Fake Proton VPN sites and gaming mods spread NWHStealer in new Windows malware campaign

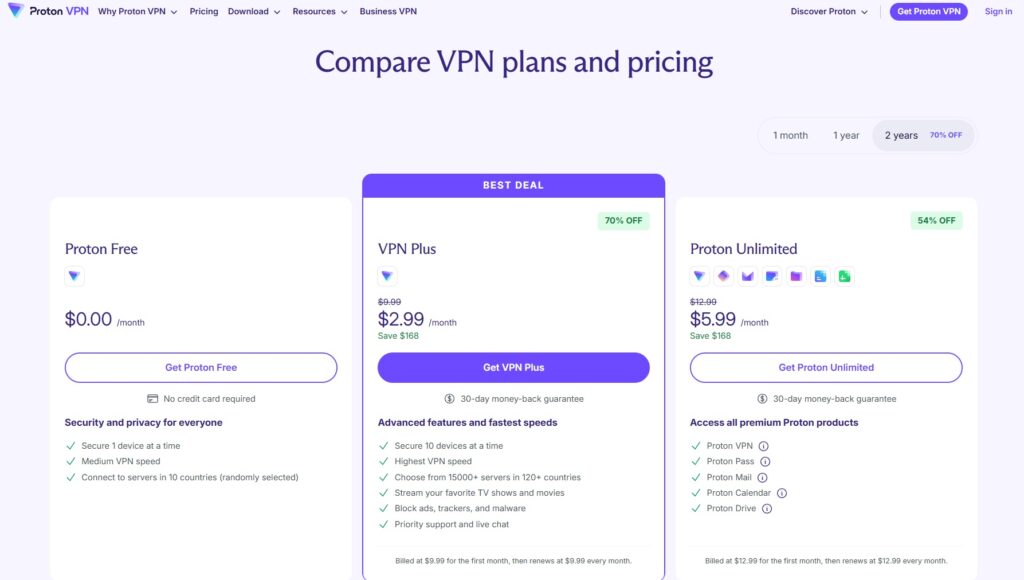
A new malware campaign is pushing NWHStealer through fake Proton VPN sites, gaming mods, hardware tools, and download links shared across GitHub, GitLab, SourceForge, MediaFire, and YouTube. Malwarebytes says the stealer targets browser data, saved passwords, and cryptocurrency wallet information on Windows systems.
What makes this campaign dangerous is the delivery method. Attackers are not leaning on mass spam or crude phishing alone. They are hiding malware inside software people already want, which raises the odds that victims will download and run the files themselves.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Malwarebytes researcher Gabriele Orini says the campaigns use several wrappers and loaders before the final stealer lands on the device. In some cases, the malware injects itself into legitimate Windows processes such as RegAsm, while other chains use MSI packages or Node.js as the first stage.
Trusted platforms make the lure more convincing
The fake software covers a wide range of popular tools. Malwarebytes says the lures include fake VPN installers, hardware utilities such as OhmGraphite, Pachtop, and Sidebar Diagnostics, plus gaming cheats and mods including Xeno.
One unusual part of the campaign involves onworks[.]net, a free web hosting provider that Malwarebytes found serving malicious ZIP archives from its download section. Files with names such as HardwareVisualizer_1.3.1.zip and Sidebar Diagnostics-3.6.5.zip looked legitimate but carried code that launched the infection chain after execution.
The fake Proton VPN angle stands out as well. Malwarebytes says some malicious ZIP files used DLL hijacking, where a file posing as a WinRAR executable loaded a rogue WindowsCodecs.dll file that unpacked the next malware stages.
How the infection chain works
In one observed chain, the malware hides inside a legitimate-looking executable such as HardwareVisualizer.exe. When the victim runs it, the loader checks for analysis tools, decrypts strings, resolves Windows API functions, and then decrypts the next payload with AES-CBC through BCrypt APIs. Malwarebytes says the samples also include junk code to slow analysis and frustrate automated tools.
In another chain, the malicious DLL decrypts an embedded file called runpeNew.dll, which then uses process hollowing to inject the final payload into a running Windows process like RegAsm.exe. Malwarebytes says that stage uses low-level APIs such as NtProtectVirtualMemory and NtAllocateVirtualMemory.
Once NWHStealer gains a foothold, it uses PowerShell to create hidden folders in LOCALAPPDATA, adds those folders to Microsoft Defender exclusions, and forces a Group Policy update. The malware also creates scheduled tasks to run at logon with elevated privileges.
What NWHStealer steals
Malwarebytes says NWHStealer targets data from Edge, Chrome, Opera, Brave, Chromium, and Firefox. It also checks more than 25 folders and registry keys linked to cryptocurrency wallets, which can give attackers a path to account theft and financial loss.
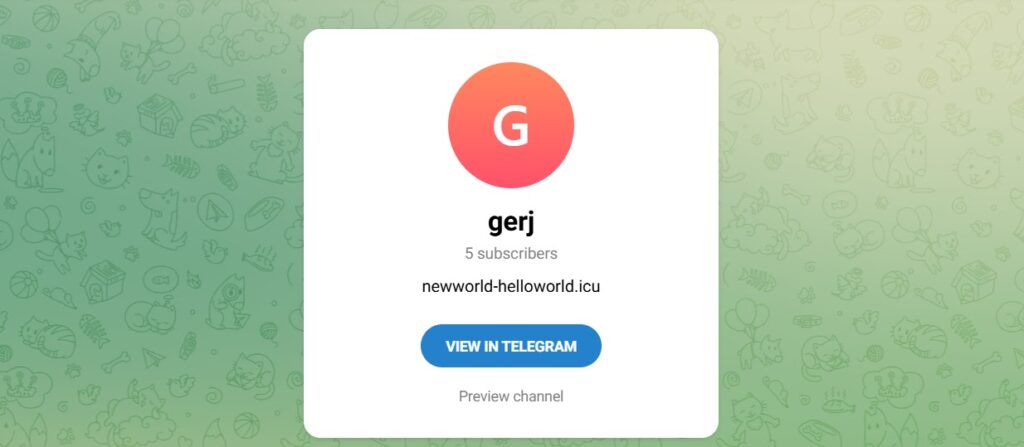
The malware encrypts stolen data with AES-CBC before sending it to its command-and-control server. If that main server goes offline, it can fetch a fresh domain through a Telegram-based dead drop resolver, which helps the attackers keep the campaign running even when infrastructure changes.
Malwarebytes also says the malware uses a known CMSTP UAC bypass. It creates a random INF file in the temp folder and abuses cmstp.exe to elevate privileges without showing a visible prompt.
NWHStealer campaign at a glance
| Item | Verified detail |
|---|---|
| Malware family | NWHStealer |
| Main targets | Browser data, saved credentials, cryptocurrency wallet information |
| Delivery lures | Fake Proton VPN sites, gaming mods, hardware utilities, GitHub, GitLab, MediaFire, SourceForge, YouTube links |
| Execution methods | Self-injection, process injection into RegAsm, MSI wrappers, Node.js loaders |
| Persistence | Scheduled tasks, hidden LOCALAPPDATA folders, Defender exclusions |
| Evasion and privilege abuse | Junk code, process hollowing, CMSTP UAC bypass |
| C2 resilience | Telegram-based dead drop resolver |
Source sample provided by the user:
How to reduce your risk
- Download software only from official vendor sites.
- Treat GitHub, SourceForge, MediaFire, and similar platforms as delivery channels, not proof of trust.
- Check the publisher and digital signature before you run any installer.
- Avoid software links dropped in YouTube descriptions or comments unless you can verify the developer independently.
- Scan ZIP archives and executables before opening them.
- Watch for tools that ask for elevated rights without a clear reason.
- Keep browser-stored passwords and crypto wallets to a minimum on general-use PCs.
FAQ
NWHStealer is a Windows information stealer that collects browser data, saved passwords, and cryptocurrency wallet information. Malwarebytes documented multiple campaigns distributing it in April 2026.
It spreads through fake software downloads and malicious links tied to fake VPN sites, gaming mods, hardware utilities, code-hosting pages, file-sharing sites, and YouTube videos.
Malwarebytes says it targets Edge, Chrome, Opera, Brave, Chromium, and Firefox.
Because the malware hides inside tools users actively search for and trust, instead of relying only on obvious phishing emails. That makes the initial download look more normal and lowers suspicion.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages