PCPJack cloud worm targets Docker, Kubernetes, Redis, and MongoDB credentials
PCPJack is a newly reported cloud-focused malware framework that targets exposed infrastructure, steals credentials, and spreads across additional systems. SentinelOne says the worm targets Docker, Kubernetes, Redis, MongoDB, RayML, and vulnerable web applications.
The malware is unusual because it does not deploy a cryptominer. Instead, it focuses on stealing cloud, developer, messaging, productivity, and financial credentials that can support fraud, spam, extortion, or resale.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
PCPJack also tries to remove traces of TeamPCP, a rival cloud threat group, before installing its own tools. This makes the campaign look like a turf war over already exposed or compromised cloud systems.
What makes PCPJack different
Most cloud malware tries to turn exposed servers into mining machines. PCPJack takes a different path by focusing on credentials and lateral movement.
SentinelOne says the framework collects secrets from cloud environments, containers, developer tools, productivity platforms, databases, and financial services. That gives attackers more options than one-time resource abuse.
The framework also tracks whether it successfully replaced TeamPCP infections. This shows the operator is not only looking for new victims, but also competing for control of systems that other attackers may already own.
At a glance
| Category | Details |
|---|---|
| Malware name | PCPJack |
| Main target | Exposed cloud and container infrastructure |
| Targeted services | Docker, Kubernetes, Redis, MongoDB, RayML, and vulnerable web apps |
| Main goal | Credential theft and cloud propagation |
| Cryptomining behavior | No cryptominer observed in the analyzed toolsets |
| Initial script | bootstrap.sh |
| Working directory | /var/lib/.spm/ |
| Exfiltration method | Encrypted data sent through attacker-controlled infrastructure and Telegram |
How the infection starts
The infection chain starts with a shell script named bootstrap.sh. The script prepares a Linux system, installs Python when needed, creates a working directory, downloads additional modules, and starts the main malware workflow.
The framework uses multiple Python modules for scanning, credential extraction, encryption, lateral movement, and cloud range collection. This modular design makes it easier for the operator to update one part without changing the whole framework.
PCPJack also runs cleanup steps against TeamPCP artifacts. SentinelOne says the actor’s focus on removing TeamPCP services suggests direct competition rather than simple opportunistic scanning.
What PCPJack steals
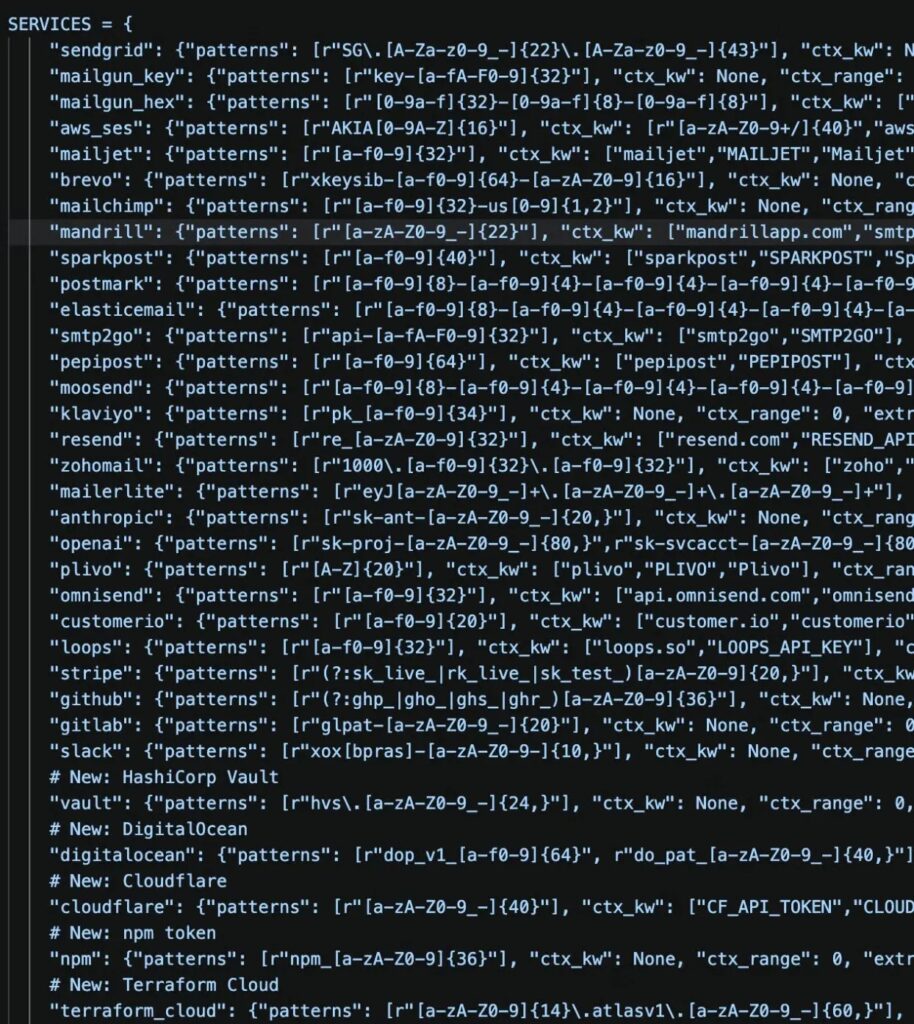
PCPJack searches for secrets across many services and file locations. It can collect SSH keys, cloud tokens, API keys, developer credentials, messaging tokens, and financial service credentials.
SentinelOne reported that the framework looks for data tied to services such as Slack, WordPress, OpenAI, Anthropic, cloud providers, HashiCorp Vault, Grafana Cloud, Discord, DigitalOcean, Google APIs, and 1Password.
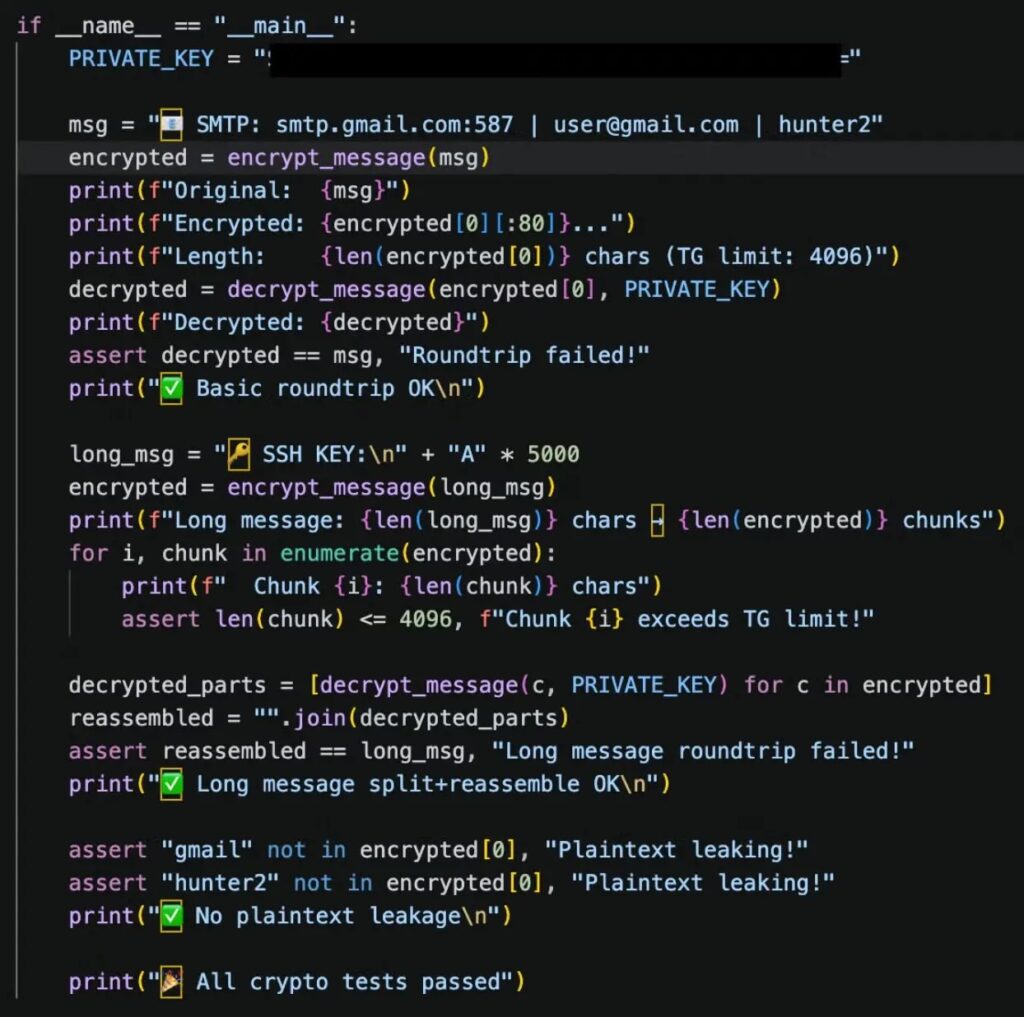
Stolen data is encrypted before exfiltration. The analyzed framework uses X25519 ECDH and ChaCha20-Poly1305, then breaks stolen data into smaller chunks before sending it through Telegram-related infrastructure.
Credential types at risk
- SSH private keys
- Cloud provider access tokens
- OpenAI and Anthropic API keys
- Slack tokens
- WordPress database credentials
- Docker and Kubernetes access material
- HashiCorp Vault secrets
- Grafana Cloud credentials
- Discord tokens
- 1Password-related data
- Cryptocurrency wallet files
How PCPJack spreads
The worm scans for exposed cloud services and vulnerable applications. It uses cloud IP ranges and external hostname data to find targets at scale.
SentinelOne says PCPJack downloads hostname data from Common Crawl parquet files and uses it for scanning. The approach can give the malware a very large pool of potential targets without hardcoding every address into its code.
Once it finds a target, the framework can attempt exploitation, harvest secrets, enumerate reachable infrastructure, and replicate itself to additional hosts through SSH, Kubernetes, Docker, Redis, RayML, or MongoDB paths.
Vulnerabilities linked to the campaign
| CVE | Product or area | Role in the campaign |
|---|---|---|
| CVE-2025-29927 | Next.js middleware | Authentication bypass used as an entry path |
| CVE-2025-55182 | React and Next.js | Server-side deserialization issue known as React2Shell |
| CVE-2026-1357 | WPVivid Backup | Unauthenticated file upload path |
| CVE-2025-9501 | W3 Total Cache | PHP injection path |
| CVE-2025-48703 | CentOS Web Panel | Shell injection path |
Sliver backdoor adds another layer
SentinelOne also found a Sliver-based backdoor on the attacker’s staging server. The files were compiled for x86_64, x86, and ARM systems, which suggests the operator wanted access across different cloud and container architectures.
The binaries used names such as update.bin, update-386.bin, and update-arm.bin. These names can blend into normal maintenance activity at a quick glance.
The backdoor gives the operator a more direct access option after the initial infection chain. That increases the risk for any environment where credentials, SSH keys, or orchestration access are already exposed.
Why Docker, Kubernetes, Redis, and MongoDB are high-risk targets
Exposed infrastructure services can become powerful entry points. A misconfigured Docker daemon can give attackers control over containers and host-level resources. Docker’s own documentation warns that remote daemon access should use secure controls such as SSH or TLS.
Kubernetes environments create similar risk when API access is weak. Kubernetes documentation explains that API access needs authentication and authorization controls because the API server sits at the center of cluster operations.
Redis and MongoDB can also expose valuable data or credentials when left open to the internet. Redis documentation highlights access control and secure deployment as key parts of protecting the service.
What security teams should monitor
- Unexpected files or scripts under /var/lib/.spm/.
- Execution of bootstrap.sh, monitor.py, worm.py, extractor.py, or similarly named Python modules.
- Connections to spm-cdn-assets-dist-2026 S3 infrastructure.
- Outbound traffic to cdn.cloudfront-js[.]com on ports 8443 or 7443.
- New Sliver-like binaries named update.bin, update-386.bin, or update-arm.bin.
- Unexpected use of /var/tmp/apt-daily-upgrade.
- Cloud scans against Docker, Kubernetes, MongoDB, Redis, and RayML ports.
- Enumeration of Kubernetes clusters or Docker daemons from unusual hosts.
- Large-scale access to environment variables and configuration files.
- Attempts to read SSH keys, cloud tokens, API keys, and developer secrets.
How organizations can reduce exposure
Organizations should start by reducing exposed services. Docker daemons, Kubernetes APIs, Redis, MongoDB, and RayML endpoints should not be reachable from the public internet unless there is a clear business need and strong access control.
Cloud teams should enforce multi-factor authentication, rotate exposed credentials, and reduce long-lived secrets. They should also move away from plaintext secrets in environment variables and configuration files where possible.
In AWS environments, IMDSv2 should be required to reduce metadata abuse risk. AWS documentation explains that instances can be configured to accept only IMDSv2 calls, causing IMDSv1 calls to fail.
Defensive checklist
- Require authentication on Docker, Kubernetes, Redis, MongoDB, and RayML endpoints.
- Protect Docker remote access with SSH or TLS.
- Apply Kubernetes RBAC and least-privilege service accounts.
- Disable public access to databases unless strictly required.
- Patch systems affected by the CVEs used in the campaign.
- Require IMDSv2 on AWS EC2 instances.
- Rotate cloud tokens, API keys, SSH keys, and application secrets after exposure.
- Use secret scanning in repositories, CI logs, containers, and environment files.
- Monitor for unusual Telegram, S3, and CloudFront-like outbound traffic.
- Audit cron jobs, systemd services, hidden directories, and unexpected Python virtual environments.
Why PCPJack matters
PCPJack shows that cloud attackers are moving beyond cryptomining. Credentials can produce longer-term value because attackers can sell access, launch spam, steal data, extort organizations, or move deeper into enterprise environments.
The TeamPCP cleanup behavior also shows how crowded exposed cloud infrastructure has become. Compromised systems may host more than one attacker, and new malware may remove older malware only to take over the same access.
For defenders, the lesson is direct: exposed cloud services are no longer just a performance or configuration issue. They are a fast path to credential theft, lateral movement, and wider compromise.
Summary
- PCPJack is a cloud-focused malware framework reported by SentinelOne.
- It targets Docker, Kubernetes, Redis, MongoDB, RayML, and vulnerable web applications.
- The malware removes TeamPCP artifacts before installing its own toolset.
- It focuses on credential theft instead of cryptomining.
- It can collect SSH keys, cloud tokens, API keys, Slack tokens, Vault secrets, and other sensitive data.
- It uses modular Python components, encrypted exfiltration, Telegram-related infrastructure, and Sliver backdoors.
- Organizations should lock down exposed services, rotate secrets, require IMDSv2, and monitor for unusual Python and cloud scanning activity.
FAQ
PCPJack is a cloud-focused malware framework that steals credentials, removes rival TeamPCP artifacts, and spreads across exposed infrastructure.
PCPJack targets Docker, Kubernetes, Redis, MongoDB, RayML, exposed cloud services, and vulnerable web applications.
No cryptomining payload was observed in the analyzed toolsets. SentinelOne says the campaign appears focused on credential monetization, fraud, spam, extortion, or resale.
The malware appears to remove TeamPCP artifacts so it can take over compromised systems for its own operator. This suggests competition between cloud threat actors.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages