Rust-based VENON malware hits 33 Brazilian banks with stealthy credential-theft overlays
A newly disclosed Windows banking trojan called VENON is targeting users in Brazil, and researchers say it marks a notable shift in the region’s cybercrime playbook because the malware is written entirely in Rust, not Delphi. ZenoX, the Brazilian security firm that published the research, says VENON monitors banking apps and websites, then launches credential-stealing overlays only when a victim opens a targeted service.
The malware does not just go after traditional banks. ZenoX says VENON watches 33 targets across banks, fintechs, government portals, crypto exchanges, and wallet apps. That list includes Itaú, Santander Brasil, Caixa, Banco do Brasil, Nubank, Banco Inter, BTG Pactual, Binance, Coinbase, Kraken, MetaMask, Trust Wallet, Ledger Live, and others.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What makes this campaign stand out is not only the language choice. ZenoX says the malware combines classic Latin American banking trojan behavior, such as overlays and active window monitoring, with a more modern toolchain built in Rust and backed by heavy evasion. The researchers also raise the possibility that generative AI helped the developers recreate known banking trojan features in a new language, though they frame that as a hypothesis rather than a confirmed fact.
ZenoX says VENON first appeared in February 2026 during threat hunting. During static analysis, the team found no Delphi code at all and identified 88 Rust crate dependencies instead. The company says that makes VENON potentially the first Brazilian banking RAT developed entirely in Rust.
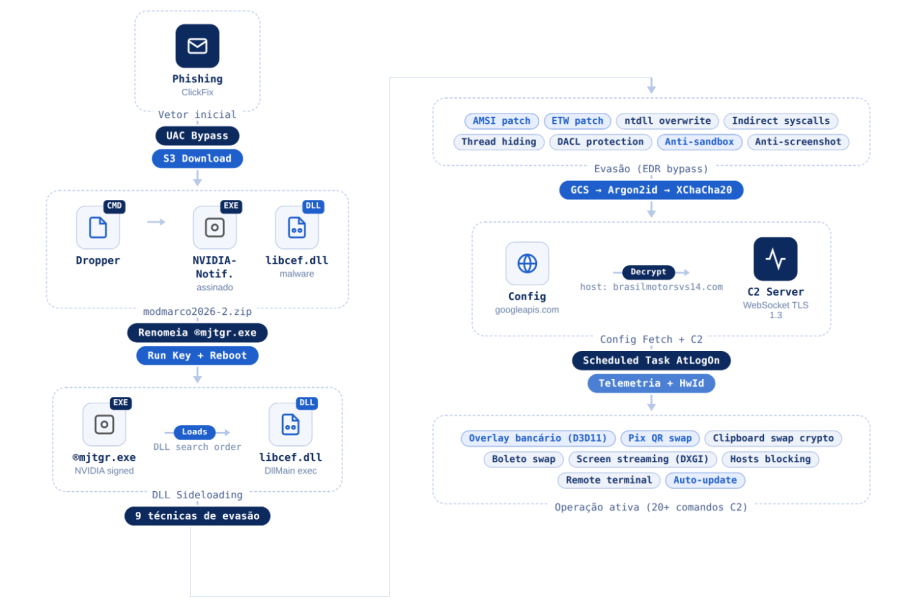
The infection chain starts with DLL sideloading. ZenoX says the malware abuses a legitimate NVIDIA binary, NVIDIANotification.exe, to load a malicious libcef.dll by taking advantage of Windows DLL search order. The researchers say they also observed a rise in ClickFix campaigns using the same binary pair, but they stopped short of calling that delivery path fully confirmed for this sample.
Once the malicious DLL runs, VENON tries hard to stay hidden. ZenoX says it executes nine anti-analysis and evasion steps before beginning its core activity, including anti-sandbox checks, indirect syscalls, ETW bypass, AMSI bypass, thread hiding, and overwriting the in-memory .text section of ntdll.dll with a clean copy from disk.
After that, the malware fetches a remote configuration from Google Cloud Storage, with a fallback domain if needed. ZenoX says the config uses layered protection that includes Base64, Argon2id, and XChaCha20-Poly1305, and ultimately reveals a command-and-control host used by the operators. The company says this reflects a more mature design than earlier versions of the same RAT, which reportedly relied on weaker cryptography.
Persistence comes next. According to ZenoX, VENON installs a scheduled task called “NVIDIA Notification Service,” connects to its C2 over TLS 1.3 via WebSockets, and identifies victims using a hardware-based ID derived from the computer name and drive serial number. The malware then waits for one of its targets to appear before it shows a fake overlay or triggers other theft logic.
One of the more unusual features targets Itaú specifically. ZenoX says VENON contains two VBScript blocks that hijack shortcuts for the Itaú desktop application and redirect victims to an attacker-controlled web page while keeping the bank’s icon to avoid suspicion. The malware also supports an uninstall step that can restore the original shortcuts, which suggests the operators can clean up after themselves remotely.
The broader backdrop matters here. Banking malware in Brazil already spreads through aggressive social engineering and trusted messaging channels. Separate reporting from Blackpoint Cyber on the SORVEPOTEL worm shows attackers have abused authenticated WhatsApp Web sessions to push malicious lures that ultimately install banking malware such as Astaroth. That does not tie SORVEPOTEL directly to VENON, but it shows how active and adaptive the Brazilian malware ecosystem remains.
What VENON does
| Feature | What researchers found |
|---|---|
| Malware type | Windows banking RAT / banking trojan |
| Programming language | Fully compiled in Rust |
| Main goal | Steal credentials through fake overlays and targeted fraud logic |
| Initial execution | DLL sideloading via legitimate NVIDIANotification.exe |
| Main payload | Malicious libcef.dll |
| Evasion | Anti-sandbox, AMSI bypass, ETW bypass, indirect syscalls, thread hiding, ntdll text overwrite |
| Config retrieval | Google Cloud Storage with fallback domain |
| Persistence | Scheduled task named “NVIDIA Notification Service” |
| Network channel | TLS 1.3 WebSocket C2 |
| Special trick | Itaú shortcut hijacking with remote uninstall support |
All of these details come from ZenoX’s March 10 research report on VENON.
Why this malware matters
- It shows a clear move away from the Delphi-heavy malware tradition in Latin America.
- It targets a broad set of financial and crypto services, not just one or two banks.
- Its attack chain uses multiple stealth features before it begins visible fraud activity.
- The AI angle remains a researcher assessment, but it suggests criminals may use generative tools to speed up malware rewrites and feature expansion.
- The malware includes operator-friendly controls such as shortcut restoration, which points to a more disciplined intrusion workflow.
Target categories highlighted by ZenoX
- Traditional banks, including Itaú, Santander Brasil, Caixa, Banco do Brasil, Nubank, Banco Inter, Sicoob, Sicredi, Banco Original, and Safra.
- Fintech and payment services, including PagBank, PicPay, Mercado Pago, and Bling ERP.
- Government services, including Receita Federal.
- Crypto exchanges and wallets, including Binance, Coinbase, Kraken, Bybit, MetaMask, Trust Wallet, Phantom, Ledger Live, Rabby Wallet, and Cake DeFi.
FAQ
VENON is a Windows banking trojan that ZenoX says was developed entirely in Rust and designed to steal credentials from Brazilian banking and crypto targets using overlays, shortcut hijacking, and remote command-and-control.
Most well-known Latin American banking trojans have relied heavily on Delphi. ZenoX says VENON contains no Delphi code and may be the first Brazilian banker RAT built fully in Rust.
No. ZenoX says the code structure and backend patterns suggest AI-assisted development, but the company presents that as a hypothesis based on technical indicators, not as a confirmed fact.
ZenoX says the confirmed execution chain uses DLL sideloading through a legitimate NVIDIA binary and a malicious libcef.dll. The company also observed related ClickFix activity, but did not present that delivery path as fully confirmed for this exact sample.
ZenoX says the malware monitors 33 services across banks, fintechs, government portals, crypto exchanges, and wallet apps.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages