North Korean fake IT worker scheme keeps growing, with VPNs and laptop farms helping operatives look local

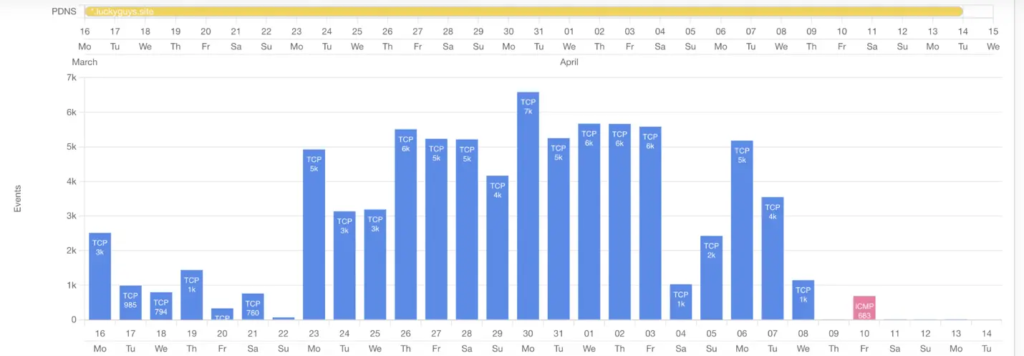
North Korea’s fake IT worker operation remains one of the most effective fraud and sanctions evasion schemes in the cyber world, and fresh research shows how the actors keep hiding in plain sight. Team Cymru says operatives linked to the scheme used infrastructure tied to the domain luckyguys[.]site, plus consumer VPN services and residential internet connections, to appear as legitimate remote workers while seeking jobs and moving money.
The goal is not just employment fraud. U.S. Treasury and the Justice Department have both said North Korean IT worker schemes generate revenue for Pyongyang and help fund its weapons programs, while also giving operatives a path into corporate networks and sensitive data.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The latest public reporting adds more technical detail to a threat that many companies still treat as a hiring problem instead of a security problem. Team Cymru found traffic linked to the identified infrastructure from U.S. and Latvian residential IP addresses, a pattern consistent with the use of proxy hosts or so-called laptop farms that make a foreign operator look like a local employee inside the United States.
How the operation works
The scheme starts with fake identities, fabricated resumes, and false professional histories. U.S. authorities say North Korean operatives pose as remote IT workers, often with help from facilitators, to win jobs at real companies in the United States and allied countries.
Once hired, the deception does not stop at onboarding. The Justice Department says facilitators have helped run laptop farms in the United States so employer-issued machines stay physically inside the country, even while the real worker operates elsewhere. That setup helps the traffic, timezone behavior, and device footprint look normal to employers.
Team Cymru’s research adds the network layer to that picture. It said the infrastructure it tracked showed heavy use of Astrill VPN, Mullvad, and Proton VPN, along with connections to services such as Gmail, ChatGPT, and Workana. Those tools help the workers communicate, search for jobs, and mask their true origin while blending into ordinary remote work activity.
Why companies should take this more seriously
This is not a niche fraud campaign. Treasury said in March 2026 that DPRK-facilitated IT teams use fraudulent documentation, stolen identities, and fabricated personas to obtain employment, and that the regime reportedly takes most of the wages earned by those workers to support weapons and ballistic missile programs.
The risk also goes beyond payroll loss. The FBI and DOJ have repeatedly warned that North Korean remote workers can gain access to employer systems, source code, intellectual property, and internal collaboration tools. In some cases, U.S. authorities say the schemes later turned to extortion after the workers obtained sensitive company data.
The Team Cymru findings support that wider warning. Researchers said the traffic tied to luckyguys[.]site dropped sharply after public exposure, suggesting the operators closely monitor attribution and abandon infrastructure quickly when defenders start looking in the right place. That kind of response fits a disciplined long-running operation, not a casual freelance scam.
What the new research found
| Finding | Why it matters |
|---|---|
| luckyguys[.]site linked to DPRK fake IT worker payments | Gives defenders a concrete infrastructure lead to investigate |
| Domain resolved to 163.245.219[.]19 during analysis | Helps network teams hunt historical connections |
| Traffic seen from U.S. and Latvian residential IPs | Suggests use of proxy hosts or laptop farms |
| Heavy VPN use, especially Astrill and Mullvad | Shows how operators hide geography and appear local |
| Activity included platforms like Gmail and Workana | Shows the blend of normal work tools and malicious deception |
The table reflects Team Cymru’s public analysis and aligns with the broader warnings already issued by U.S. agencies about DPRK remote worker tradecraft.
What organizations should do now
- Treat remote hiring as both an HR risk and a security risk. Treasury and DOJ have both made clear these operations serve sanctions evasion and network access goals.
- Add extra identity verification for remote technical hires, especially when a candidate resists live video checks or pushes communication toward text-only channels.
- Review whether corporate devices used by remote employees show signs of being routed through residential proxy hosts or unusual VPN infrastructure.
- Hunt for connections to 163.245.219[.]19 and 216.158.225[.]144, which Team Cymru said should be flagged and investigated.
- Do not treat residential IP addresses as automatically safe. In this scheme, home connections can be part of the deception layer.
FAQ
It is a long-running operation in which North Korean operatives use stolen or fake identities to get hired as remote workers, then send revenue back to the regime and in some cases gain access to company systems and data.
They help the workers appear to connect from the United States or other trusted locations, which reduces suspicion during hiring and day-to-day work. Team Cymru said Astrill, Mullvad, and Proton VPN appeared prominently in the traffic it reviewed.
It is a setup where employer-issued laptops stay in the United States and are managed by facilitators, making the worker appear local even when the real operator is overseas. DOJ said two U.S. nationals were sentenced in April 2026 for helping run such farms.
Team Cymru recently published new infrastructure analysis, while Treasury, DOJ, and the FBI have all issued warnings or enforcement actions tied to DPRK remote IT worker schemes.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages