Email-borne worm surge hit industrial control systems worldwide in late 2025

A sharp rise in email-borne worm activity hit industrial control systems in the fourth quarter of 2025, driven largely by a campaign spreading Backdoor.MSIL.XWorm through phishing emails. Kaspersky ICS CERT said the percentage of ICS computers on which worms were blocked rose 1.6 times to 1.60% in Q4 2025, with increases recorded in every region of the world.
The campaign stood out because the malware had not appeared on ICS computers in the previous quarter, then suddenly showed up across all regions in just one reporting period. Researchers linked that jump to global phishing activity involving XWorm and a broader wave of malicious emails aimed at industrial environments.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This matters because email still gives attackers a simple way into sensitive operational environments. Once a malicious attachment lands on a system that connects to industrial processes, the impact can stretch well beyond a single infected PC.
XWorm drove the spike
Kaspersky said many of the blocked threats were tied to Backdoor.MSIL.XWorm, a worm and backdoor designed to persist on infected systems and give attackers remote control. The company said the malware spread through phishing emails and appeared across ICS environments worldwide during Q4 2025.
Researchers also tied the activity to phishing campaigns known since 2024 as “Curriculum-vitae-catalina.” In those attacks, threat actors disguised malware as job applications and sent messages with subjects such as “Resume” or “Attached Resume,” often targeting HR staff, recruiters, and employees involved in hiring.
The malicious attachment typically posed as a resume file, but it actually delivered malware when opened. Kaspersky said the campaign relied on obfuscation techniques that helped the payload get past basic defenses and helped explain why the threat surged so suddenly in Q4.
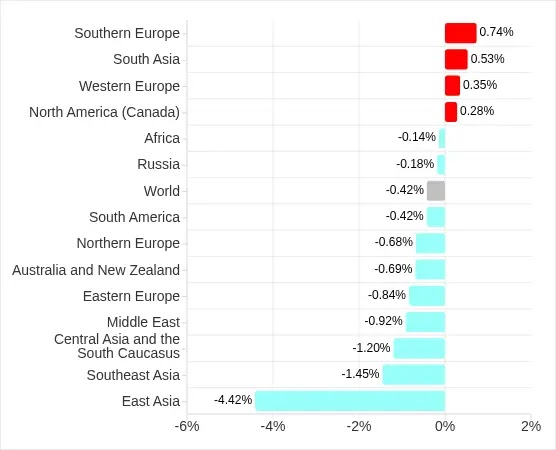
The spread was global, but regions saw different levels of impact
Kaspersky said the first wave hit in October 2025 and affected Russia, Western Europe, South America, and North America, especially Canada. A second wave followed in November and expanded to more regions before the activity slowed in December.
At the regional level, the percentage of ICS computers on which worms were blocked ranged from 0.32% in Northern Europe to 3.72% in Africa. The top three regions for worm detections were Africa, the Middle East, and Central Asia with the South Caucasus.
Southern Europe saw the sharpest increase, with worm detections rising 2.16 times. Kaspersky said that jump aligned with the region’s already high rate of email-related threats against ICS systems.
Why industrial networks remain exposed
The broader email threat picture stayed elevated even though the percentage of ICS computers on which email client threats were blocked fell to 2.76% in Q4 2025. Kaspersky still called that the second-highest quarterly value in three years, which shows that email remains a major delivery channel for threats in operational technology environments.
The report also noted that the main categories of threats from email clients blocked on ICS computers in Q4 2025 were malicious scripts and phishing pages, spyware, and malicious documents. Worms also rose within that mix, which points to a shift in how attackers tried to gain footholds.
In Africa, Kaspersky said email client threats on ICS computers reached 4.17% in Q4 2025. The company also noted that removable media remained another infection path there, which shows how some regions face layered risks from both phishing and offline spread methods.
What the malware can do after infection
According to the report, XWorm gives attackers remote control over infected systems and is built to maintain persistence after compromise. That makes it more dangerous than a one-time downloader because it can hold access and support later actions inside the network.

Kaspersky said the malware used obfuscation and layered delivery methods to hide its behavior. That helped it slip through defenses during mass phishing campaigns and likely contributed to its spread across industrial environments.
For ICS and OT operators, the takeaway is straightforward. A fake resume or similar attachment can serve as the starting point for remote access inside an environment that may connect to critical systems and industrial processes.
Key figures
| Metric | Figure |
|---|---|
| Global percentage of ICS computers with worms blocked in Q4 2025 | 1.60% |
| Change from previous quarter | 1.6x increase |
| Lowest regional worm rate | 0.32% in Northern Europe |
| Highest regional worm rate | 3.72% in Africa |
| Region with steepest increase | Southern Europe, up 2.16x |
| Global percentage of ICS computers with email client threats blocked in Q4 2025 | 2.76% |
Source for figures: Kaspersky ICS CERT and Securelist.
What organizations should do
- Block executable attachments at the email gateway before they reach end users. Kaspersky specifically warned about malicious files disguised as resumes.
- Train HR teams, recruiters, and staff who handle hiring messages to treat unsolicited attachments as high-risk. Those users were a key target in the “Curriculum-vitae-catalina” campaigns.
- Tighten controls on removable media, especially in regions where USB-based spread still plays a role.
- Keep ICS endpoints updated and use behavior-based detection, since the report says the campaigns relied on obfuscation that can weaken signature-only defenses.
FAQ
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages