ODINI Research Shows Faraday Cages Cannot Fully Stop Air-Gap Data Leaks
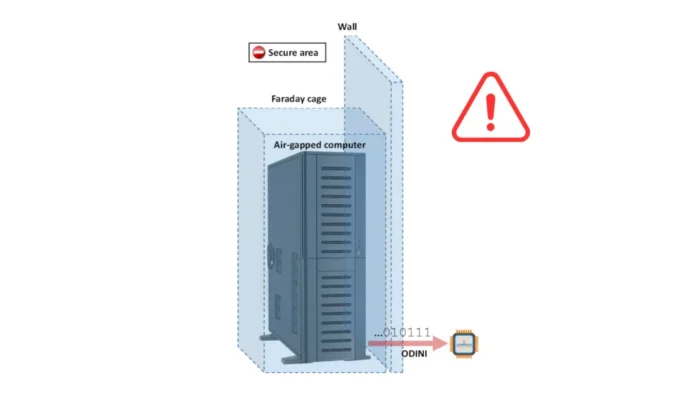
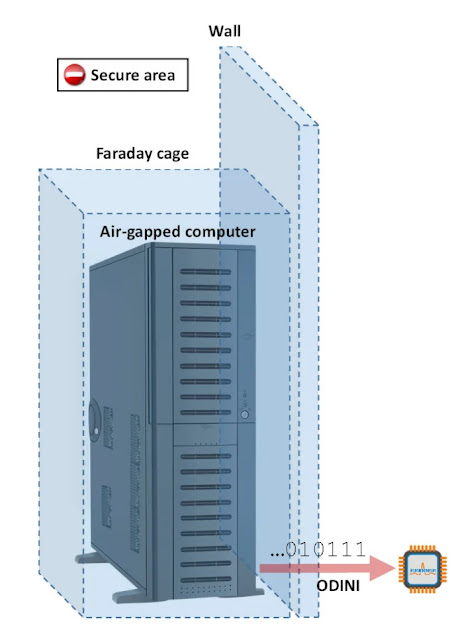
ODINI is a proof-of-concept malware technique that can leak data from air-gapped computers by controlling magnetic fields generated by the CPU. The research shows that even systems protected by Faraday shielding can still expose small amounts of sensitive data under specific conditions.
The work comes from researchers Mordechai Guri, Boris Zadov, Andrey Daidakulov, and Yuval Elovici. Their paper was first published in 2018, but it remains relevant because it highlights a physical exfiltration path that standard network defenses cannot detect.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
ODINI does not let attackers remotely break into an isolated computer by itself. The attacker must first infect the air-gapped machine, usually through a supply chain compromise, removable media, insider access, or another physical route. The technique focuses on getting data out after that initial compromise.
How ODINI leaks data through magnetic fields
ODINI manipulates CPU workload to generate controlled low-frequency magnetic fields. The malware can vary the load across CPU cores and use those changes to encode data into magnetic emissions.
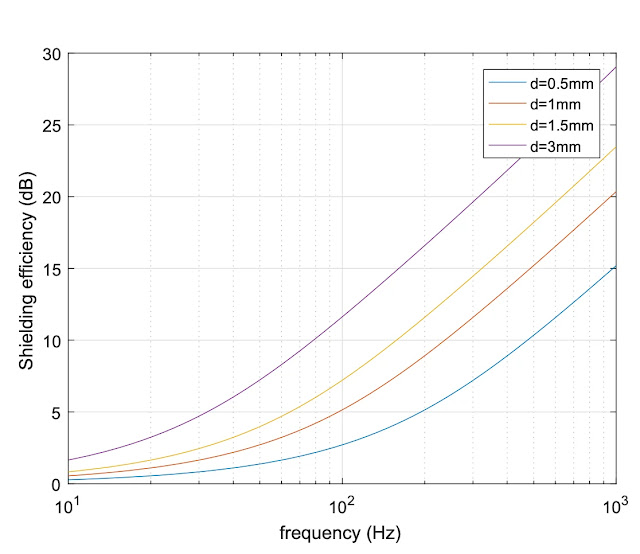
That matters because Faraday cages are mainly designed to block electromagnetic signals. Low-frequency magnetic fields can still penetrate metal shielding more effectively than many radio-frequency signals.
In the ODINI model, a nearby magnetic sensor receives the signal and converts it back into data. The transmitted information could include passwords, encryption keys, short documents, authentication tokens, or other compact secrets.
Key facts at a glance
| Item | Details |
|---|---|
| Technique name | ODINI |
| Research type | Proof-of-concept covert channel |
| Main target | Air-gapped computers protected by Faraday cages |
| Signal source | CPU-generated magnetic emissions |
| Receiver | Nearby magnetic sensor |
| Privileges required | User-level execution, no admin or root access required |
| Reported data rate | 1 to 40 bits per second, depending on distance and hardware |
| Main limitation | The attacker needs prior infection and a nearby receiver |
Why Faraday shielding is not enough
Faraday cages can reduce or block many forms of electromagnetic leakage. That is why military, government, financial, and critical infrastructure environments may use shielded rooms or enclosures around sensitive systems.
ODINI targets a different leakage path. Instead of relying on network signals, Wi-Fi, Bluetooth, or normal radio communication, it uses magnetic emissions caused by CPU power changes.
The researchers showed that magnetic signals could be observed from several types of computers, including desktops, a laptop, a server, and a small-form-factor PC. In their tests, signal reception reached up to 150 centimeters in some conditions, while practical data transfer depended heavily on distance and error rate.
The data rate is low but still useful
ODINI is not designed to steal large files quickly. Its reported data rate ranges from 1 to 40 bits per second, and the fastest rates work only when the receiver sits close to the target machine.
That still creates risk for small high-value secrets. A password, private key fragment, encryption key, recovery phrase, or token can fit into a small amount of data.
At longer distances, the channel becomes slower and less reliable. The research found that 1 bit per second worked at longer tested ranges, while 10 and 40 bits per second were feasible only at close range.
MAGNETO uses the same idea with a smartphone
The related MAGNETO research uses a similar CPU workload technique but receives the signal through a smartphone magnetometer. That is the sensor a phone normally uses for compass functionality.
The MAGNETO paper showed that the channel can still work when a smartphone sits in airplane mode or inside a Faraday shielding case. That makes the research important for secure areas where phones are allowed but wireless interfaces are disabled.
In practice, the smartphone must be very close to the compromised computer. This makes strict device zoning one of the most important defenses against this class of attack.
Why antivirus tools may miss the transmitter
The ODINI transmitter does not need special CPU instructions, suspicious system calls, or admin privileges. It can run as a normal user-level process.
That makes the behavior difficult to classify as malware through traditional signatures. A process that generates CPU load may look like a normal computation, software build, encryption task, benchmark, or analytics job.
Detection becomes harder in environments where systems already run heavy workloads. Defenders need context, baseline behavior, and physical security controls, not only endpoint malware signatures.
What defenders should watch for
- Unexpected CPU workload patterns on isolated systems.
- Repeated low-frequency workload modulation from untrusted processes.
- Unknown user-level programs running on high-security machines.
- Unauthorized phones, sensors, development boards, or electronics near protected systems.
- Changes to secure-area rules that allow new devices near air-gapped computers.
- Unexplained magnetic activity near shielded rooms or secure workstations.
How organizations can reduce the risk
The strongest defense is strict physical zoning. Sensitive systems should remain separated from phones, magnetic sensors, embedded devices, and any electronics that could act as receivers.
Organizations can also use hardware-based magnetic jamming or magnetic field monitoring in the most sensitive environments. These controls can add cost and complexity, so they usually make sense only for high-security facilities.
Software-based jamming is another option. Random CPU workloads can interfere with the covert signal, but they may reduce system performance and may not suit real-time or mission-critical systems.
ODINI is a warning, not a mass malware outbreak
ODINI should not be treated like common ransomware or commodity infostealer malware. It is research that demonstrates what a skilled attacker could do after compromising a highly restricted computer.
The attack also requires physical proximity. An attacker needs a receiver close enough to collect the magnetic signal, which makes this more relevant to espionage, insider risk, and high-value targeted environments than ordinary consumer systems.
Still, the research challenges a common assumption. Air gaps and Faraday cages can reduce many attack paths, but they do not make data exfiltration impossible once malware is already running on the protected machine.
FAQ
ODINI is a proof-of-concept malware technique that leaks data from air-gapped computers by modulating CPU-generated magnetic fields.
No. ODINI focuses on data exfiltration after the target machine is already infected. The attacker still needs an initial compromise path.
The research shows that low-frequency magnetic signals generated by CPU workload changes can penetrate Faraday shielding under tested conditions.
The researchers reported data transfer rates from 1 to 40 bits per second. Higher speeds require close proximity between the target machine and the receiver.
Summary
- ODINI shows that CPU-generated magnetic emissions can leak data from air-gapped systems.
- The technique can work even when a computer sits inside Faraday shielding.
- The malware needs prior access to the target machine and a nearby magnetic receiver.
- The data rate is low, but it can still expose compact secrets such as passwords or keys.
- Physical zoning and receiver bans remain essential for highly sensitive environments.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages