PlugX USB worm resurfaces with multi-country spread and stealthy DLL sideloading

Researchers have documented a PlugX USB worm variant spreading across several countries through infected removable drives and DLL sideloading. Sophos X-Ops said it observed cases in Papua New Guinea, Ghana, Mongolia, Zimbabwe, and Nigeria, with the earliest sample in its dataset dating to August 2022.
PlugX itself is not new. It is a long-running remote access trojan associated in past reporting with China-linked threat activity, but this campaign drew attention because of its unusual geographic spread and its use of a C2 server that earlier research had only loosely connected to PlugX operations.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Sophos says the worm relies on DLL sideloading to launch the malware through a legitimate executable, then copies itself to USB drives in a way that makes the device look clean in normal Windows Explorer views. That combination helps it move quietly between systems, including networks with limited or no internet access.
How the infection chain works
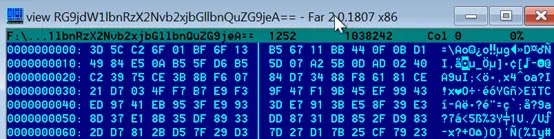
According to Sophos, the package includes a legitimate AvastSvc.exe, a malicious wsc.dll, and an encrypted payload. When a victim clicks what appears to be a removable-drive shortcut on the USB stick, the worm runs the renamed executable, which then sideloads the malicious DLL and starts the PlugX backdoor.

The USB trick is simple but effective. Sophos says the malware hides its files and folders with hidden and system attributes, stores them under RECYCLER.BIN, and drops a desktop.ini file so the folder looks like a real Recycle Bin. The visible item on the drive is a shortcut that imitates a normal disk icon, which lowers suspicion.
Researchers also said the worm collects files such as Word documents, Excel spreadsheets, PowerPoints, and PDFs, then stores them on the USB drive with base64-encoded names for later exfiltration. That behavior matches earlier reporting from Unit 42, which found related PlugX variants that infected USB devices and copied documents into hidden folders on removable media.
The Mustang Panda angle
Sophos said the tradecraft it observed aligns with PKPLUG activity, also known as Mustang Panda. The researchers stopped short of presenting a definitive actor attribution in the public write-up, but they said the techniques and infrastructure overlap strengthened the connection.
One infrastructure detail stands out. Sophos traced command-and-control traffic to 45.142.166.112, an IP that Unit 42 had referenced in 2019 as loosely connected to PlugX. Sophos said its newer findings strengthen the suspected link between that infrastructure and the operator behind this campaign.
This matters because USB-spreading malware can survive outside normal perimeter defenses. Sekoia’s 2024 work on the PlugX USB worm showed the malware continued to propagate globally even after parts of its infrastructure had gone quiet, partly because infected USB devices can sit offline for long periods before reaching a new machine.
PlugX USB worm at a glance
| Item | Details |
|---|---|
| Malware family | PlugX |
| Propagation | USB worm plus DLL sideloading |
| Observed countries in Sophos report | Papua New Guinea, Ghana, Mongolia, Zimbabwe, Nigeria |
| Earliest sample in Sophos dataset | August 2022 |
| Key visible lure | Fake removable-drive shortcut |
| Hidden storage path | RECYCLER.BIN with desktop.ini |
| Main document targets | .doc, .docx, .xls, .xlsx, .ppt, .pptx, .pdf |
| Suspected alignment | PKPLUG / Mustang Panda tradecraft alignment |
Source: Sophos X-Ops analysis.
What defenders should do now
- Disable AutoRun and AutoPlay for removable media. Sophos recommends reducing trust in USB-triggered execution paths because the worm uses shortcut-based deception on removable drives.
- Show hidden and system files on endpoints used for investigations or high-risk workflows. That can expose suspicious folders such as
RECYCLER.BINon USB devices - Monitor for DLL sideloading behavior involving unexpected copies of legitimate executables and adjacent rogue DLLs. This recommendation follows directly from the infection chain Sophos described.
- Hunt for unusual outbound traffic and document staging activity on hosts that interact with removable media. This is a practical step based on Sophos’ note that the worm encrypts and stages documents for exfiltration.
- Treat PlugX as a persistence and lateral-movement problem, not just a single-host infection. Sekoia’s sinkholing work showed the worm can keep spreading even when direct C2 visibility drops.
FAQ
No. PlugX is an established remote access trojan, but Sophos says this worm variant combines USB propagation, DLL sideloading, and a broad geographic footprint that made the campaign noteworthy.
The worm hides its files on the drive, creates a deceptive shortcut that looks like a removable disk, and executes a legitimate binary that sideloads a malicious DLL when the user clicks it.
Sophos says it targets common business documents, including Word, Excel, PowerPoint, and PDF files.
Sophos says the observed methods align with PKPLUG, also known as Mustang Panda, but the public report frames that as alignment rather than a flat definitive attribution.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages