Why VoidLink stands out from earlier AI malware claims
Earlier cases of AI-linked malware often involved low-quality scripts, recycled code, or amateur operators. Check Point says VoidLink is different because it appears to have been built almost entirely through AI-driven workflows while still reaching the level of a serious, structured malware project.
Researchers first believed a coordinated engineering team had built the framework. Later, leaked development artifacts changed that view. Check Point says those materials pointed instead to a single developer using ByteDance’s TRAE SOLO environment to plan, generate, refine, and test the codebase.
According to Check Point’s January 2026 research, the project reached a first functional implant in under a week. The same report says the codebase grew to more than 88,000 lines, which the company argues would previously have required much larger teams and much longer timelines.
What VoidLink can do on infected Linux systems
VoidLink targets modern Linux infrastructure rather than ordinary desktop systems. Check Point says it can detect major cloud environments, recognize Docker and Kubernetes, and adjust its behavior to match where it lands.
It also supports several stealth and persistence methods. Those include user-mode techniques such as LD_PRELOAD, plus kernel-level capabilities through loadable kernel modules and eBPF-based components. Elastic’s March 2026 analysis says the framework combines traditional LKM methods with eBPF to help hide activity and maintain persistence.
Researchers say the framework also supports multiple command-and-control methods, including HTTP, HTTPS, ICMP, and DNS tunneling, alongside a plugin system with more than 30 modules. That makes it flexible enough for long-term access, post-exploitation activity, and further expansion after the initial compromise.
VoidLink at a glance
| Area | What researchers found |
|---|---|
| Platform focus | Linux, cloud, container, and modern infrastructure environments |
| Key stealth methods | LD_PRELOAD, LKM rootkits, eBPF-based hiding techniques |
| Architecture | Modular framework with plugins and multiple C2 channels |
| Environment awareness | Detects cloud services, Docker, and Kubernetes |
| Development model | Check Point says AI handled most of the implementation work |
| Scale concern | A single actor may now build advanced tooling much faster than before |
How AI appears to have accelerated development
The most important detail may not be the malware itself, but the process behind it. Check Point says the developer did not rely on random prompts or one-off code generation. Instead, the actor appears to have used a more disciplined workflow based on structured specifications, sprint plans, and acceptance criteria.
Check Point links that process to what it describes as Spec Driven Development, where detailed written specifications guide implementation. In this case, the documents reportedly split the project into virtual teams and mapped out development goals, timelines, and deliverables before the AI agent generated much of the working code.
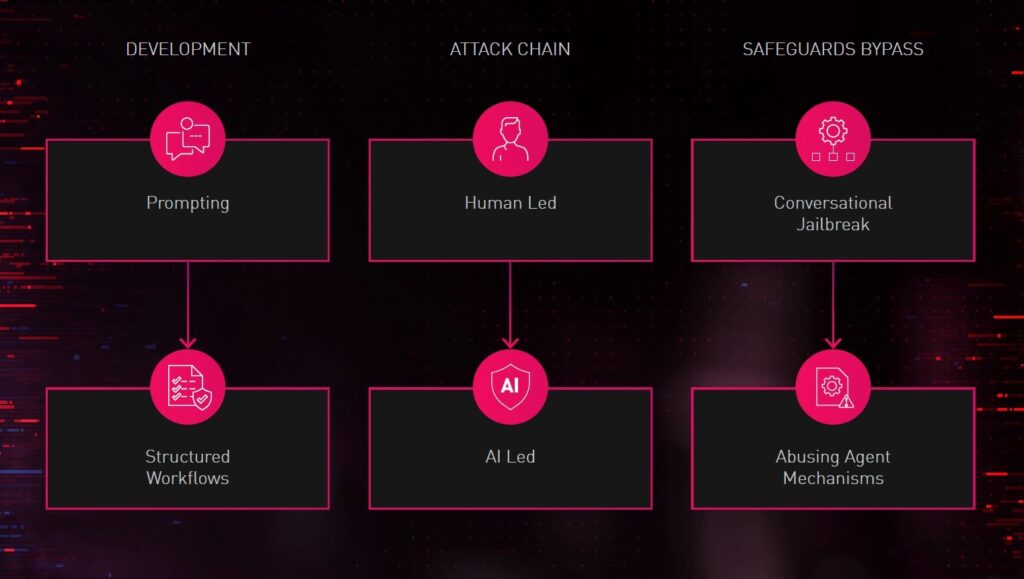
That is why VoidLink matters beyond one malware family. It suggests capable attackers can now combine domain knowledge with AI-assisted engineering practices to build complex malware faster, with more consistency, and with less manpower than before.
Why defenders should pay attention now
VoidLink does not just point to a new tool. It points to a new production model for malware. If a skilled individual can use AI to develop a cloud-aware Linux framework with rootkit and plugin support, then the barrier to building high-end offensive tooling has clearly dropped.
Security teams should also note an important nuance. Check Point said in January that it had not yet observed real-world infections tied to VoidLink at that stage, but the design and pace of development still made it significant. The risk comes from what the framework proves is now possible, even before broad deployment is seen.
Elastic’s later analysis adds weight to that concern. Its researchers say they examined source code, binaries, and deployment scripts for the rootkit subsystem, which gave them a deeper look at how the framework evolved across Linux targets and stealth techniques.
What organizations should do next
- Review Linux detections for unusual eBPF and kernel module behavior.
- Hunt for covert command channels that use ICMP or DNS tunneling.
- Tighten monitoring around Kubernetes, Docker, and cloud credential access.
- Audit AI tool governance inside development and corporate environments.
- Treat rapid, well-structured malware projects as potentially AI-assisted by default.
FAQ
Researchers describe VoidLink as a real malware framework discovered during development, not a fictional lab demo. Check Point said it was identified early and had not yet been observed in active attacks at the time of its January reporting.
It gives one of the clearest documented examples that AI can help one developer build advanced malware at a pace that once required larger teams. That changes how defenders should think about threat development speed and scale.
The reported framework focuses on Linux and cloud-native infrastructure. The larger lesson, however, applies much more broadly because the same AI-assisted workflow could be adapted to other malware projects over time.
Researchers say it blends modular design, multiple command channels, rootkit support, and environment-aware behavior. Elastic also points to its hybrid use of LKM and eBPF techniques in the rootkit subsystem.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages