Pushpaganda used Google Discover and AI-written clickbait to push malicious notifications

A new threat campaign called Pushpaganda abused Google Discover to push deceptive stories into the feeds of Android and Chrome users, then tricked them into enabling browser notifications that delivered scareware and scam luses. HUMAN’s Satori Threat Intelligence and Research Team says the operation relied on AI-generated content, aggressive SEO tactics, and deceptive site behavior.
The campaign was not just about fake articles. HUMAN says the real goal was to turn real users into a source of invalid traffic and ad revenue by pushing them into persistent notification subscriptions and repeated visits to actor-controlled domains. At its peak, the operation generated about 240 million bid requests tied to 113 domains in a single seven-day period.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Google says it has already deployed a fix to stop this kind of low-quality, manipulative content from surfacing in Discover. In a statement reported by The Hacker News, the company said it had launched the fix before learning of the report and pointed to its existing spam-fighting systems and policies.
How Pushpaganda got into Discover
HUMAN says the actors created 113 domains and used AI to generate sensational articles and images meant to attract clicks at a glance. Those stories then appeared in Google Discover feeds through either advanced SEO or paid placement, although the researchers said they could not confirm which route was used in every case.
The campaign first focused on India, then expanded to Australia, the United States, and other regions. The Hacker News, citing the HUMAN report and follow-up reporting, also said the operation reached Canada, South Africa, and the U.K.
That distribution channel matters because Discover sits in a high-visibility spot. HUMAN describes it as a personalized news stream shown across Google properties, including Android home screens and blank Chrome tabs, which gave the actors access to users outside the usual email or SMS scam pipeline.
One click turned into persistent scareware
After users clicked a deceptive story, they landed on an actor-controlled page that immediately triggered a notification prompt. HUMAN says many users clicked “Allow” either to get past the pop-up or because they believed it was required to access the content.
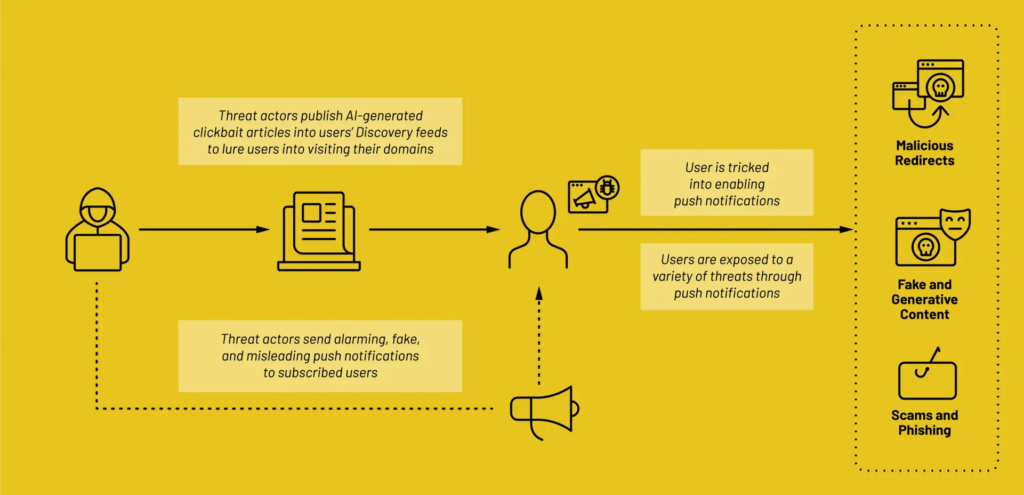
Once a user subscribed, the site could push notifications directly at the operating-system level. HUMAN says those messages bypassed traditional ad blockers and often used fear-heavy themes such as fake arrest warrants, false missed calls from family members, and bogus financial alerts.
The notifications had little or nothing to do with the original article. Clicking one often sent the user to another actor-controlled domain, which then repeated the cycle and expanded the operators’ traffic and monetization chain.
The ad fraud angle made the scheme more profitable
HUMAN says some Pushpaganda domains used deceptive buttons labeled things like “Apply Now,” “Claim Now,” or “Join WhatsApp.” Instead of completing the promised action, those buttons opened new active tabs while a background tab rotated through more Pushpaganda-linked pages.
That tab-rotation behavior quietly loaded ads and inflated session activity, making the traffic look more valuable to advertising systems than it really was. HUMAN says the result was more ad impressions and revenue from users who never meant to engage with those pages in the first place.
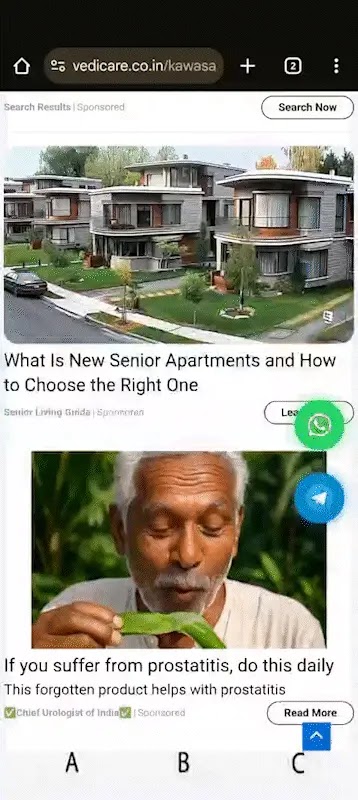
Researchers also saw deepfake-style creative embedded in ads on those domains, including content that appeared to misuse the likeness of celebrities and medical professionals. That added another layer of trust abuse on top of the Discover manipulation and push-notification scam chain.
Pushpaganda at a glance
| Item | What researchers found |
|---|---|
| Campaign name | Pushpaganda |
| Primary lure | AI-generated clickbait in Google Discover |
| Main abuse path | Notification prompts on actor-controlled domains |
| Scale observed | 113 associated domains |
| Peak activity | About 240 million bid requests in 7 days |
| Initial geography | India |
| Later spread | Australia, U.S., and other regions |
The table above reflects HUMAN’s report and follow-up reporting from The Hacker News.
What users should do now
- Review browser notification permissions and remove any domain you do not recognize. HUMAN specifically recommends revoking access for suspicious sites.
- Avoid clicking “Allow” on notification prompts from sites you did not intend to trust.
- Treat urgent legal, banking, tax, or family-alert notifications from random sites as social engineering attempts.
- On Chrome for Android, check notification permissions under Settings, then Site settings, then Notifications. This step appears in the sample you shared and matches the browser-based mitigation HUMAN recommends.
FAQ
Pushpaganda is a scam and ad-fraud operation that used AI-generated content and Google Discover exposure to trick users into enabling malicious browser notifications.
Yes. Google told The Hacker News it had already launched a fix for the spam issue and said it uses spam-fighting systems and policies to keep manipulative content out of Discover.
The strongest confirmed description is scareware, social engineering, and ad fraud delivered through notification abuse. Some follow-on pages may have pushed additional scams, but the primary public reporting centers on malicious notifications, fake alerts, and traffic monetization.
HUMAN’s Satori Threat Intelligence and Research Team identified the campaign. The researchers named in the report are Louisa Abel, Vikas Parthasarathy, João Santos, and Adam Sell.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages