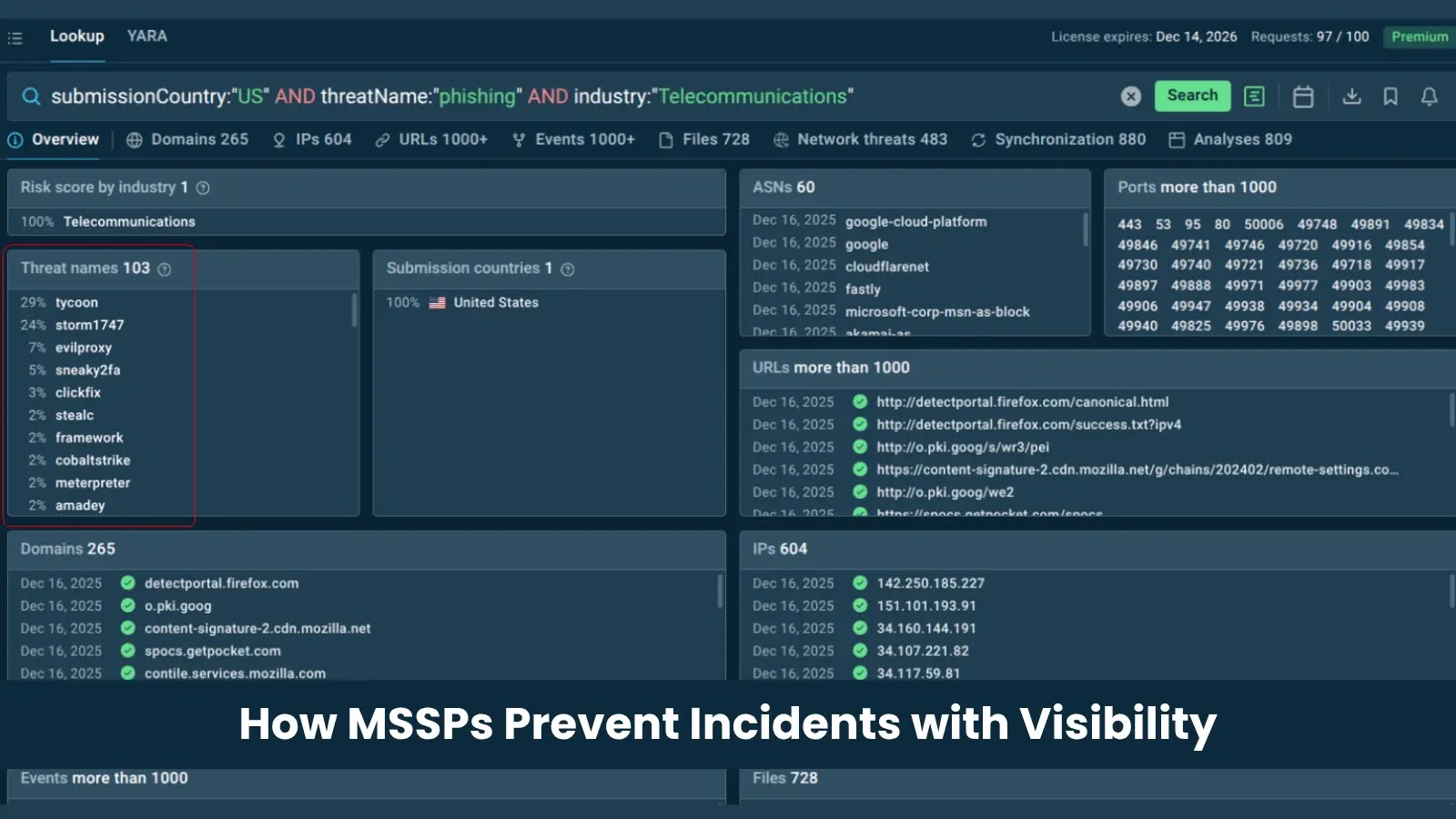
Threat actors use Vercel AI tools to create realistic phishing sites at scale

Threat actors are abusing Vercel and its AI website-building tools to create realistic phishing pages that imitate trusted brands and steal login credentials.
Cofense researchers say attackers use Vercel’s GenAI capabilities, hosting, quick deployment, and third-party integrations to build convincing fake sign-in pages with far less effort than traditional phishing kits required.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The risk is practical and immediate. A phishing page that looks clean, loads quickly, and copies a familiar brand can trick users who still rely on spelling mistakes or poor design to spot scams.
Vercel phishing abuse at a glance
| Detail | Information |
|---|---|
| Main platform abused | Vercel |
| AI tool mentioned by researchers | v0, previously known as v0.dev |
| Main attack type | Credential phishing |
| Common lures | Fake sign-in pages, job offers, interview invitations, and brand impersonation |
| Brands observed in examples | Microsoft, Adidas, Nike, and Spotify |
| Extra abuse path | Telegram bot integrations for credential delivery |
| Main defense | Verify domains before entering credentials |
How attackers abuse AI-generated web pages
Vercel’s v0 product lets users create web apps and pages from text prompts. In normal use, this helps developers, designers, founders, and teams build faster.
Attackers are using the same speed for phishing. Cofense says a threat actor can prompt the tool to create a fake Microsoft sign-in page, then adjust the page until it resembles the real service.
This lowers the skill barrier. A criminal no longer needs to write the full page by hand, buy a phishing kit, or run complex hosting infrastructure to create a polished login page.
Why these phishing pages are harder to spot
Older phishing training often told users to look for spelling errors, broken layouts, strange colors, or poor grammar. AI-generated pages can remove many of those obvious warning signs.
Cofense says Vercel-hosted phishing pages can closely copy legitimate layouts, logos, colors, and page behavior. That makes visual inspection less reliable.
The URL becomes the most important clue. Even a convincing fake login page still needs to run on a different domain or subdomain than the real service.
Telegram makes credential theft faster
Cofense also observed attackers combining Vercel phishing pages with Telegram bot integrations. This gives criminals a quick way to receive stolen credentials after a victim enters them.
Telegram bots can send messages, upload files, and automate data delivery through the Telegram Bot API. Cofense has separately reported that threat actors use Telegram bots for credential theft and other data exfiltration activity.
This combination makes phishing operations easier to run. Vercel can host the fake page, while Telegram can deliver stolen credentials to the attacker in near real time.
Real campaigns used job and brand lures
Cofense documented phishing campaigns that used fake job offers and interview invitations to pull users into brand-themed pages. In one case, attackers posed as an Adidas hiring manager and led users to a fake careers page.
Researchers also described Nike job-posting lures and Microsoft-themed sign-in pages. These campaigns take advantage of familiar brands and common workflows that employees already trust.
Another example involved a fake Spotify login page. Cofense said the page copied the real service’s logos, wording, color scheme, and functionality before sending stolen credentials to the attacker and redirecting the victim to a page asking for payment card details.
Why Vercel is attractive to attackers
- AI prompts can generate realistic phishing pages quickly.
- Cloud hosting removes the need for attackers to manage their own infrastructure.
- Pages can be redeployed if one version gets removed.
- Different AI outputs help attackers create variations of the same lure.
- Integrations with other services can support automation and credential collection.
- Trusted-looking hosted pages can bypass a user’s visual expectations.
Vercel says it uses moderation and abuse reporting
Vercel’s transparency report says the company uses proactive and reactive moderation against harmful content. This includes detection systems, reporting tools, human review, and content moderation workflows.
The company also has an abuse reporting page for malicious or illegal activity involving Vercel-hosted sites. The form includes categories for phishing or malware, copyright complaints, trademark violations, and other abuse.
That reporting path matters because phishing pages often move quickly. Security teams should report active Vercel-hosted phishing pages while also blocking the domains in email, DNS, proxy, and browser controls.
How organizations should defend users
| Risk | Recommended action |
|---|---|
| Convincing fake login pages | Train users to verify the domain before entering credentials |
| Vercel-hosted phishing links | Monitor inbound mail for suspicious vercel.app URLs |
| Credential theft | Use phishing-resistant MFA or passkeys where possible |
| Fast page redeployment | Block confirmed malicious URLs and related infrastructure quickly |
| Brand impersonation | Use domain monitoring and takedown workflows |
| User confusion | Make reporting suspicious links simple inside email clients |
What users should check before signing in
Users should not trust a page only because it looks professional. AI-generated phishing pages can look clean, polished, and familiar.
The safest habit is to check the full browser address before typing a password. Users should confirm that the domain belongs to the service they intended to visit.
When a login page appears after clicking an email link, users should stop and open the service directly from a saved bookmark or by typing the known address manually.
Practical steps for security teams
- Search mail logs for suspicious Vercel-hosted links.
- Block confirmed phishing URLs at the email gateway, DNS layer, and secure web gateway.
- Report malicious Vercel-hosted pages through Vercel’s abuse form.
- Update phishing training to focus on domains, login flows, and unexpected redirects.
- Deploy phishing-resistant MFA for high-risk accounts.
- Review credential use after any user submits data to a suspected phishing page.
- Monitor for Telegram bot indicators in phishing investigations where available.
The bottom line
AI website builders have made phishing faster, cheaper, and more polished. Attackers can now create pages that look credible without advanced web development skills.
That does not make phishing impossible to detect. It changes what users and defenders should focus on.
Organizations should move away from training that relies mainly on spelling mistakes or ugly page design. Domain checks, phishing-resistant authentication, mail filtering, browser protections, and fast takedown reporting now matter more.
FAQ
Users should check the full domain in the browser address bar before entering credentials and avoid logging in through unexpected email links.
They can look polished and familiar, which makes them harder for users to spot through design mistakes or grammar errors.
v0 is Vercel’s AI builder for creating apps and websites from prompts. Vercel says v0.dev became v0.app in 2025.
Attackers are using Vercel’s AI web-building and hosting features to create realistic fake login pages that imitate trusted brands and collect credentials.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages