TCLBANKER Malware Hijacks WhatsApp and Outlook to Spread Banking Trojan
TCLBANKER is a new Brazilian banking trojan that steals financial data and spreads through victims’ own WhatsApp and Microsoft Outlook accounts. Elastic Security Labs tracks the campaign as REF3076 and says the malware appears to be a major update of the Maverick and SORVEPOTEL malware families.
The campaign stands out because it does not rely only on fake banking pages or simple phishing emails. It abuses a signed Logitech application, uses DLL side-loading, checks whether the victim appears to be in Brazil, and then spreads through trusted contacts.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Once TCLBANKER infects a Windows system, it watches for visits to targeted banking, fintech, and cryptocurrency websites. When the victim opens a monitored site, the malware can connect to its command-and-control server and display fake full-screen overlays designed to steal passwords, security codes, and other sensitive information.
How the TCLBANKER attack starts
The infection begins with a malicious ZIP file that contains an MSI installer. Elastic says the installer abuses a signed Logitech program called Logi AI Prompt Builder.
The malware uses DLL side-loading against the legitimate Logitech application. It places a malicious DLL named screen_retriever_plugin.dll where the trusted application loads it automatically.
This technique helps the malware blend into normal software behavior. To a user, the file may look like a regular installer. In the background, the malicious DLL starts the next stage of the attack.
At a glance
| Item | Details |
|---|---|
| Malware name | TCLBANKER |
| Campaign tracking name | REF3076 |
| Main target region | Brazil |
| Targeted services | Banking, fintech, and cryptocurrency platforms |
| Initial delivery | Malicious ZIP file with MSI installer |
| Abused application | Logi AI Prompt Builder |
| Propagation methods | WhatsApp Web hijacking and Outlook email automation |
Why the Logitech abuse matters
Attackers often abuse trusted software because security tools and users may treat signed applications as safer. TCLBANKER uses that trust to load its own malicious component through DLL side-loading.
The loader only runs when it detects expected process names, including logiaipromptbuilder.exe. It refuses to run when loaded by common analysis processes that researchers use to inspect malware.
Elastic says the loader also includes anti-debugging checks, anti-analysis checks, language checks, string encryption, ETW tampering, and a watchdog system. These features make the malware harder to inspect in sandboxes and lab environments.
TCLBANKER checks for Brazilian victims
TCLBANKER does not fully activate on every infected machine. It checks the region, language, keyboard layout, and time zone to decide whether the system looks like a real Brazilian target.
If the environment does not match the expected profile, the malware may fail to decrypt its embedded payload. This helps it avoid automated malware analysis systems and security researchers outside its target region.
This type of environment-gated behavior also reduces noise for attackers. They can focus the banking trojan on users who are more likely to visit the financial platforms targeted by the campaign.
What the banking trojan does
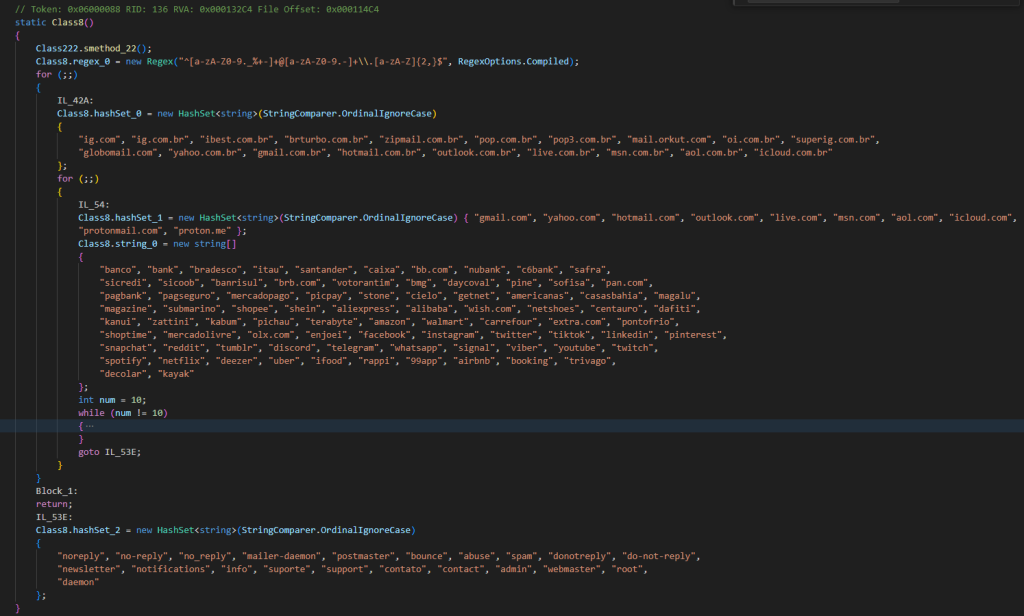
The main banking module monitors the browser address bar using Windows UI Automation. Elastic says it targets 59 Brazilian banking, fintech, and cryptocurrency domains.
When the malware detects a targeted website, it opens a WebSocket connection to its command-and-control server. From there, operators can issue commands and guide the fraud attempt in real time.
The malware can capture screenshots, start or stop screen streaming, manipulate the clipboard, control the mouse and keyboard, manage files and processes, enumerate windows, and display fake credential prompts.
Fake full-screen overlays steal credentials
TCLBANKER uses Windows Presentation Foundation to create full-screen overlays. These screens can look like banking prompts, verification screens, vishing wait pages, or fake Windows Update screens.
The overlays can block normal desktop interaction and hide themselves from screen capture tools. This helps attackers control what the victim sees while reducing the chance that the fraud gets recorded.
The goal is simple. The victim sees a trusted-looking prompt and enters credentials, banking codes, or verification details directly into an attacker-controlled screen.
How the WhatsApp worm spreads
The WhatsApp module looks for authenticated WhatsApp Web sessions inside browsers. Instead of asking the victim to scan a new QR code, the malware tries to reuse the existing browser session.
After hijacking the session, the malware can send phishing messages to the victim’s contacts. Those messages carry the attacker’s lure and can point new users to the same trojanized installer.
This makes the campaign more convincing. A message that comes from a real friend, colleague, or family member can look much safer than a random phishing message from an unknown number.
How the Outlook module spreads
The Outlook module abuses Microsoft Outlook through COM automation. It can open Outlook in the background and send phishing emails from the infected user’s account.
Elastic says the malware can use the victim’s contact list and inbox to find more recipients. This gives attackers a way to spread through real business and personal relationships.
This approach can bypass some reputation-based defenses because the message comes from a legitimate email account. The sender may also have an existing relationship with the recipient.
Why defenders should take this seriously
- TCLBANKER combines credential theft with self-propagation.
- It abuses a legitimate signed application to start the infection chain.
- It targets 59 banking, fintech, and cryptocurrency domains.
- It uses Brazilian language and region checks to avoid analysis.
- It hijacks WhatsApp Web sessions to reach trusted contacts.
- It abuses Outlook to send phishing emails from real accounts.
- It uses full-screen overlays to pressure users into entering credentials.
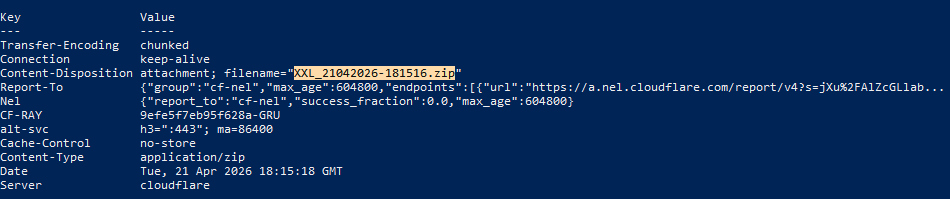
Cloudflare Workers infrastructure appears in the campaign
Elastic says the campaign uses Cloudflare Workers for command-and-control and distribution infrastructure under a single account. The researchers also found developer artifacts, test process names, debug paths, and an incomplete phishing page.
Those details suggest REF3076 may still be in an early operational stage. The campaign already has advanced propagation and evasion features, but the infrastructure and tooling may continue to change.
Security teams should expect the operators to refine the malware, update lures, rotate infrastructure, and improve automation if the campaign continues.
What organizations should monitor
| Area | What to look for |
|---|---|
| Endpoint behavior | Unexpected Logi AI Prompt Builder activity or suspicious child processes |
| DLL loading | Unknown screen_retriever_plugin.dll files in Logitech-related folders |
| WhatsApp Web | Unusual browser automation or unexpected messages sent to contacts |
| Outlook | Bulk outgoing email activity or COM automation from suspicious processes |
| Network traffic | Connections to suspicious Cloudflare Workers domains or known REF3076 infrastructure |
| User interface | Unexpected full-screen overlays, fake update screens, or blocked desktop controls |
Recommended actions
- Warn users not to open unexpected ZIP files or installers received through WhatsApp or email.
- Block known TCLBANKER indicators of compromise at endpoint and network layers.
- Review systems that recently ran Logi AI Prompt Builder from unusual directories.
- Monitor for suspicious DLL side-loading patterns involving screen_retriever_plugin.dll.
- Investigate sudden spikes in outbound Outlook messages.
- Review WhatsApp Web sessions on machines that may have opened suspicious files.
- Use endpoint detection rules that flag full-screen fraud overlays and suspicious browser automation.
- Reset passwords and revoke sessions for accounts used on infected machines.
Summary
- TCLBANKER is a Brazilian banking trojan tracked by Elastic as REF3076.
- The malware abuses a signed Logitech application and DLL side-loading to start the infection chain.
- It targets 59 banking, fintech, and cryptocurrency domains.
- It spreads through hijacked WhatsApp Web sessions and Outlook accounts.
- Organizations should monitor endpoint behavior, outgoing messages, suspicious DLLs, and known campaign infrastructure.
FAQ
TCLBANKER is a Brazilian banking trojan that steals financial data and spreads through WhatsApp Web and Microsoft Outlook accounts.
Elastic Security Labs published the detailed research and tracks the campaign as REF3076.
The campaign uses a malicious ZIP file with an MSI installer that abuses a signed Logitech application called Logi AI Prompt Builder.
Elastic says the malware targets 59 Brazilian banking, fintech, and cryptocurrency domains.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages