Critical ExifTool flaw lets malicious images run code on macOS

A newly disclosed ExifTool vulnerability can let a malicious image trigger command execution on macOS during metadata processing. The flaw affects ExifTool 13.49 and earlier on macOS, and researchers say attackers can abuse the DateTimeOriginal metadata field to inject commands when the tool runs in a specific mode. Kaspersky’s GReAT team reported the issue, and ExifTool fixed it in version 13.50.
The vulnerability is tracked as CVE-2026-3102. Public advisories describe it as an OS command injection issue tied to ExifTool’s SetMacOSTags function in lib/Image/ExifTool/MacOS.pm, with the vulnerable path involving the PNG file parser. NVD says the bug can be exploited remotely, while the CVSS vector published for the flaw reflects user interaction because a target system still has to process the malicious file.
For most users, the immediate takeaway is simple: updating ExifTool closes the known issue. The bigger concern is that ExifTool often works behind the scenes inside photo workflows, digital asset tools, forensic pipelines, and automation scripts, so some organizations may use a vulnerable build without realizing it. Kaspersky specifically warns that apps and workflows built on ExifTool may also need checking for embedded older versions.
What happens in this ExifTool attack?
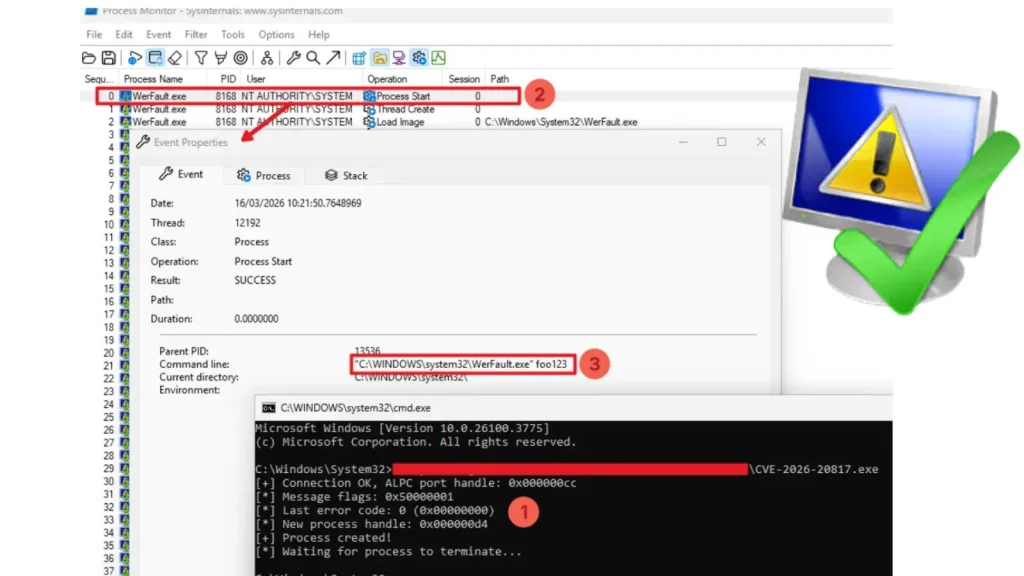
Researchers say the attack hides shell commands inside a malformed DateTimeOriginal value in an image’s metadata. The picture itself can look harmless. When a vulnerable ExifTool build on macOS processes that metadata under the right conditions, the injected command can run on the host.
Kaspersky says exploitation needs two conditions:
- The file must be processed on macOS
- ExifTool must run with the
-nor--printConvflag enabled
That flag matters because it tells ExifTool to output machine-readable values without normal conversion. Kaspersky says this behavior helps make the malicious metadata path exploitable.
Why this matters
ExifTool is widely used to read and edit metadata in images, videos, and PDFs. Because it often runs as part of automated content handling, a single crafted image could become an entry point for a broader compromise if an exposed workflow processes untrusted files on macOS. Kaspersky says attackers could use the initial command execution to fetch and launch follow-on payloads.
This does not mean every Mac that opens an image is vulnerable. The risk centers on systems and applications that actually invoke vulnerable ExifTool code under the affected conditions. That distinction matters for incident response and patch prioritization.
Key details at a glance
| Item | Details |
|---|---|
| CVE | CVE-2026-3102 |
| Affected software | ExifTool 13.49 and earlier on macOS |
| Vulnerability type | OS command injection / remote code execution path |
| Trigger | Crafted image metadata in DateTimeOriginal |
| Extra condition | ExifTool run with -n / --printConv |
| Fix | Upgrade to ExifTool 13.50 or later |
The fix landed in ExifTool 13.50 on February 7, 2026. ExifTool’s version history explicitly says that release “Patched potential MacOS security issue.”
What organizations should do now
Security teams should move quickly because vulnerable ExifTool builds may sit inside more than one workflow.
- Update ExifTool to 13.50 or later
- Check media pipelines, DAM platforms, and scripts for embedded older ExifTool copies
- Review whether any workflow on macOS uses the
-nor--printConvoption - Process untrusted files in isolated environments
- Monitor macOS endpoints for suspicious child processes or unexpected downloads after image ingestion
For defenders, supply chain visibility matters here. A direct ExifTool update may not be enough if a third-party app ships its own bundled version. Kaspersky calls this out clearly in its mitigation guidance.
FAQ
Yes. Public advisories for CVE-2026-3102 describe the issue as affecting ExifTool up to 13.49 on macOS.
Not necessarily in the usual sense. The important step is that a vulnerable workflow must process the malicious file. That could happen in an automated pipeline, not only through a person double-clicking an image.
Kaspersky says attackers can place the malicious content in the DateTimeOriginal metadata field using an invalid format.
ExifTool 13.50 introduced the patch, and newer versions also include it.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages