xlabs_v1 botnet hijacks exposed Android devices to attack Minecraft servers
A new Mirai-based botnet called xlabs_v1 is hijacking Android and IoT devices that expose Android Debug Bridge on the internet, then using them in paid DDoS attacks against game servers.
Hunt.io researchers uncovered the operation after finding an exposed server in the Netherlands that contained the botnet operator’s toolkit. The files showed how xlabs_v1 infects ADB-exposed devices, connects them to command infrastructure, and measures their bandwidth for DDoS-for-hire pricing.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Minecraft servers appear to be a major target. The botnet includes a RakNet flood attack, a protocol family commonly tied to game traffic, and its distribution server exposed a bot binary on TCP port 25565, the default Minecraft server port.
What xlabs_v1 does
xlabs_v1 targets devices with ADB exposed on TCP port 5555. ADB is a legitimate Android development and debugging tool, but it should not be reachable from the public internet.
When attackers find an exposed device, they can push a payload through ADB and execute it without needing the owner to click a file. Hunt.io said the toolkit included multi-architecture binaries for ARM, MIPS, x86-64, ARC, and Android APK targets.
That broad build set allows the botnet to target many device types, including Android TV boxes, smart TVs, set-top boxes, routers, and low-cost IoT hardware that ships with debugging features left open or poorly secured.
At a glance
| Item | Details |
|---|---|
| Botnet name | xlabs_v1 |
| Malware family | Mirai-derived IoT botnet |
| Main infection vector | Exposed Android Debug Bridge on TCP port 5555 |
| Main target | Minecraft and other game servers |
| Business model | DDoS-for-hire |
| Operator handle | Tadashi |
| Researcher | Hunt.io |
| Infrastructure location | Offshore LC netblock in the Netherlands |
How researchers found the botnet
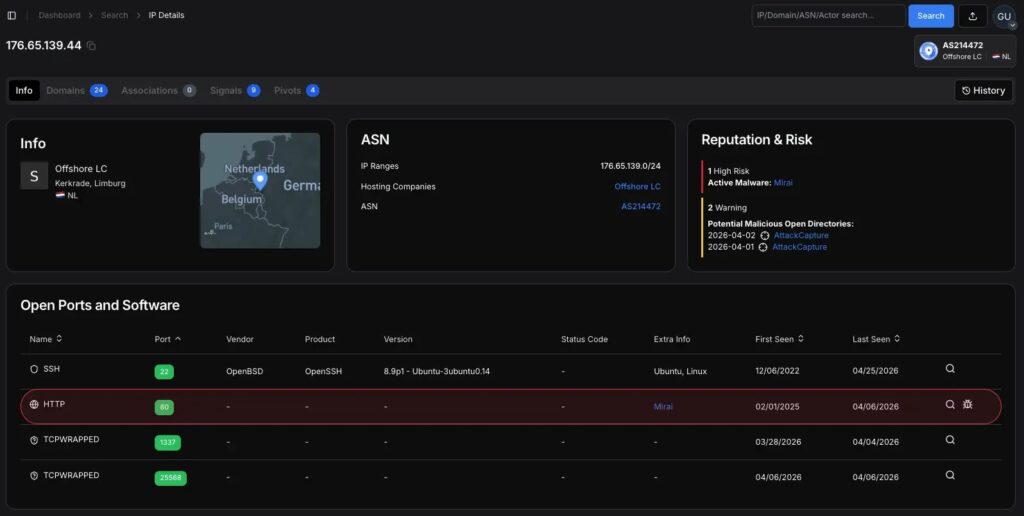
Hunt.io identified the operation in early April 2026 while monitoring bulletproof hosting networks. Its AttackCapture tool found an open directory on a Netherlands-hosted server at 176.65.139[.]44.
The directory had no authentication and exposed the operator’s working files. The captured set included two ELF binaries, infection payloads, proxy credentials, and a placeholder target file.
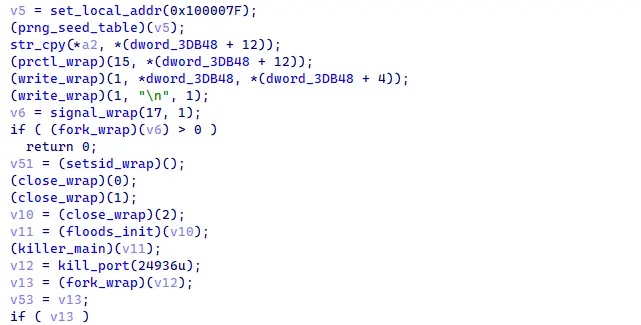
Researchers compared a stripped production ARM32 binary with an unstripped development build. That mistake exposed important internal details, including the botnet brand, command-and-control domain, operator handle, and authentication token.
Why Minecraft servers are in the crosshairs
Game servers are frequent DDoS targets because downtime is immediately visible. A short outage can disrupt players, damage a server’s reputation, and push small operators to pay for attacks or protection.
xlabs_v1 includes 21 flood variants across TCP, UDP, and raw protocols. Hunt.io specifically highlighted RakNet and OpenVPN-shaped UDP floods as part of the attack set.
The RakNet capability and the use of TCP port 25565 for bot distribution strongly point to game-server disruption as the botnet’s main commercial purpose.
How the infection works
After landing on a device, the bot drops into the /data/local/tmp/ directory and starts running in the background. That location is commonly writable on Android systems and often abused by malware using ADB access.
The bot then hides signs of its launch by capturing an infection-vector argument and clearing it from process listings. It also overwrites its process name with /bin/bash to look less suspicious during a quick check.
After that, it detaches from the terminal, closes standard input and output handles, and continues as a background process. This does not make it invisible to security tools, but it can hide the infection from casual inspection.
Key technical behavior
| Behavior | Purpose |
|---|---|
| ADB abuse on TCP 5555 | Initial access to exposed Android and IoT devices |
| Payload drop in /data/local/tmp/ | Runs malware from a writable Android directory |
| Process name changed to /bin/bash | Helps the bot blend into process listings |
| ChaCha20-protected string table | Hides internal strings such as C2 details and tokens |
| 8,192 Speedtest sockets | Measures upstream bandwidth for pricing infected devices |
| 21 flood variants | Supports different DDoS attack methods |
The botnet acts like a commercial service
xlabs_v1 does more than infect devices and wait for commands. It profiles each infected device’s network capacity by opening 8,192 parallel sockets to a nearby Speedtest server.
Hunt.io said this bandwidth profiling helps the operator place bots into pricing tiers. A fast home fiber device can be worth more to a DDoS-for-hire customer than a slow connection.
This shows that the operator is managing the botnet like a rentable attack platform. The malware’s goal is not persistence for espionage. It is reliable traffic generation for customers who want to knock services offline.
Infrastructure and command channel
The operation was hosted inside a single bulletproof /24 netblock announced by Offshore LC in the Netherlands. Hunt.io said the same netblock contained command, staging, distribution, and co-located Monero cryptojacking infrastructure.
The bot connects to xlabslover[.]lol over TCP port 35342 and sends a registration message with host details, CPU count, RAM size, and an authentication token.
If the outbound connection fails, the malware can open a fallback listener on TCP port 26721 and try several iptables paths to keep a re-entry channel available.
What defenders should monitor
- Internet-facing Android devices with TCP port 5555 exposed.
- Unexpected files in /data/local/tmp/, especially arm7.
- /bin/bash processes running without a normal controlling terminal.
- Outbound connections to xlabslover[.]lol.
- Outbound traffic to TCP port 35342.
- Unexpected listeners on TCP port 26721.
- Large bursts of Speedtest-related connections from Android or IoT devices.
- Traffic to pool[.]hashvault[.]pro from devices that should not mine cryptocurrency.
Why exposed ADB is a serious problem
ADB gives developers powerful control over Android devices. When it is exposed to the internet, attackers can turn that same control into remote malware installation.
Many infected devices may not look like traditional computers. Android TV boxes, smart TVs, routers, and cheap IoT systems often run quietly for months without close security monitoring.
That makes them useful to DDoS operators. Owners may not notice the infection until their internet connection slows down, their device becomes unstable, or their network appears in abuse reports.
Recommended actions
- Disable ADB on all Android and IoT devices unless it is actively needed.
- Never expose ADB on TCP port 5555 to the public internet.
- Block inbound access to TCP 5555 at routers, firewalls, and cloud security groups.
- Restart and factory reset devices that show signs of compromise.
- Update firmware on Android TV boxes, routers, and smart devices where updates are available.
- Restrict outbound traffic from IoT networks to only required destinations.
- Segment smart TVs, set-top boxes, and IoT devices away from business systems.
- Monitor for abnormal upload spikes and repeated outbound connection bursts.
Impact for Minecraft server operators
Minecraft server owners should treat xlabs_v1 as another sign that game infrastructure remains a profitable DDoS target. The botnet’s design shows direct interest in game-server flooding rather than general disruption alone.
Small server operators may face the greatest pressure because they often rely on basic hosting plans or consumer-grade DDoS protection. Attackers can rent traffic from botnets like this to overwhelm those setups.
Server owners should use reputable DDoS-protected hosting, keep firewall rules tight, monitor traffic baselines, and prepare failover or filtering plans before attacks begin.
What this means for defenders
xlabs_v1 is not the most advanced botnet, but it is organized enough to create real disruption. Its operator built pricing logic, multi-architecture payloads, many flood types, and competition-killing behavior into the malware.
The exposed staging server also shows how quickly a single operational mistake can reveal a cybercriminal service. Hunt.io used one leaked development build to reconstruct the botnet’s targets, infrastructure, command flow, and operator identity markers.
For defenders, the priority is simple. Remove exposed ADB, monitor IoT traffic, isolate smart devices, and treat unusual outbound bandwidth from Android hardware as a possible sign of botnet abuse.
FAQ
xlabs_v1 is a Mirai-derived IoT botnet used for DDoS-for-hire attacks, with a strong focus on Minecraft and other game servers.
It targets Android and IoT devices with Android Debug Bridge exposed on TCP port 5555, then pushes and runs malware through that access.
Android TV boxes, smart TVs, set-top boxes, routers, and IoT devices are at risk if ADB is enabled and exposed to the internet.
The botnet includes game-focused flood capabilities, including a RakNet flood variant, and its infrastructure uses the default Minecraft server port for distribution.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages