Iran cyber conflict widens after Epic Fury and Roaring Lion, but many attack claims still lack proof

The cyber side of the Iran conflict is clearly growing, but the picture is messy. After the United States and Israel launched their joint campaign on February 28 under Operation Epic Fury and Operation Roaring Lion, official statements, intelligence reporting, and security warnings all pointed to a higher risk of retaliatory cyber activity. At the same time, many of the loudest hacktivist claims spreading online still lack independent verification.
The core facts are easier to confirm than the battlefield chatter. The White House publicly confirmed Operation Epic Fury, and the IDF said it launched Operation Roaring Lion together with U.S. forces on February 28. Reuters also reported that the opening phase included cyber and space-based disruption before the broader military strikes.
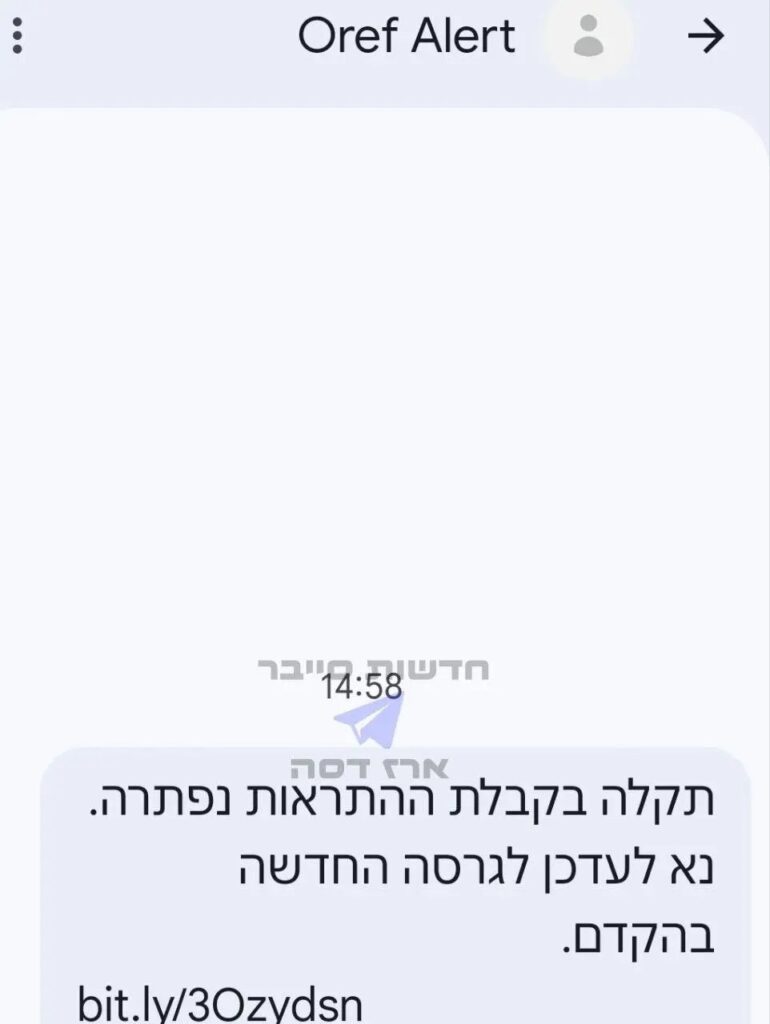
Iran’s loss of connectivity is also well documented. NetBlocks data cited by multiple outlets showed national connectivity falling to about 4% of normal levels on February 28, then closer to 1% during the blackout, with restrictions entering a fourth day on March 3. That matters because the outage does two things at once: it can disrupt command, coordination, and public communication inside Iran, and it also makes outside verification much harder.
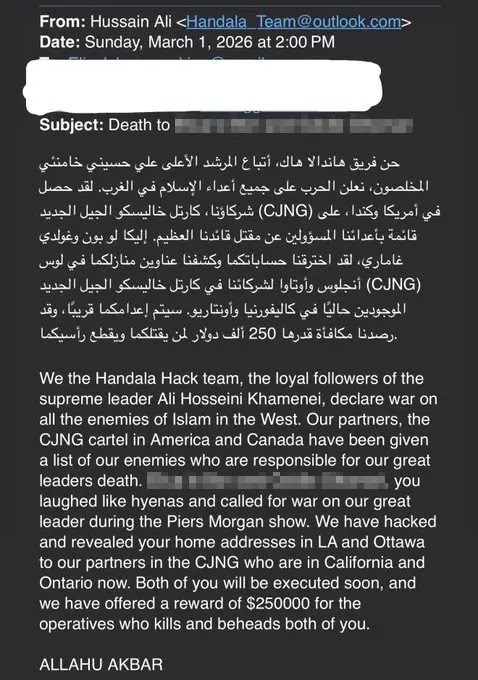
What comes next looks less like one clean state-on-state cyber campaign and more like a crowded, fast-moving digital conflict. Reuters reported cyber operations against Iranian apps and websites soon after the strikes. A U.S. intelligence assessment reported by Reuters then warned that Iran and its proxies could step up defacements and DDoS attacks. The UK’s NCSC took a more measured line, saying there is likely no significant change in the direct cyber threat to the UK right now, but there is almost certainly a heightened indirect risk for organizations with offices or supply chains in the Middle East.
That gap between confirmed risk and unverified claims is important. Public monitoring from CloudSEK and reporting that cites CyberKnow both point to a surge in hacktivist activity, including pro-Iran and pro-Russian groups, but much of that activity is self-claimed on Telegram or similar channels. In plain terms, the conflict is real, the cyber risk is rising, but some of the dramatic breach claims still sit in the “possible, not proven” bucket.
What is confirmed, and what still needs proof
| Item | Status | What the evidence shows |
|---|---|---|
| Joint U.S.-Israeli operation began on February 28 | Confirmed | The White House confirmed Operation Epic Fury, and the IDF confirmed Operation Roaring Lion. |
| Cyber disruption formed part of the opening phase | Confirmed by Reuters reporting | Reuters reported cyber and space-based disruptions in the first phase of the campaign. |
| Iran suffered a near-total internet blackout | Confirmed by network monitoring cited in reporting | NetBlocks data cited by Forbes and other outlets showed connectivity falling sharply, then flattening around 1%, with the blackout entering day four on March 3. |
| Retaliatory cyber activity is expected | Confirmed by official warning | A U.S. intelligence assessment reported by Reuters warned of likely defacements and DDoS incidents from Iran-backed actors and proxies. |
| Dozens of hacktivist groups are now active | Plausible, but partly self-reported | CloudSEK logged more than 150 hacktivist incident claims in open channels, and CyberKnow said about 60 groups were engaged. Those figures describe claimed activity, not fully verified breaches. |
| Specific claims about major infrastructure compromises | Largely unverified in public reporting | Analysts and media have repeated some claims, but public technical proof remains limited in many cases. |
Why the blackout changes the cyber fight
Iran going mostly offline does not end the cyber threat. It changes it. The blackout can slow central coordination and reduce visibility into what domestic Iranian operators are doing in real time, but it can also push activity toward proxies, foreign infrastructure, and loosely aligned hacktivist groups outside Iran. Reuters, NCSC, and CISA all point to the same broader lesson: organizations should prepare for retaliation that may be disruptive, opportunistic, and harder to attribute than a classic military cyber operation.
That is why the current risk picture looks broader than Iran alone. The NCSC warned UK organizations with regional exposure to review monitoring and external attack surface. CISA’s Iran threat overview says Iranian actors routinely target poorly secured U.S. networks and internet-connected devices, especially exposed edge systems and operational technology. Older joint U.S. advisories also show familiar tradecraft such as brute force, password spraying, weak credentials, and attacks on critical infrastructure.
What security teams should do now
| Priority | Why it matters now | Source basis |
|---|---|---|
| Increase monitoring on internet-facing systems | Retaliation often starts with weak edge devices, exposed services, and basic credential abuse. | CISA, joint U.S. advisory |
| Review DDoS readiness and communications plans | Official warnings and current reporting both highlight defacement and DDoS as likely near-term tactics. | Reuters, NCSC |
| Tighten MFA and password hygiene | Iranian actors have repeatedly used brute force, password spraying, and MFA abuse. | CISA, FBI, NSA and partners |
| Recheck third-party and regional supply-chain exposure | NCSC says indirect risk is higher for organizations with offices or supply chains in the Middle East. | NCSC |
| Treat dramatic Telegram breach claims with caution | Claimed attacks are rising faster than verified incidents. | CloudSEK, CyberKnow-cited reporting |
Practical takeaways for defenders
- Expect noisy activity first, especially DDoS, defacement, phishing, and hack-and-leak style claims.
- Do not assume the blackout inside Iran means the threat has faded. It may simply become less visible and more distributed.
- Focus on basics that still matter most: patch exposed systems, harden authentication, segment critical systems, and rehearse incident response.
- Separate verified incidents from propaganda. In fast-moving conflicts, attackers and sympathizers often exaggerate success for psychological effect.
FAQ
Yes. The military campaign is official, Iran’s connectivity collapse is widely documented, and official warnings now point to a higher risk of retaliatory cyber activity, especially defacements, DDoS, and opportunistic attacks.
Public network monitoring cited in reporting showed connectivity drop to about 4% at first and then around 1%, with the outage entering its fourth day on March 3.
Not in many cases. Open-source monitoring shows a jump in claimed attacks, but a large share of those claims still lacks public technical validation.
Organizations with operations, staff, vendors, or supply chains tied to the Middle East face the clearest indirect risk. Critical infrastructure operators and firms with exposed edge systems should also stay alert.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages