JanaWare ransomware is targeting Turkish users through a modified Adwind RAT, Acronis says

A new ransomware operation called JanaWare appears to be targeting users in Turkey through a customized version of the Adwind remote access trojan, according to Acronis Threat Research Unit. The company says the campaign uses malicious Java archive files, geofencing checks, and a separate ransomware module that activates only when the victim environment matches Turkish language and location signals.
Acronis says the campaign has likely been active since at least 2020, with a sample compiled in November 2025 showing that related command-and-control infrastructure remained active during the company’s analysis. The researchers say the apparent victim pool centers on home users and small to medium-sized businesses, not large enterprises.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The ransom demands also stand out. Acronis says analyzed samples asked for about $200 to $400, which is far below the multimillion-dollar demands seen in many enterprise ransomware cases. That points to a lower-value, higher-volume model built to pressure smaller victims into paying quickly.
How the infection chain works
According to Acronis, the attack starts with phishing emails that deliver or link to a malicious JAR file. Once the victim opens it, the file runs through Java and loads a customized Adwind variant that acts as the main access tool and delivery channel for the ransomware stage.
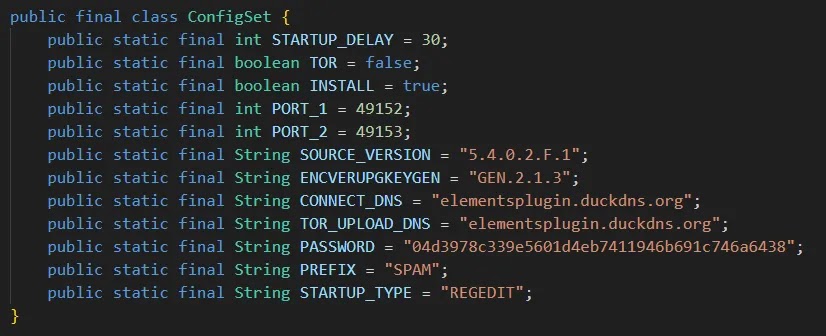
Acronis says the attackers then decide whether to continue based on locale, language, and external IP geolocation. If the machine does not appear to be in Turkey, the malware stops. That likely helped the campaign stay hidden from many researchers and automated sandboxes outside the country.
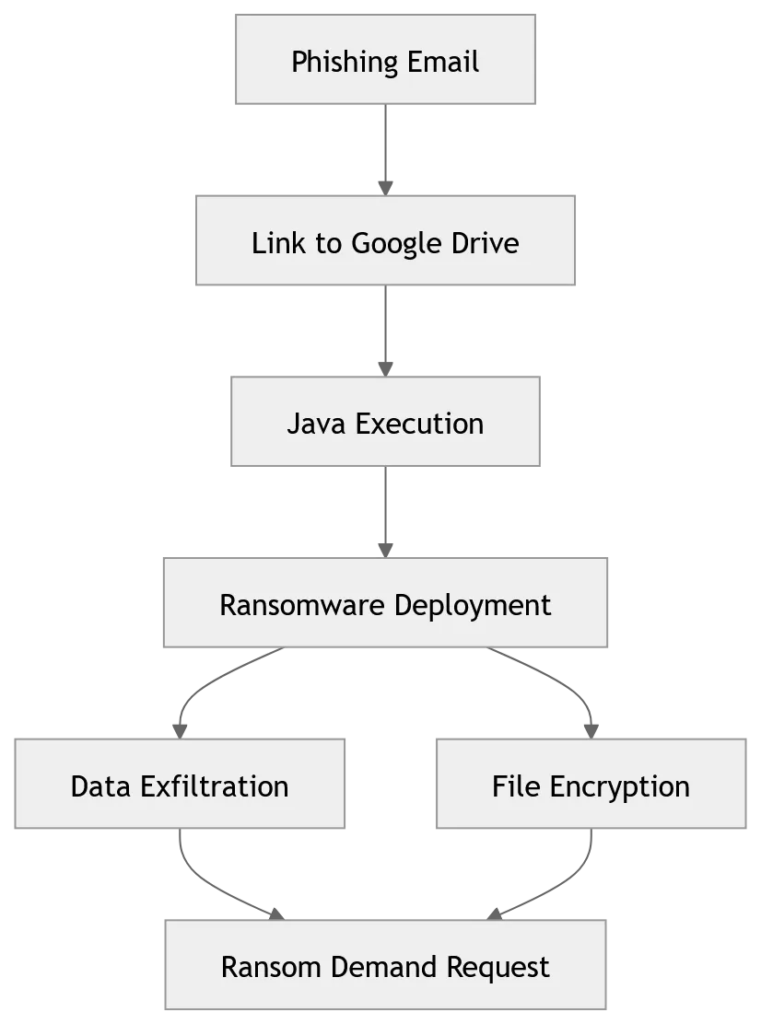
If the checks pass, the malware weakens defenses before encryption begins. Acronis says it runs PowerShell and registry changes to interfere with Microsoft Defender, suppress security notifications, remove Volume Shadow Copy backups, disable Windows Update, and inspect installed antivirus products. The ransomware then encrypts files with AES and sends the key to its command server over Tor, which makes recovery much harder without attacker cooperation.
Why JanaWare stands out
One unusual detail is the use of Adwind, also known in MITRE ATT&CK as part of the jRAT malware family. MITRE describes it as a cross-platform Java-based backdoor with a long history, which helps explain why a modified Java RAT can still serve as an effective loader and access tool in 2026.
Acronis also says the malware uses two public Java obfuscators, Stringer and Allatori, and includes a FilePumper class that adds random content to its own JAR during installation. That changes the file hash from victim to victim, which weakens simple hash-based detection.
The communication methods also show deliberate planning. Acronis says victims receive Turkish-language ransom notes and are told to contact the attackers through qTox or via a Tor hidden service. The report describes that as a way to reduce traceability and make disruption harder for defenders and law enforcement.
JanaWare at a glance
| Area | What Acronis found |
|---|---|
| Main delivery method | Phishing emails leading to malicious JAR files |
| Loader / access tool | Customized Adwind RAT variant |
| Geographic targeting | Turkish locale and IP-based geofencing |
| Main victims | Home users and SMBs in Turkey |
| Ransom demand | Roughly $200 to $400 |
| Communications | qTox and Tor hidden services |
| Defense evasion | Obfuscation, polymorphism, security feature tampering |
What users and defenders should do
The clearest defensive step is to reduce unnecessary Java execution. Oracle says organizations can use Java Management Service and related management tools to identify outdated Java installations, unauthorized applications, and runtime mismatches. In practice, that means defenders should review where Java is still needed and block untrusted JAR execution everywhere else.
Acronis also recommends stronger email filtering for messages that combine cloud-hosted links with executable content, plus network monitoring for the specific command-and-control infrastructure seen in the campaign. Even if those exact indicators change, the broader lesson holds: watch for Java-launched child activity, unusual outbound connections, and systems that suddenly disable security controls before encryption.
For resilience, CISA continues to recommend offline, encrypted backups that are tested regularly, along with response planning and hardening of internet-facing systems. That advice fits JanaWare well because once the malware removes shadow copies and sends the encryption key off the host, local recovery options can vanish quickly.
Key defensive actions
- Restrict Java Runtime Environment use on endpoints that do not need it.
- Block or quarantine suspicious emails carrying JAR files or cloud links tied to executable downloads.
- Monitor for outbound Tor-related activity and the infrastructure Acronis listed in its indicators.
- Treat Turkish-language ransom notes or unexplained
ONEMLI NOTfiles as urgent incident indicators. - Maintain offline backups and test restoration regularly.
FAQ
Acronis describes JanaWare as a ransomware module delivered through a customized Adwind RAT campaign focused on Turkish users.
Acronis says geofencing, Java obfuscation, and polymorphic behavior likely limited visibility, especially outside Turkey.
The report says the campaign mainly targets home users and small to medium-sized businesses in Turkey.
Acronis says the observed $200 to $400 range suggests a high-volume model aimed at victims who may pay quickly instead of pursuing lengthy recovery.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages