CryptoPro Secure Disk for BitLocker Vulnerabilities Enable Root Access and Credential Theft

Attackers with physical access can exploit flaws in CryptoPro Secure Disk (CPSD) for BitLocker to gain root privileges and steal credentials. These issues affect the software’s Linux pre-boot environment. Researchers at SEC Consult Vulnerability Lab found two key vulnerabilities. CPSD confirms patches fix them in versions 7.6.6 and 7.7.1. Their advisory states: “Update to mitigate integrity bypass (CVE-2025-10010) and cleartext storage risks.”
CPSD protects Windows partitions with BitLocker encryption. It runs a minimal Linux system on an unencrypted partition for user authentication. Physical access lets anyone boot this system. The first flaw bypasses file integrity checks. This allows root code execution.
SEC Consult reported the issues in June 2025. CPSD released fixes promptly. No active exploits appear in public feeds as of February 26, 2026. Check CPSD updates and CVE details for latest status.
The integrity bypass targets Linux Integrity Measurement Architecture (IMA). IMA verifies files but skips config files. Attackers alter them to run shells or backdoors. A simple tweak executes code like a reverse shell without alerts.
Vulnerability Details
| CVE | CVSS | Impact | Fixed In |
|---|---|---|---|
| CVE-2025-10010 | N/A (High) | Root code execution via integrity bypass | 7.6.6 / 7.7.1 |
| N/A | N/A (Medium) | Cleartext creds in /tmp expose networks | 7.6.6 / 7.7.1 |
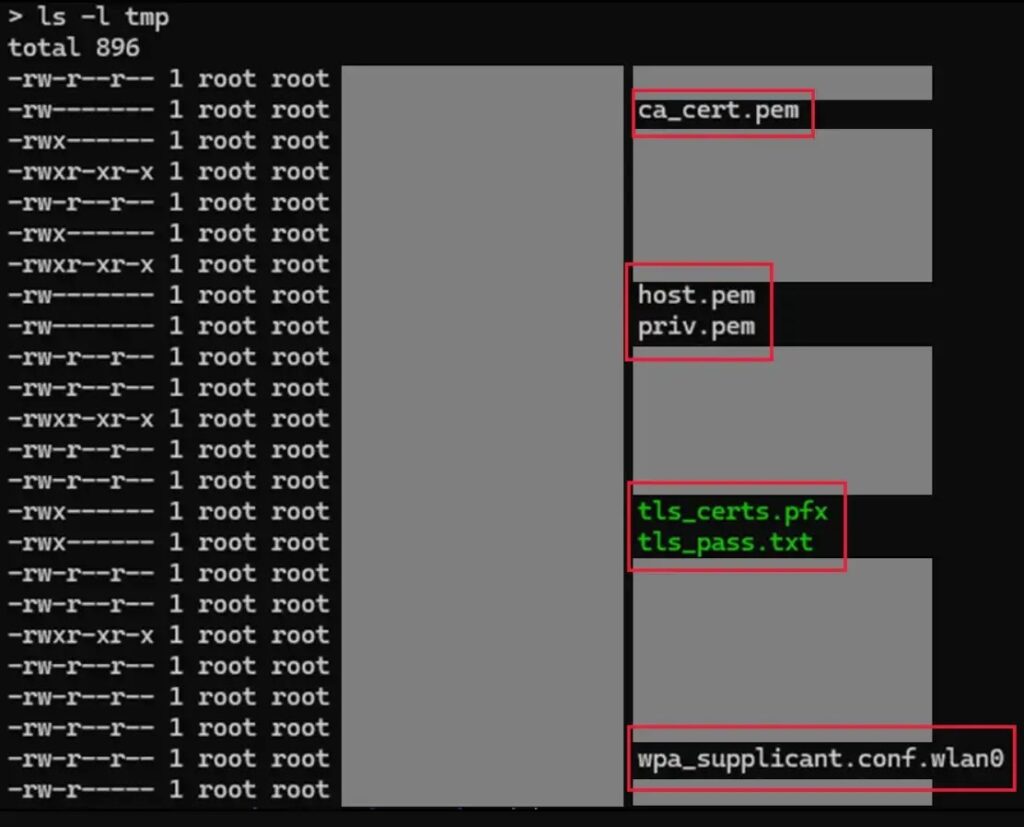
The second flaw hits the “forgot password” feature. It stores certs and WLAN passwords in plain text under /tmp. Root access from the first vuln lets attackers grab them. This bypasses 802.1X controls and grants network entry.
Organizations in high-security sectors use CPSD for endpoint protection. Physical theft risks rise with remote work. One compromised device exposes encrypted data and internals.
Affected Versions and Patches
- Vulnerable: Below 7.6.6 or 7.7.1
- Fixed: 7.6.6 (encrypts PBA partition); 7.7.1 (default encryption)
- Workaround: Enable PBA encryption if on 7.6.0+
CPSD notes: “Encrypt the pre-boot partition to block modifications.”
Protection Steps
Act fast to secure systems.
- Update to 7.6.6 or later immediately.
- Encrypt PBA partitions manually if needed.
- Limit physical access; use TPM 2.0 full-disk encryption.
- Audit encryption tools yearly.
- Monitor boot logs for tampering.
FAQ
Root access via integrity bypass and credential theft from /tmp.
7.6.6 and 7.7.1 or higher.
Physical access to boot the unencrypted Linux partition.
No confirmed wild exploits as of February 2026.
Encrypt PBA partition (available since 7.6.0).
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages