounts or randomly created Gmail addresses.
The pressure can also move offline. Reports say employees at compromised companies, including senior executives, have faced swatting attempts. Swatting involves making false emergency calls to send police or emergency responders to a victim’s location.
That tactic turns a corporate breach into a personal safety issue. It also matches a broader pattern in some extortion communities, where attackers combine data theft, harassment, and public shaming to force payment.
Why this matters for retailers and hotels
Retail and hospitality companies often have large frontline workforces, distributed locations, seasonal staff, and heavy use of cloud systems. Those conditions give vishing groups more opportunities to impersonate IT support.
The attack also bypasses many controls that companies built for email phishing. A secure email gateway cannot block a phone call. Link scanning tools will not help if an employee types a fake login address after speaking to someone they believe works for IT.
BlackFile’s approach also shows why MFA alone no longer stops every identity attack. MFA still matters, but attackers now focus on stealing live passcodes, enrolling their own devices, or abusing helpdesk workflows.
How organizations can reduce the risk
Security teams should treat helpdesk verification as a frontline control. Employees need a safe way to verify IT calls before they share information, open remote access tools, or visit login pages.
RH-ISAC recommends stronger call-handling policies, multifactor identity checks for callers, and simulation-based social engineering training for frontline staff.
Companies should also monitor for new device registrations, unusual Salesforce API usage, large SharePoint downloads, and suspicious searches for sensitive file names. These signals may reveal activity that looks normal at the tool level but abnormal for the employee account.
What security teams can do now
- Require employees to end unexpected IT calls and call back through an approved internal number.
- Block new MFA device registration without stronger identity checks.
- Alert on unusual SSO logins, especially after helpdesk contact.
- Review Salesforce and SharePoint API activity for high-volume exports.
- Monitor searches for sensitive terms such as “SSN,” “confidential,” and “payroll.”
- Train frontline staff with realistic vishing simulations.
- Limit executive directory exposure inside internal systems.
- Review Gmail or external email contact during extortion response.
FAQ
BlackFile is a financially motivated extortion group linked to data theft attacks that use vishing, stolen credentials, and cloud data exfiltration. It is also tracked as CL-CRI-1116, UNC6671, and Cordial Spider.
Vishing means voice phishing. Attackers call victims by phone, pretend to be someone trustworthy, and push them to reveal credentials, MFA codes, or other sensitive information.
These sectors often have many employees, large customer-facing teams, and complex cloud environments. That makes social engineering easier and gives attackers more accounts to target.
Current reporting focuses on data theft and extortion, not file encryption. The group steals sensitive files and uses leak threats, ransom emails, and victim pressure tactics to demand payment.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages