Bitwarden CLI npm Package Compromised in Developer Credential Theft Attack

Bitwarden has confirmed that a malicious version of its @bitwarden/cli npm package was briefly distributed through npm on April 22, 2026. The affected release, @bitwarden/[email protected], was available for about 93 minutes, between 5:57 PM and 7:30 PM ET, before Bitwarden removed and deprecated it.
The company says the incident affected only the npm delivery path for the CLI package during that short window. Bitwarden said it found no evidence that end-user vault data, production data, or production systems were accessed or compromised.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The malicious package still created serious risk for developers and CI/CD environments. Security researchers at Socket, JFrog, OX Security, and Endor Labs found that the payload could steal npm tokens, GitHub tokens, SSH keys, cloud credentials, shell history, environment files, and other secrets from infected systems.
How the Bitwarden CLI attack worked
JFrog said attackers hijacked the legitimate @bitwarden/cli npm package version 2026.4.0 and kept its expected Bitwarden metadata. The malicious release changed the preinstall script and the bw command entry point so both ran a custom loader called bw_setup.js instead of the normal bundled CLI.
That loader checked whether the Bun runtime existed on the machine. If Bun was missing, the loader downloaded it, then used it to run an obfuscated JavaScript payload named bw1.js.
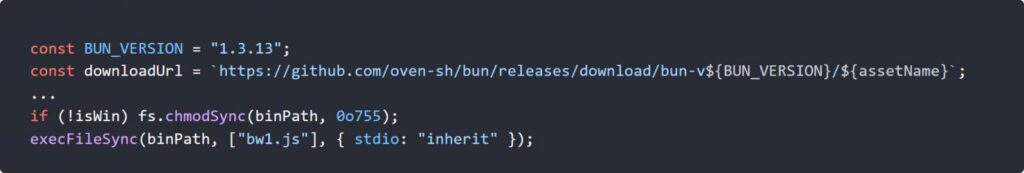
Source: Jfrog
The payload then searched the system for developer secrets. OX Security said the malware encrypted stolen data and uploaded it to public GitHub repositories created under the victim’s own account. Those repositories included the phrase “Shai-Hulud: The Third Coming,” linking the activity to earlier npm worm campaigns.
At a glance
| Item | Details |
|---|---|
| Package | @bitwarden/cli |
| Malicious version | 2026.4.0 |
| Distribution channel | npm |
| Exposure window | April 22, 2026, 5:57 PM to 7:30 PM ET |
| Main target | Developers and CI/CD environments |
| Bitwarden vault data affected | No evidence of access |
| Production systems affected | No evidence of compromise |
| Loader | bw_setup.js |
| Main payload | bw1.js |
| Runtime used | Bun |
| Data stolen | npm tokens, GitHub tokens, SSH keys, cloud credentials, .env files |
| Exfiltration method | Encrypted data uploaded to public GitHub repositories |
| Campaign marker | “Shai-Hulud: The Third Coming” |
Why this was dangerous for developers
The package was live for less than two hours, but npm packages can execute code during installation. That means a developer, CI runner, build container, or automated deployment system that installed the malicious version may have run the payload immediately.
The main risk was not password vault theft. The risk was developer credential theft, especially from machines and CI/CD systems that hold access tokens for GitHub, npm, AWS, Azure, Google Cloud, SSH, and internal build systems.
Socket said the attack appears to have abused a compromised GitHub Action in Bitwarden’s CI/CD pipeline. Bitwarden later linked the incident to a broader Checkmarx supply chain attack, and Socket said the Bitwarden payload shared infrastructure and code patterns with the Checkmarx incident.
What the malware tried to steal
Researchers reported that the payload targeted secrets commonly found on developer machines and build systems. These secrets can let attackers move from one package or repository to many more.
| Targeted secret type | Why attackers want it |
|---|---|
| npm tokens | Publish malicious versions of other packages |
| GitHub tokens | Access repositories, workflows, and secrets |
| SSH keys | Connect to servers or private repositories |
| AWS credentials | Access cloud infrastructure and storage |
| Azure credentials | Access Microsoft cloud resources |
| Google Cloud credentials | Access cloud projects and service accounts |
.env files | Extract application secrets and API keys |
| Shell history | Find commands containing credentials |
| CI/CD secrets | Spread through automated build pipelines |
OX Security also said the malware had self-propagation behavior. It could use stolen npm credentials to find packages the victim could modify and inject malicious code into them.
Connection to Checkmarx and TeamPCP
Bitwarden said the malicious npm package was connected to a broader Checkmarx supply chain incident. The company said compromised access was revoked, the malicious npm release was deprecated, and remediation steps started immediately.
Socket reported that the Bitwarden payload used the same audit.checkmarx[.]cx/v1/telemetry endpoint seen in the Checkmarx incident. It also shared an obfuscation routine and the same pattern of credential theft, GitHub-based exfiltration, and supply chain propagation.
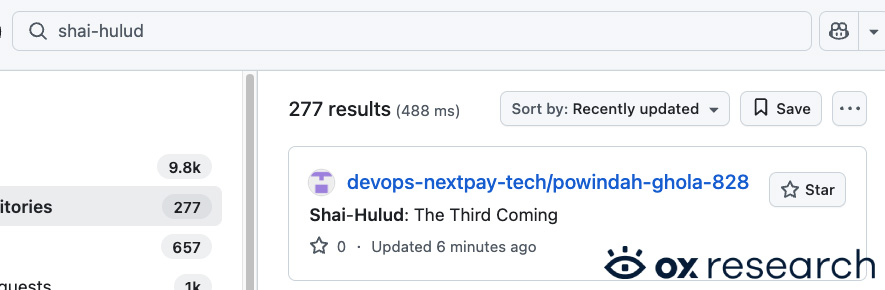
Source: OX Security
SecurityWeek reported that the incident has been tied to TeamPCP, a threat actor connected to earlier open-source supply chain campaigns.
Why the npm ecosystem remains exposed
This attack shows how a trusted package can become dangerous even when the project’s normal codebase remains intact. Developers may trust the package name, publisher reputation, and automation pipeline, but npm install scripts can still run attacker code before a user notices anything wrong.
The attack also shows how CI/CD systems have become high-value targets. A developer laptop may contain some secrets, but a build runner can hold tokens that publish packages, update production infrastructure, or access many repositories.
The risk grows when organizations allow automatic installs of latest package versions without pinning, lockfiles, artifact verification, or install script restrictions.
What affected developers should do now
- Check whether
@bitwarden/[email protected]was installed on any developer machine, container, or CI runner. - Treat any system that installed the package during the affected window as compromised.
- Rotate npm tokens, GitHub tokens, SSH keys, and cloud credentials.
- Review AWS, Azure, and Google Cloud logs for suspicious access.
- Check GitHub accounts for newly created public repositories containing unknown encrypted data.
- Search for repositories or commits referencing “Shai-Hulud: The Third Coming.”
- Rebuild affected CI runners from clean images.
- Review package publishing logs for unexpected npm releases.
- Disable or restrict npm lifecycle scripts in CI where possible.
- Pin dependencies and avoid automatic upgrades to unreviewed package versions.
What Bitwarden users should know
Bitwarden says vault data was not accessed and its production systems were not compromised. The issue affected the npm distribution mechanism for the CLI package, not the integrity of the legitimate Bitwarden CLI codebase or stored vault data.
Users who did not install @bitwarden/[email protected] from npm during the affected window do not fall into the known affected group.
Developers and organizations that did install the affected version should focus on rotating developer and infrastructure credentials rather than changing Bitwarden vault passwords only.
FAQ
Attackers published a malicious @bitwarden/[email protected] package to npm. The package contained a credential-stealing payload and was available for about 93 minutes on April 22, 2026.
Bitwarden says it found no evidence that end-user vault data was accessed or at risk. It also says production data and production systems were not compromised.
Developers, CI systems, or automated environments that installed @bitwarden/[email protected] from npm during the affected window were at risk.
Researchers said the malware targeted npm tokens, GitHub tokens, SSH keys, cloud credentials, environment files, shell history, and CI/CD secrets.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages